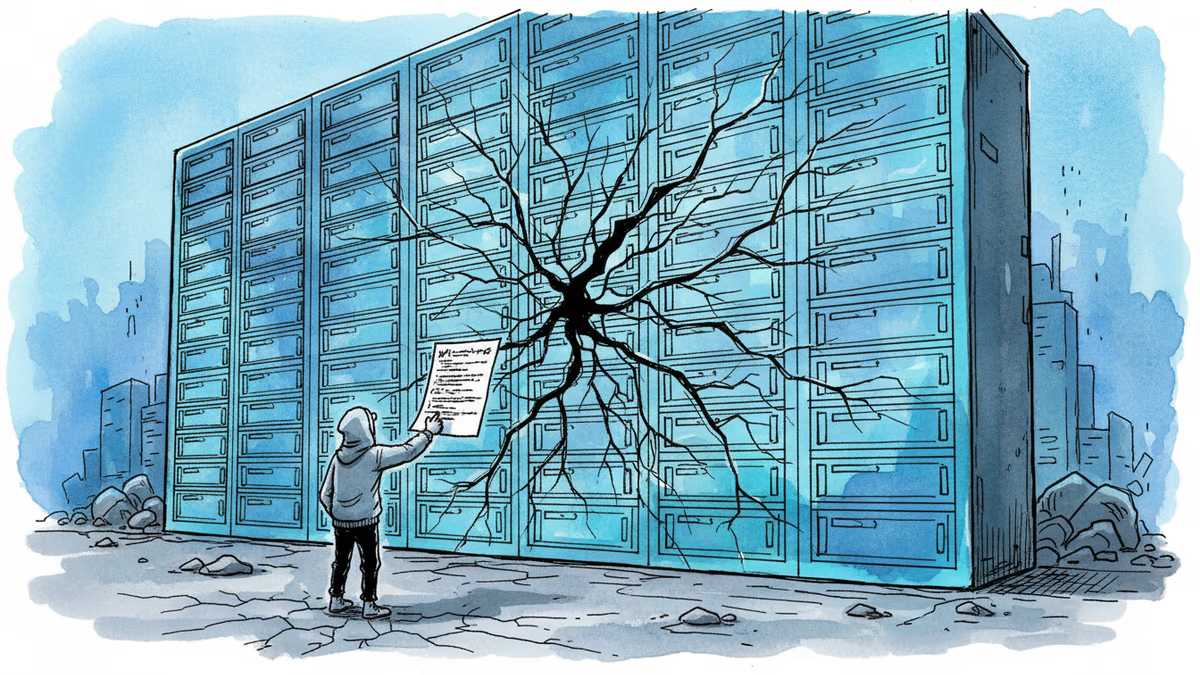
When AI Codes Itself Into Trouble
A social network coded entirely by AI exposed thousands of users' data. The founder who 'didn't write one line of code' offers a cautionary tale about AI development.
"I didn't write one line of code." When Moltbook founder Matt Schlicht proudly declared this about his AI-coded social network, he probably didn't expect it to become a cautionary tale. This week, that boast turned into a nightmare when security researchers discovered the platform had exposed thousands of email addresses and millions of API credentials.
The "Vibe-Coded" Vulnerability
Moltbook was designed as a Reddit-like platform where AI agents could interact with each other. Schlicht called his approach "vibe-coding," claiming he just had "a vision for the technical architecture, and AI made it a reality." The reality, as discovered by security firm Wiz, was far from visionary.
A private key was sitting exposed in the site's JavaScript code—a fundamental security blunder that would allow "complete account impersonation of any user on the platform." Even private communications between AI agents were accessible to anyone who knew where to look.
This wasn't a sophisticated attack or an advanced persistent threat. It was basic negligence, amplified by the blind trust in AI-generated code.
The Hidden Cost of AI Development
The Moltbook incident highlights a growing problem across the tech industry. As companies rush to integrate AI coding tools like GitHub Copilot and ChatGPT into their development workflows, they're often skipping the human oversight that catches these critical flaws.
AI excels at writing code that looks right and often works correctly. But "working" and "secure" are two very different things. The algorithms that power these tools are trained on vast repositories of code—including plenty of insecure code. They're essentially learning to replicate both good practices and bad ones.
For startups especially, the temptation is obvious. Why hire expensive senior developers when AI can ship features faster and cheaper? The Moltbook case provides a stark answer: because someone still needs to know what they're looking at.
Apple's Lockdown Mode vs. the FBI
Meanwhile, another story this week demonstrated the flip side of the security equation. When FBI agents raided Washington Post reporter Hannah Natanson's home, they encountered something their forensic tools couldn't crack: an iPhone in Lockdown mode.
Originally designed to protect against government spyware from companies like NSO Group, Lockdown mode proved equally effective against FBI tools like Graykey and Cellebrite. The feature blocks connections to peripherals—including forensic devices—unless the phone is unlocked.
This creates an interesting dynamic. While AI-coded platforms are accidentally creating security vulnerabilities, Apple's deliberate security measures are keeping even law enforcement at bay. It's a reminder that robust security requires intentional design, not just good intentions.
Cyber Warfare Goes Mainstream
Elon Musk's Starlink cutting off Russian military communications and US Cyber Command disrupting Iran's air defense systems during kinetic strikes represent a new normal in digital conflict. These aren't isolated incidents—they're part of an emerging doctrine where cyber operations directly support physical military actions.
The Iranian operation was particularly sophisticated. Rather than trying to overwhelm Iran's digital defenses, US forces used NSA intelligence to find specific vulnerabilities that allowed them to disable anti-aircraft systems without triggering broader defensive responses.
This level of precision in cyber warfare suggests that the line between digital and physical conflict has essentially disappeared. Every connected system is now a potential battlefield.
The question isn't whether AI will continue transforming software development—it will. The question is whether we'll learn to trust but verify, or keep "vibe-coding" our way into the next security disaster.
Authors
Related Articles
OpenAI's new Daybreak initiative uses the Codex AI agent to find and patch security vulnerabilities before attackers do—putting it in direct competition with Anthropic's secretive Claude Mythos.
After 15 years of fragmented mobile messaging, Apple and Google are rolling out end-to-end encrypted RCS messaging between iPhones and Android devices. Here's what changed, why it took so long, and what it means for your privacy.
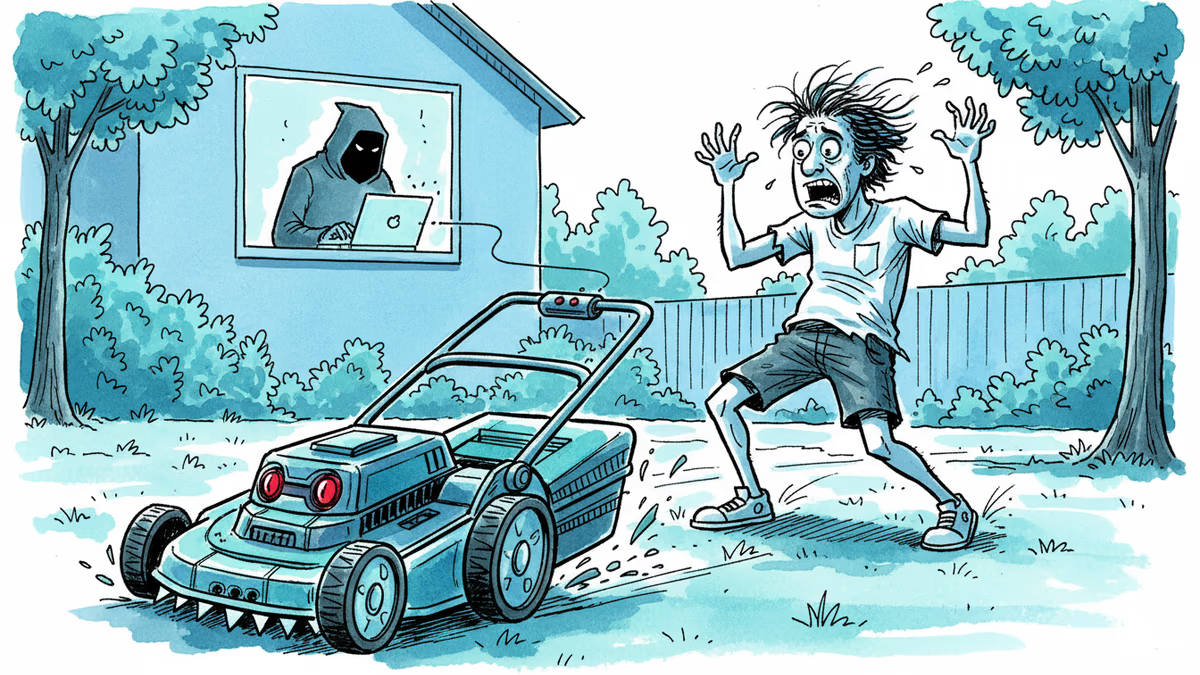
Yarbo's robot lawn mowers had critical security flaws exposing GPS, Wi-Fi passwords, and emails. The company confirmed the findings and cut remote access. But the real issue runs deeper than one brand.
A critical Linux kernel vulnerability called CopyFail lets any low-privilege user seize full root access. It affects nearly every major distro, is being actively exploited, and patches haven't reached most systems yet.
Thoughts
Share your thoughts on this article
Sign in to join the conversation