The AI Built to Stop Hackers Just Got Hacked
Anthropic's tightly restricted Mythos AI—designed to find security flaws—was accessed by Discord sleuths without a single line of exploit code. Meanwhile, North Korean hackers used AI to steal $12M in three months. The security paradox of 2026.
The most powerful AI security tool in existence was accessed by a group of hobbyists on Discord. No zero-days. No sophisticated exploits. Just a data breach at an unrelated startup, some educated guessing about URL formats, and permissions that were already sitting there, waiting to be used.
That's the story of Anthropic's Mythos Preview—and it tells us something uncomfortable about the moment we're in.
Three Stories, One Uncomfortable Pattern
This week handed the cybersecurity world three events that, taken together, form a kind of Rorschach test for the AI security debate.
Anthropic had restricted Mythos Preview to a carefully vetted group of researchers. The model is, by the company's own admission, unusually capable at finding vulnerabilities in software and networks—capable enough to warrant tight controls. Yet a group of Discord users pieced together access through what Bloomberg described as straightforward detective work: they combed data from a breach at Mercor, an AI training startup, made an educated guess about the model's URL based on Anthropic's known naming conventions, and leveraged existing permissions held by someone who worked for an Anthropic contracting firm. The result: access not just to Mythos but to other unreleased Anthropic models. The group, apparently aware of the stakes, used it only to build simple websites—laying low to avoid detection.
In the same week, Mozilla announced it had used early, authorized access to Mythos Preview to identify and patch 271 vulnerabilities before shipping Firefox 150. Same tool. Radically different outcome.
And then there's the North Korea angle. Researchers identified a group of moderately skilled North Korean hackers—not the elite units—who have been using AI to write malware through what's being called "vibe coding" and to spin up convincing fake company websites. Their haul: up to $12 million in three months. AI didn't make them elite hackers. It made average hackers significantly more productive.
The Vulnerabilities That Never Got Fixed
Behind the AI headlines, older wounds are still bleeding.
Citizen Lab confirmed this week what security researchers have warned about for years: the SS7 telecom protocol—the aging infrastructure that routes calls and texts between phone networks globally—is being actively exploited by commercial surveillance vendors. Two firms essentially posed as rogue phone carriers, piggybacking on access to three small telecoms (019Mobile in Israel, Tango Mobile in the UK, and Airtel Jersey in the English Channel) to track the location of "high-profile" targets. Citizen Lab declined to name either the firms or their targets but warned the two companies are likely not operating alone.
SS7's vulnerabilities have been documented since at least 2014. More than a decade later, they remain structurally embedded in global telecom infrastructure—not because no one knows how to fix them, but because fixing them requires coordinated action across hundreds of carriers worldwide.
In the UK, a different kind of trust broke down. UK Biobank—which holds health data from 500,000 British citizens, including genetic information, medical imaging, and health records—revealed that three scientific research institutions had been selling that data on Alibaba. The breach wasn't a hack. It was a contract violation. The people who were supposed to protect the data were the ones selling it.
And Apple quietly patched a flaw this week that allowed the FBI to retrieve Signal messages from a defendant's iPhone—even after the app had been deleted—through iOS push notification logs. Apple's iOS 26.4.2 update addressed the logging issue. But the episode is a reminder that end-to-end encryption protects data in transit, not data at rest on an unlocked device.
Who's Winning—and Who Decides?
The stakeholder map here is genuinely complicated.
For enterprises and developers, the Mozilla case is the argument for AI-assisted security at scale. 271 vulnerabilities caught before release is not a small number. The question is whether the same efficiency gains accrue equally to defenders and attackers—and the North Korea case suggests they don't, or at least not symmetrically.
For policymakers, the week surfaced a familiar deadlock. A US surveillance program that lets the FBI access Americans' communications without a warrant is up for renewal, and Congress is stuck. A new bill has been introduced to address concerns, but observers say it lacks substance. The tools of surveillance are getting sharper; the oversight of those tools is not keeping pace.
For privacy advocates, the Apple patch and the UK Biobank breach point to the same structural problem: consent is given once, but data lives forever—and the people who hold it don't always stay trustworthy. Signal users who thought they were protected by encryption were partially right. But "partially right" in security is just another way of saying "partially wrong."
For the general public, the most actionable takeaway from this week is also the most unsatisfying: the security of your data depends less on the tools you choose and more on the entire ecosystem those tools sit inside—the carriers, the OS, the cloud providers, the research institutions, and yes, the Discord communities that might be probing systems you didn't know existed.
This content is AI-generated based on source articles. While we strive for accuracy, errors may occur. We recommend verifying with the original source.
Related Articles

Microsoft is letting Windows users delay updates indefinitely — 35 days at a time, as many times as they want. A long-overdue fix, or a security risk hiding in plain sight?
Google is investing at least $10 billion in Anthropic, potentially up to $40 billion. With Amazon's $5B deal just days earlier, two tech giants are now backing the same AI startup — valued at $350 billion.

Google is committing up to $40 billion to Anthropic, a direct AI competitor. The deal reveals how the real AI arms race isn't about models — it's about who controls the infrastructure beneath them.
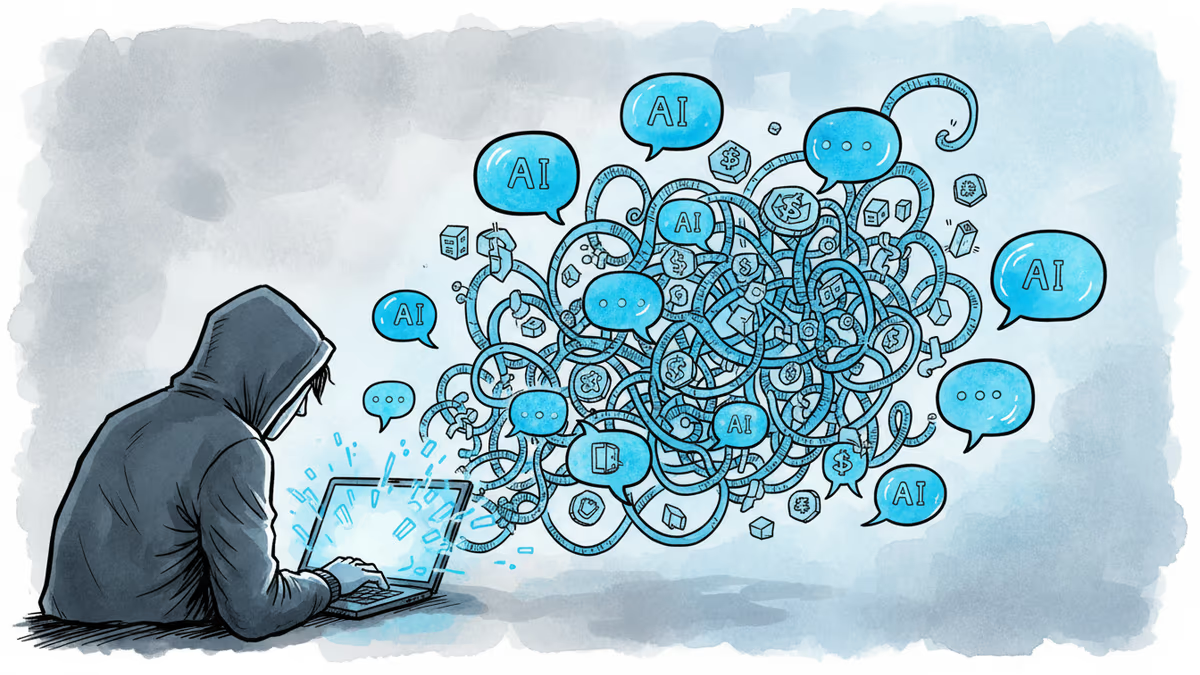
North Korean hackers used ChatGPT, Cursor, and AI web tools to steal $12M in crypto in 90 days—without knowing how to code. What this means for cybersecurity's future.
Thoughts
Share your thoughts on this article
Sign in to join the conversation