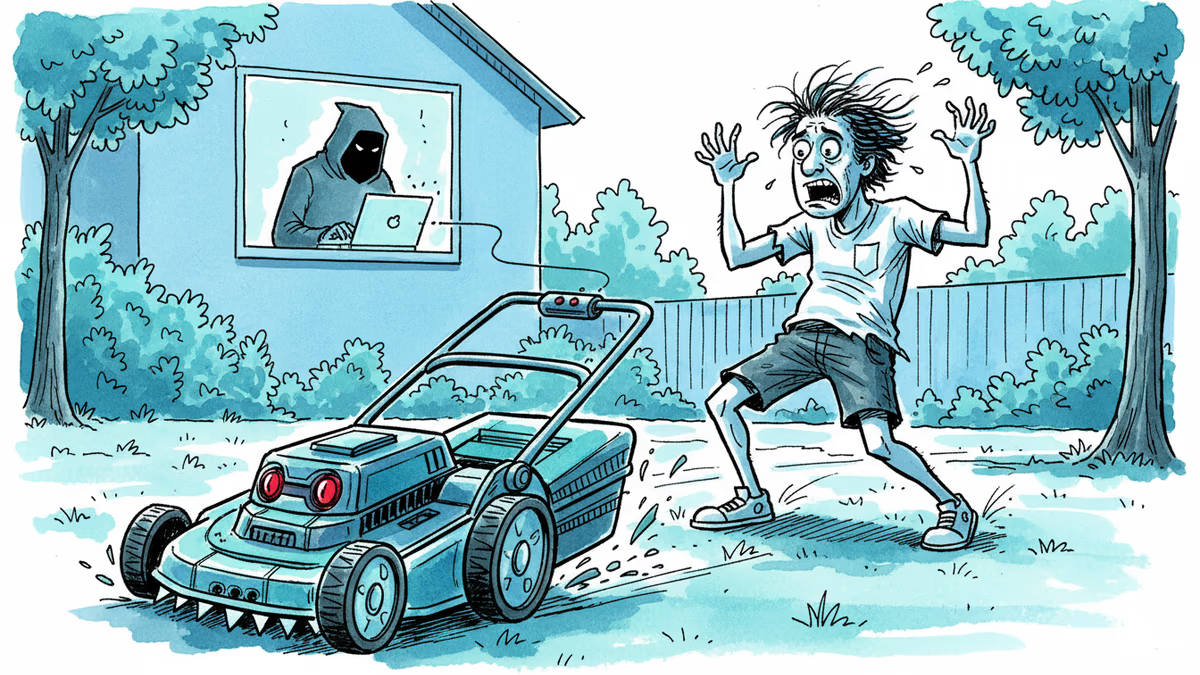
A Hacker Ran Me Over With a Robot Lawn Mower
Yarbo's robot lawn mowers had critical security flaws exposing GPS, Wi-Fi passwords, and emails. The company confirmed the findings and cut remote access. But the real issue runs deeper than one brand.
A security researcher didn't just find a vulnerability. He used it to drive a bladed robot at a journalist.
What Actually Happened
The Verge ran a two-day investigation into Yarbo, a Chinese robotics company selling smart lawn mowers across North America and Europe. A security researcher discovered that the authentication system protecting Yarbo's cloud-connected devices was, in plain terms, broken. Any casual hacker could intercept a device owner's GPS coordinates, home Wi-Fi password, and email address — and then remotely commandeer the machine itself. A machine with spinning blades.
Yarbo responded within 24 hours with a 1,200-word public statement. The company confirmed the researcher's findings, apologized, and announced it had temporarily disabled remote access across its fleet while it works on fixes. It also published a detailed remediation roadmap — an unusually transparent move in an industry where the default response to disclosed vulnerabilities tends to be silence, denial, or a one-line acknowledgment weeks later.
The apology is noted. The structural problem, however, predates Yarbo and will outlast it.
The Architecture of the Problem
To understand why this keeps happening, you need to understand how most IoT devices work. When you control a smart device from your phone — whether it's a lawn mower, a robot vacuum, or a doorbell camera — your command doesn't go directly to the device. It travels to a cloud server, which then relays it to the machine. This architecture enables remote control from anywhere. It also means that if the authentication layer between you and that server is poorly designed, anyone with network access can issue commands as if they were you.
Yarbo's flaw sat precisely in that layer. And it isn't a new story. Ecovacs robot vacuums were compromised in 2023, exposing live camera feeds inside people's homes. Smart locks, baby monitors, and connected toys have each had their moment in the vulnerability spotlight. The pattern isn't a series of isolated incidents — it's an industry that has consistently prioritized time-to-market over security architecture.
Three Ways to Read This
For consumers, the Wi-Fi password exposure is the detail that should give pause. Your home network password is the skeleton key to every device on that network — laptops, phones, smart TVs, medical devices. A compromised lawn mower isn't just a lawn mower problem. It's a perimeter problem.
For the industry, Yarbo's response is actually a case study worth examining. The company moved fast, disclosed fully, and didn't lawyer up its language into meaninglessness. Whether that transparency translates into sustained security investment — or was a one-time crisis management calculation — is the question that will answer itself over the next 12 months of patch cadence.
For regulators, this is exactly the scenario that EU's Cyber Resilience Act was designed to address. Effective 2025, the CRA requires IoT devices sold in the EU to meet mandatory cybersecurity standards before market entry — not as a voluntary certification, but as a legal prerequisite. The US has no equivalent federal standard yet, though NIST guidelines exist and the FCC has begun exploring labeling requirements. The gap between the regulatory environments is significant, and it shapes which products reach which shelves.
Who Carries the Cost
When a security flaw is discovered, the costs distribute unevenly. The researcher gets recognition. The journalist gets a story (and nearly gets run over). The company absorbs reputational damage and remediation costs. The consumer absorbs the risk — often without knowing it existed.
This asymmetry is what makes voluntary security standards structurally insufficient. A manufacturer competing on price has every incentive to cut security investment that consumers can't see and won't test before purchase. The market doesn't naturally price in the risk of a compromised device sitting on someone's home network for five years.
This content is AI-generated based on source articles. While we strive for accuracy, errors may occur. We recommend verifying with the original source.
Related Articles
A critical Linux kernel vulnerability called CopyFail lets any low-privilege user seize full root access. It affects nearly every major distro, is being actively exploited, and patches haven't reached most systems yet.

From hyper-personalized phishing to deepfake video calls, AI has turbocharged cybercrime. Meanwhile, hospitals adopt AI tools whose patient benefits remain unproven. What does this mean for trust?
Anthropic's tightly restricted Mythos AI—designed to find security flaws—was accessed by Discord sleuths without a single line of exploit code. Meanwhile, North Korean hackers used AI to steal $12M in three months. The security paradox of 2026.

Microsoft is letting Windows users delay updates indefinitely — 35 days at a time, as many times as they want. A long-overdue fix, or a security risk hiding in plain sight?
Thoughts
Share your thoughts on this article
Sign in to join the conversation