AI Agent Marketplaces Become New Hacking Highway
OpenClaw's skill marketplace harbors hundreds of malware-infected add-ons, exposing critical security flaws in AI agent ecosystems as convenience meets cyberthreat reality.
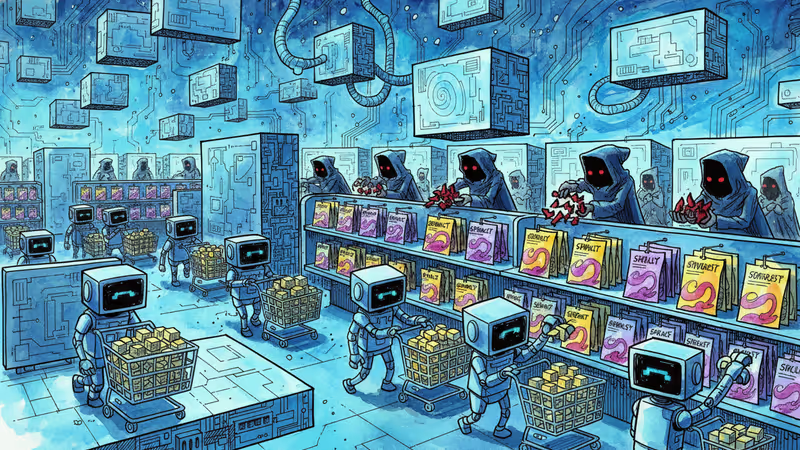
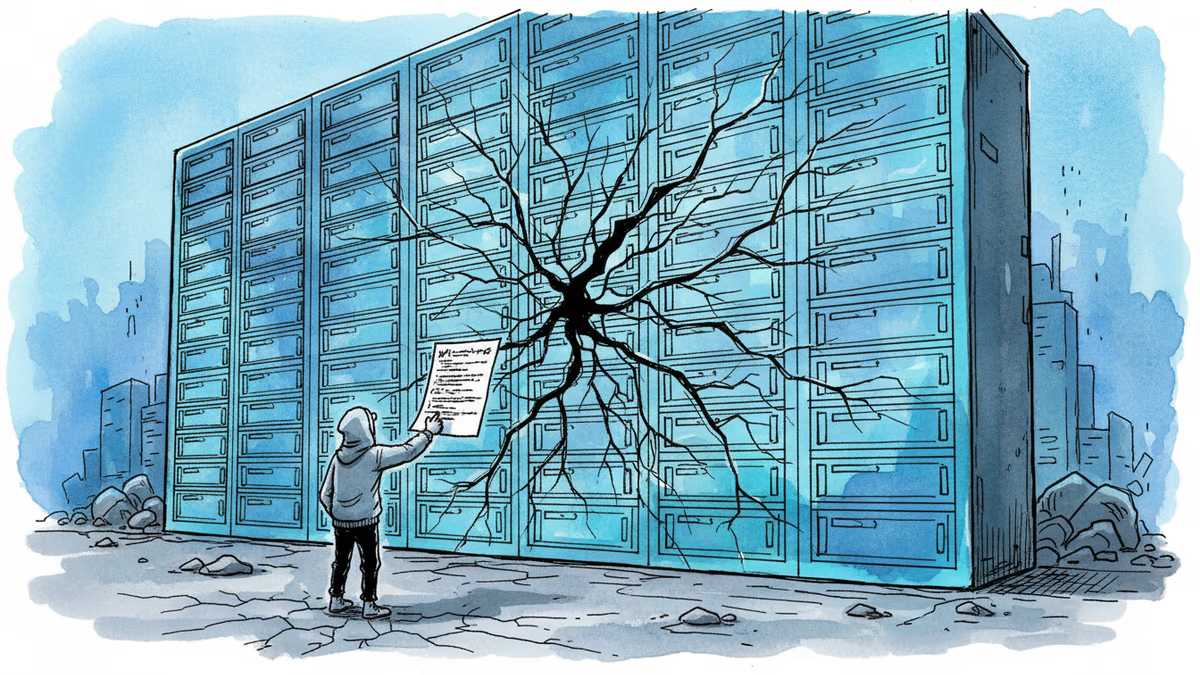
The AI agent that took the internet by storm in just one week has become a cybersecurity nightmare. OpenClaw, the "AI that actually does things," is now serving as an unintended gateway for hackers after researchers discovered malware lurking in hundreds of user-submitted skills on its marketplace.
Jason Meller, VP of Product at 1Password, didn't mince words in his Monday blog post: OpenClaw's skill hub has transformed into "an attack surface," with the platform's most popular add-on functioning as a "malware delivery vehicle."
The Promise That Became a Problem
OpenClaw (formerly Clawdbot, then Moltbot) marketed itself as the AI agent users had been waiting for—one that could manage calendars, check in for flights, clean out inboxes, and handle dozens of other mundane tasks. Running locally on devices, it offered the tantalizing prospect of a truly helpful digital assistant.
The platform's genius lay in its extensibility. Users could download "skills" from a marketplace, essentially teaching their AI agent new tricks. Want it to order groceries? There's a skill for that. Need it to manage your social media? Another skill awaits.
But this very flexibility created the perfect storm for cybercriminals. The same open ecosystem that made OpenClaw so appealing to users made it equally attractive to hackers looking for new ways to infiltrate systems.
A New Attack Vector Emerges
Unlike traditional app stores with established vetting processes, AI skill marketplaces operate in a regulatory gray area. The verification systems are often minimal, and the rapid pace of AI development means security considerations frequently take a backseat to functionality.
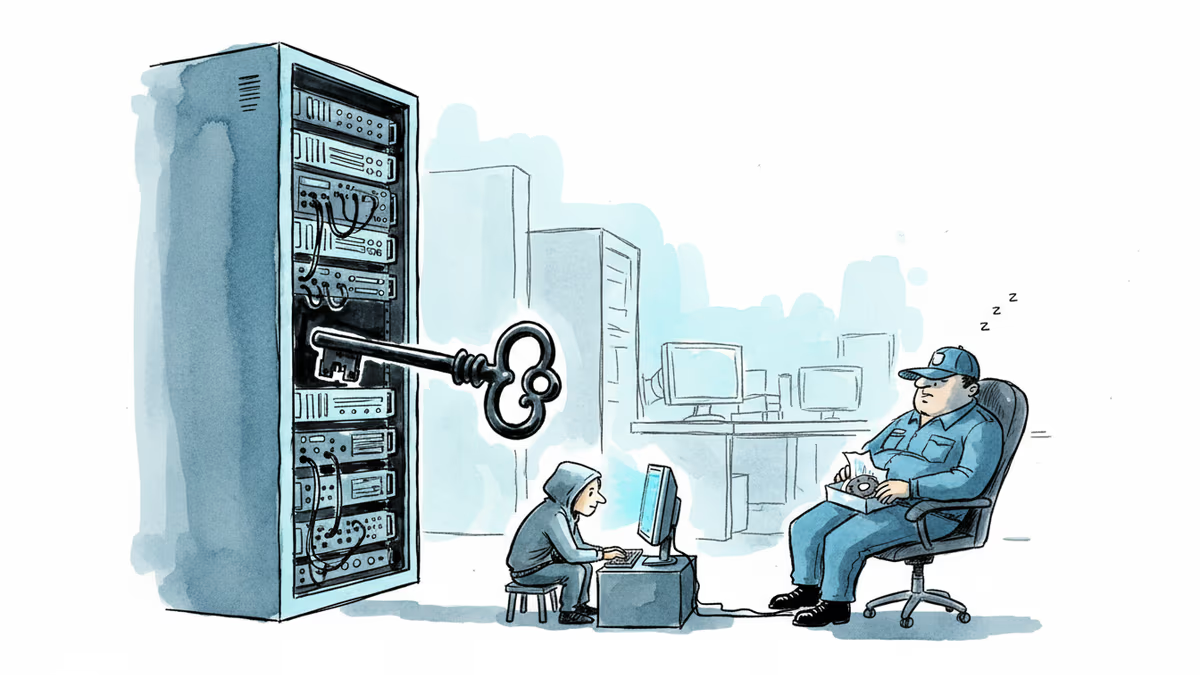
The implications are particularly severe for locally-running AI agents like OpenClaw. These systems have direct access to user data, system resources, and often elevated permissions to perform their tasks. When compromised, they don't just steal data—they can manipulate it, corrupt it, or use it as a launching pad for broader attacks.
Consider the scope of access these agents require: email accounts, calendar systems, financial platforms, social media profiles. A malicious skill doesn't just get one piece of information—it potentially gets the keys to your entire digital life.
The Regulatory Vacuum
Current cybersecurity frameworks weren't designed for AI agents that blur the lines between software and autonomous actors. Traditional malware detection focuses on known signatures and behaviors, but AI-powered attacks can adapt and evolve in real-time.
Regulators face a classic catch-22: move too slowly, and harmful applications proliferate; move too quickly, and you risk stifling innovation in a rapidly evolving field. The OpenClaw incident suggests we may have already waited too long to address these fundamental security challenges.
Major tech companies are watching this unfold with keen interest. Microsoft's Copilot, Google's Bard, and OpenAI's GPT models all incorporate similar extensibility features. The lessons learned from OpenClaw's security failures will likely influence how these platforms approach marketplace security going forward.
Authors
Related Articles
Dirty Frag gives low-privilege users root access on virtually every Linux distro. The exploit code leaked three days ago. Microsoft says attackers are already experimenting with it.
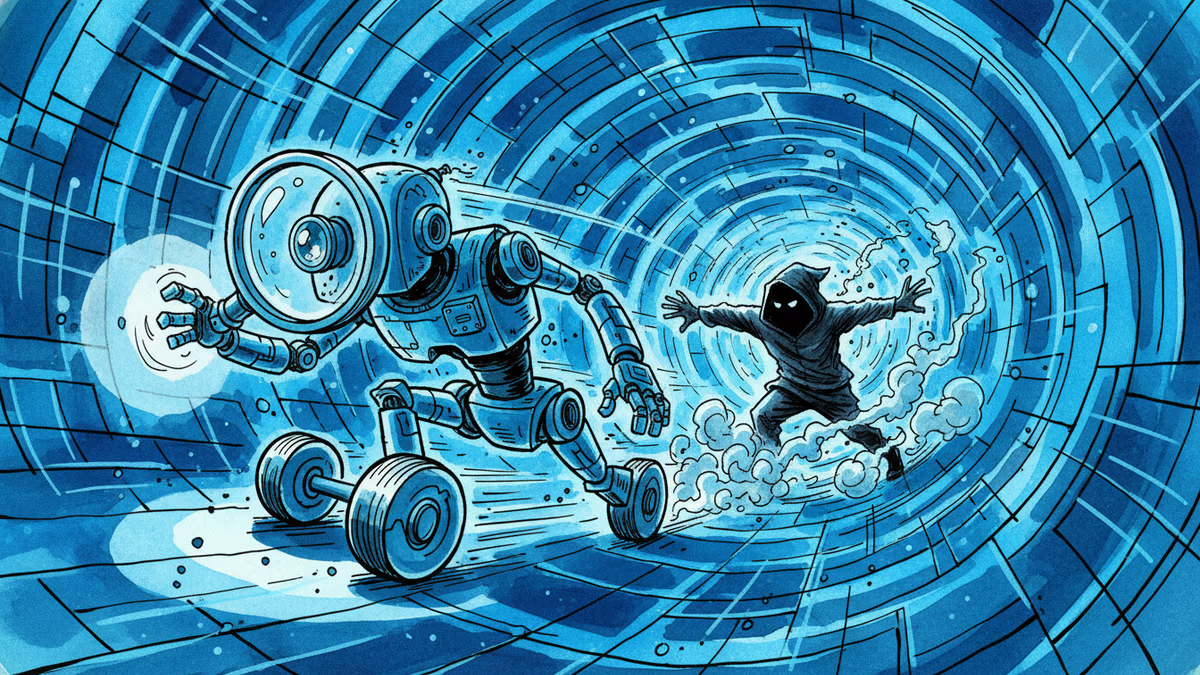
OpenAI's new Daybreak initiative uses the Codex AI agent to find and patch security vulnerabilities before attackers do—putting it in direct competition with Anthropic's secretive Claude Mythos.
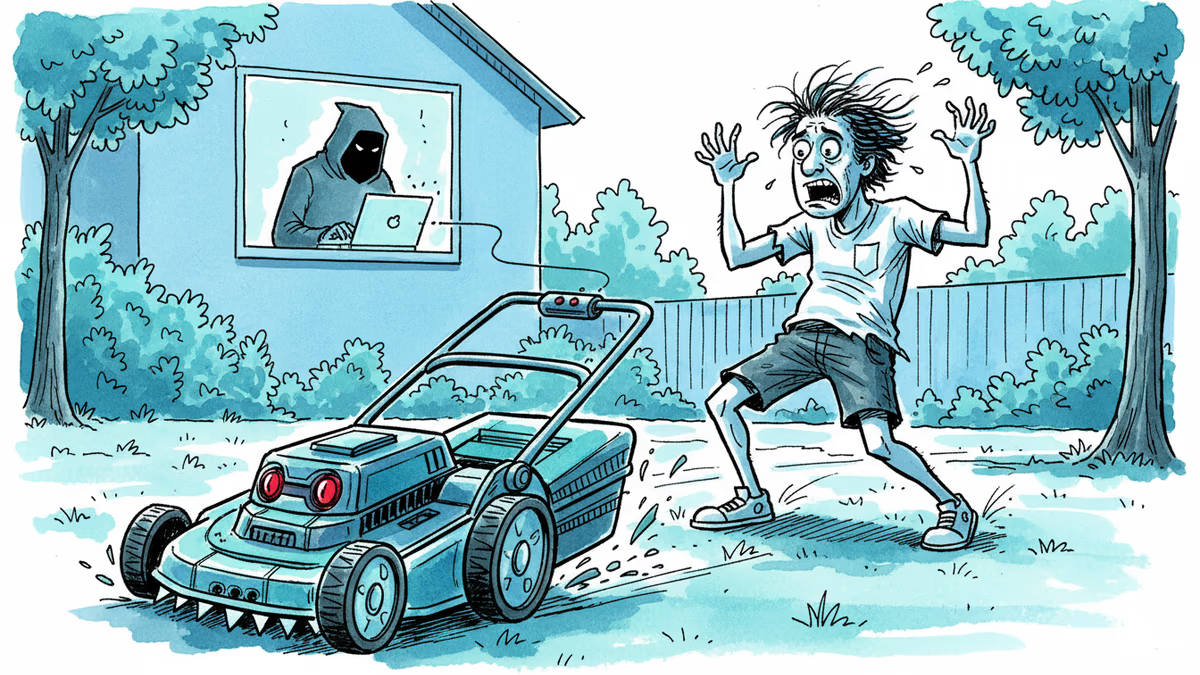
Yarbo's robot lawn mowers had critical security flaws exposing GPS, Wi-Fi passwords, and emails. The company confirmed the findings and cut remote access. But the real issue runs deeper than one brand.
A critical Linux kernel vulnerability called CopyFail lets any low-privilege user seize full root access. It affects nearly every major distro, is being actively exploited, and patches haven't reached most systems yet.
Thoughts
Share your thoughts on this article
Sign in to join the conversation