
From US Spies to Crypto Thieves: How iPhone Hacking Tools Go Rogue
A sophisticated iPhone hacking toolkit possibly created for the US government has traveled from Russian spies targeting Ukrainians to Chinese cybercriminals stealing cryptocurrency, infecting 42,000 devices.
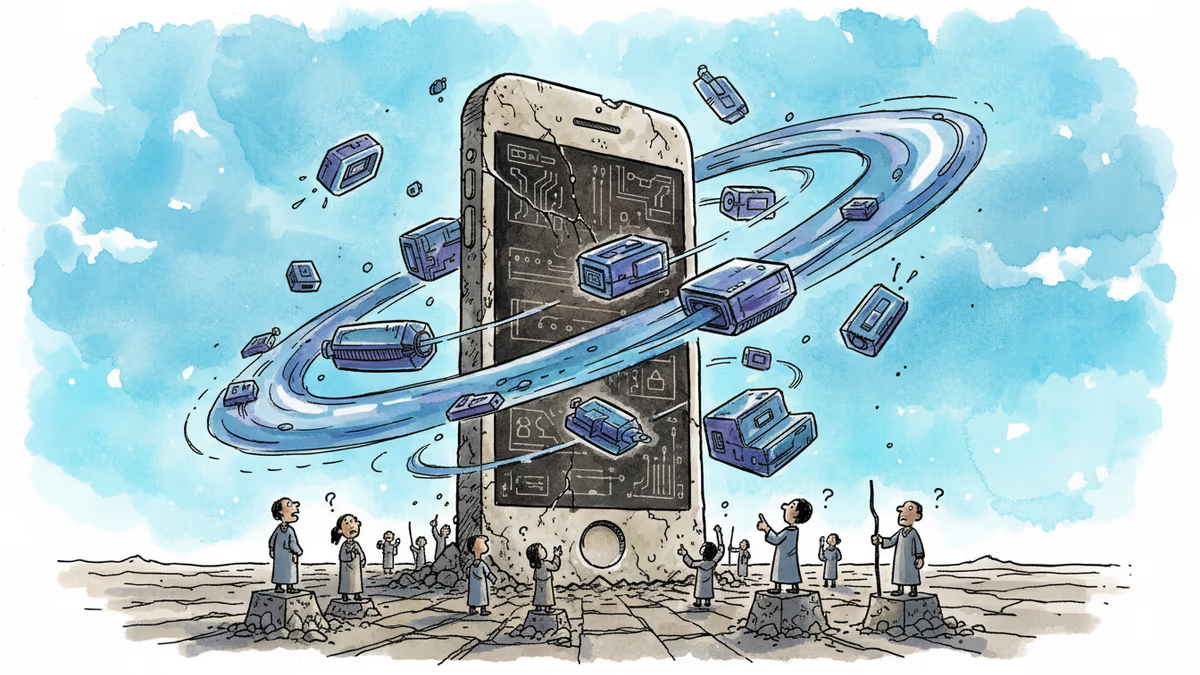
42,000 iPhones Hacked Just by Visiting a Website
Google's Tuesday report reads like a cybersecurity thriller. A toolkit called "Coruna" exploits 23 distinct iOS vulnerabilities to completely hijack iPhones when users simply visit an infected website. But the real shock isn't the technical sophistication—it's the journey this code has taken from what appears to be a US government contractor's hands to Russian spies and Chinese cryptocurrency thieves.
This isn't just another hacking story. It's a case study in how digital weapons escape their creators' control.
Three Lives of a Digital Weapon
Google tracked Coruna through three distinct campaigns, each more troubling than the last.
February 2024: The first sighting involved what Google diplomatically calls a "customer of a surveillance company." Translation: likely a government agency using it for targeted espionage.
July 2024: Russian operatives embedded the code in Ukrainian websites, disguising it as harmless visitor-counting tools. Anyone browsing Ukrainian sites became a potential target in what appears to be a state-sponsored espionage campaign.
Late 2024: Chinese-speaking cybercriminals deployed Coruna on cryptocurrency and gambling sites, purely for profit. Their goal? Drain victims' crypto wallets and steal personal data.
Each iteration reveals how quickly sophisticated state tools can proliferate beyond their intended use.
The American Fingerprints
iVerify, the mobile security firm that analyzed Coruna's criminal variant, found compelling evidence of US origins. The code bears hallmarks of English-speaking developers and required millions of dollars to develop—resources typically available only to well-funded government operations.
Most tellingly, Coruna shares components with "Operation Triangulation," the 2023 attack on Russian cybersecurity firm Kaspersky that Moscow blamed on the NSA. "This is highly sophisticated, took millions of dollars to develop, and it bears the hallmarks of other modules that have been publicly attributed to the US government," says iVerify cofounder Rocky Cole, a former NSA employee.
The implications are staggering: American taxpayer-funded tools may now be targeting American citizens.
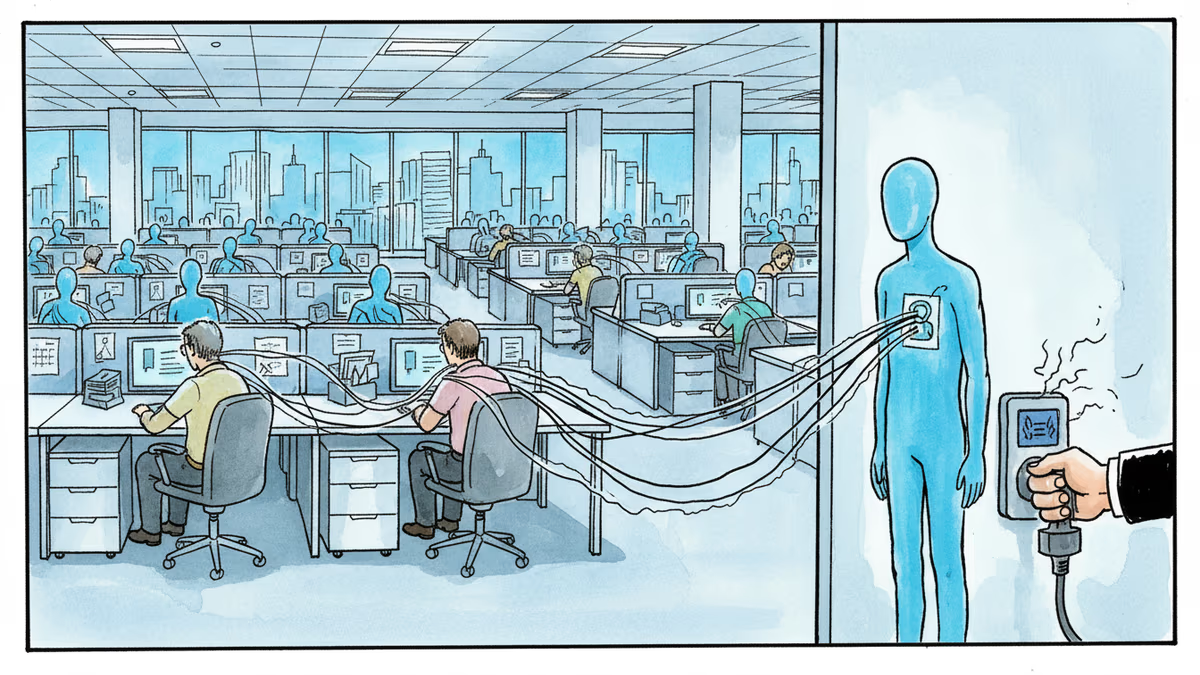
A Market for Digital Weapons
How does a government hacking tool end up in criminals' hands? The answer lies in the shadowy world of zero-day brokers—middlemen who pay tens of millions for secret hacking techniques and sell to the highest bidder.
This month, Peter Williams, an executive at US contractor Trenchant, received a seven-year sentence for selling hacking tools to Russian brokers. His company had contracts with US intelligence and "Five Eyes" allies, yet Williams sold to Operation Zero, a Russian broker network.
"These zero-day and exploit brokers tend to be unscrupulous," Cole explains. "They sell to the highest bidder and they double dip. Many don't have exclusivity arrangements."
The Scale of Damage
While Apple patched Coruna's vulnerabilities in iOS 18, devices running iOS 13 through 17.2.1 remain vulnerable. The only protection? Apple's stringent Lockdown Mode, which Coruna checks for and avoids.
iVerify estimates the cryptocurrency theft campaign alone infected roughly 42,000 devices. The total number of victims across all three campaigns—including Ukrainians targeted by Russian spies—remains unknown.
"My God, these things are very professionally written," says iVerify's Spencer Parker, contrasting Coruna's polished code with the "poorly written" malware added by cybercriminals.
The EternalBlue Parallel
Cole calls this "the EternalBlue moment for mobile malware," referencing the NSA tool leaked in 2017 that powered catastrophic attacks like North Korea's WannaCry and Russia's NotPetya. Just as EternalBlue escaped NSA control to wreak global havoc, Coruna represents the mobile equivalent—a government-grade weapon now in the wild.
The pattern is troubling: sophisticated tools created for national security repeatedly become threats to the very citizens they were meant to protect.
Authors
Related Articles

UK Visa Portal, a private immigration service mistaken for an official government site, has been exposing passport scans and selfies of over 100,000 applicants. The breach remains unpatched.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.
At Apple's 50th anniversary, top executives insisted the iPhone will anchor the AI era—and beyond. But is that confidence visionary or a warning sign?
Apple has hit 25% iPhone production in India, a milestone years in the making. What it means for supply chains, consumers, and the geopolitics of where things get made.
Thoughts
Share your thoughts on this article
Sign in to join the conversation