
The App That Promised Anonymity Just Leaked 93GB of Tip Data
P3 Global Intel, which powers anonymous crime tip systems for law enforcement worldwide, suffered a major breach. The implications go far beyond a typical data leak.
Someone trusted a system with their life. That system just got hacked.
Earlier this month, a group calling themselves the "Internet Yiff Machine" dropped 93GB of data they claim to have stolen from P3 Global Intel—the company behind anonymous crime tip management software used by Crime Stoppers programs, police departments, and government agencies around the world. P3 had promised users, plainly and publicly, that "your anonymity is protected at all times."
That sentence now reads very differently.
What P3 Actually Does—and Why This Breach Is Different
P3 Global Intel isn't a household name, but its software sits at the center of how many communities report crime. A citizen sees something suspicious—a drug deal, a missing person, a threat. They open an app or a web portal, submit a tip anonymously, and the system manages the back-and-forth between them and law enforcement. No names. No phone numbers. That's the promise.
The company has described itself as "the new standard in tip management" for law enforcement and government agencies globally. That's not a small claim—it means P3's infrastructure is woven into active criminal investigations in multiple countries.
So when hackers claim to have exfiltrated 93GB from that infrastructure, the question isn't just "what data was taken." It's: who can now be identified, and what happens to them next?
Tip submissions in these systems aren't complaints about parking violations. They include information about organized crime, drug trafficking, gang activity, domestic violence, and terrorism. People use anonymous tip lines precisely because their safety depends on not being identified. Unlike a leaked credit card number—which you cancel and replace—a leaked identity in this context can carry physical consequences.
The Trust Problem Is Bigger Than the Breach
Data breaches happen constantly. What makes this one structurally significant is the function it attacks.
Crime tip systems run on a social contract: tell us what you know, and we'll protect you. That contract doesn't just protect individual tipsters—it keeps information flowing into law enforcement. When that contract breaks, the damage compounds quietly. Future witnesses stay silent. Cold cases stay cold. The breach you're reading about today has a second-order effect that plays out over years, not days.
Cybersecurity researchers have long flagged the risks of outsourcing sensitive law enforcement data management to private vendors. The argument isn't that private companies are inherently less secure—it's that the accountability structures are different. A police department that mishandles witness data faces legal and political consequences. A vendor that does the same faces... a PR problem and, possibly, a lawsuit.
P3 has not, as of this writing, issued a detailed public statement about the scope of the breach, what data was compromised, or what notifications have been sent to affected agencies or individuals.
Who's Watching Whom
For law enforcement agencies, this is a dual crisis. There's the immediate question of whether active investigation data was exposed. And there's the longer-term question of whether their tip pipelines will dry up as public trust erodes. Both are operational problems, not just reputational ones.
For privacy advocates, the breach validates a concern that predates P3 by decades: sensitive public functions—whistleblowing, witness protection, anonymous reporting—should not be dependent on the security posture of a private company whose practices aren't subject to public audit.
For policymakers, the pressure is now on. The EU's GDPR and the US's patchwork of state privacy laws create some baseline obligations, but neither framework was designed with law enforcement tip systems specifically in mind. The regulatory gap is real.
For the general public, the calculus is uncomfortable. If you witnessed something and wanted to report it anonymously—would you, today? That hesitation, multiplied across thousands of potential tipsters, is itself a cost of this breach.
Authors
Related Articles
Dirty Frag gives low-privilege users root access on virtually every Linux distro. The exploit code leaked three days ago. Microsoft says attackers are already experimenting with it.
OpenAI's new Daybreak initiative uses the Codex AI agent to find and patch security vulnerabilities before attackers do—putting it in direct competition with Anthropic's secretive Claude Mythos.
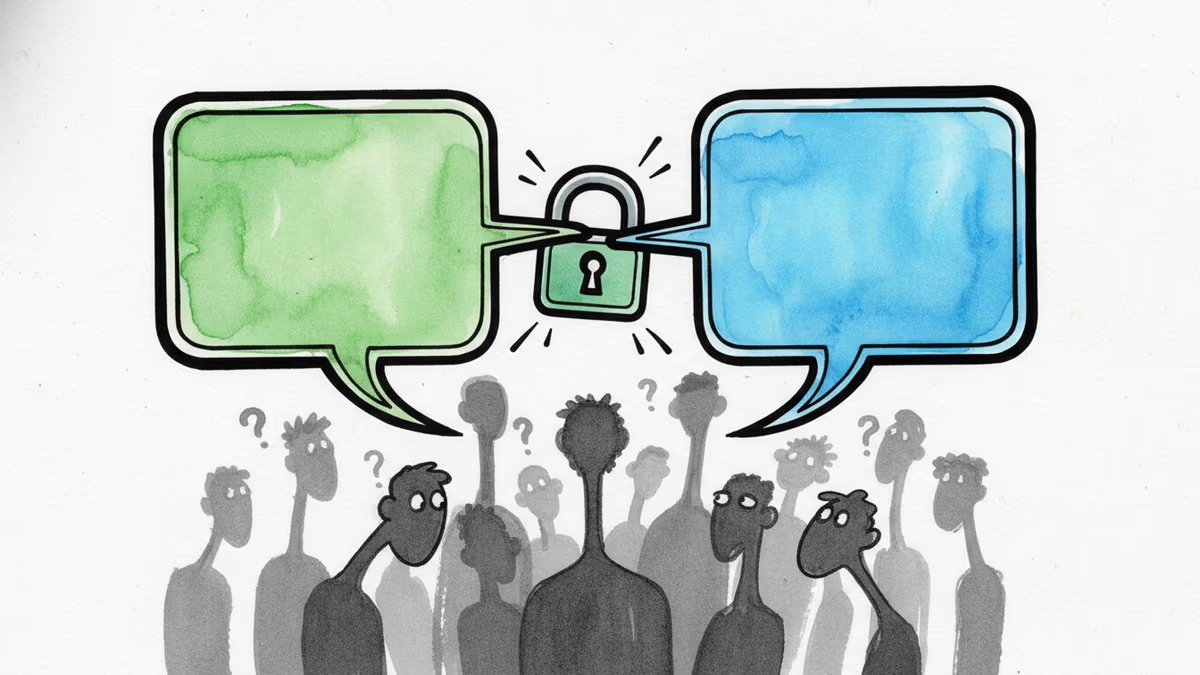
After 15 years of fragmented mobile messaging, Apple and Google are rolling out end-to-end encrypted RCS messaging between iPhones and Android devices. Here's what changed, why it took so long, and what it means for your privacy.
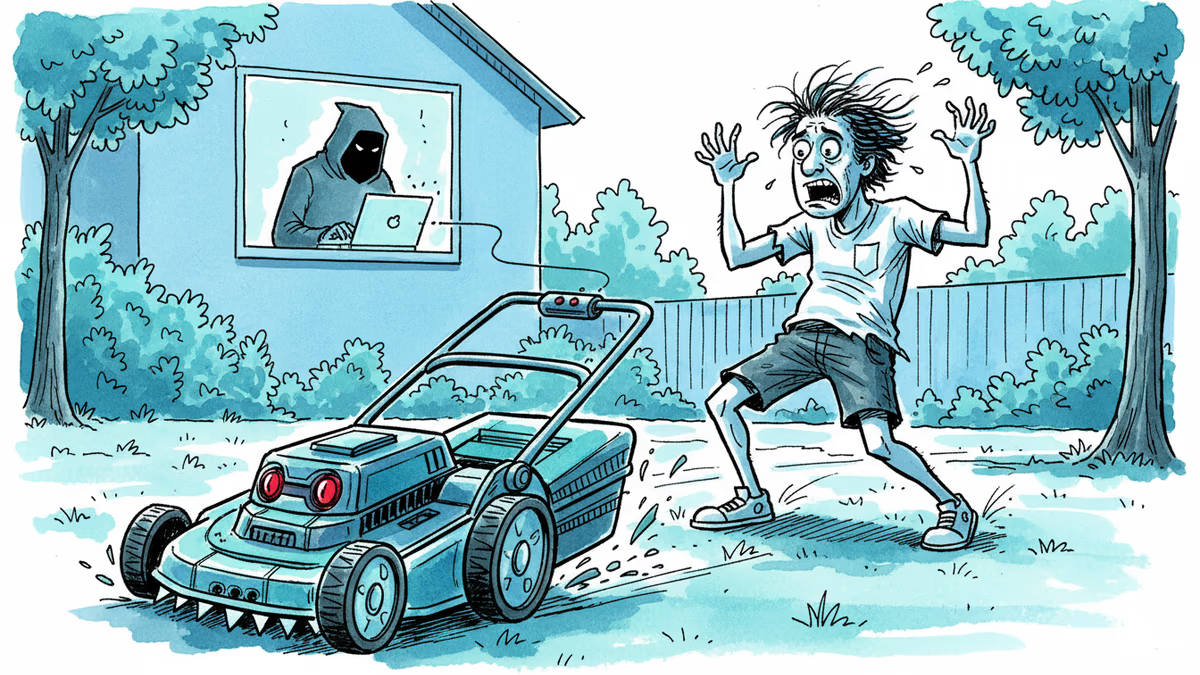
Yarbo's robot lawn mowers had critical security flaws exposing GPS, Wi-Fi passwords, and emails. The company confirmed the findings and cut remote access. But the real issue runs deeper than one brand.
Thoughts
Share your thoughts on this article
Sign in to join the conversation