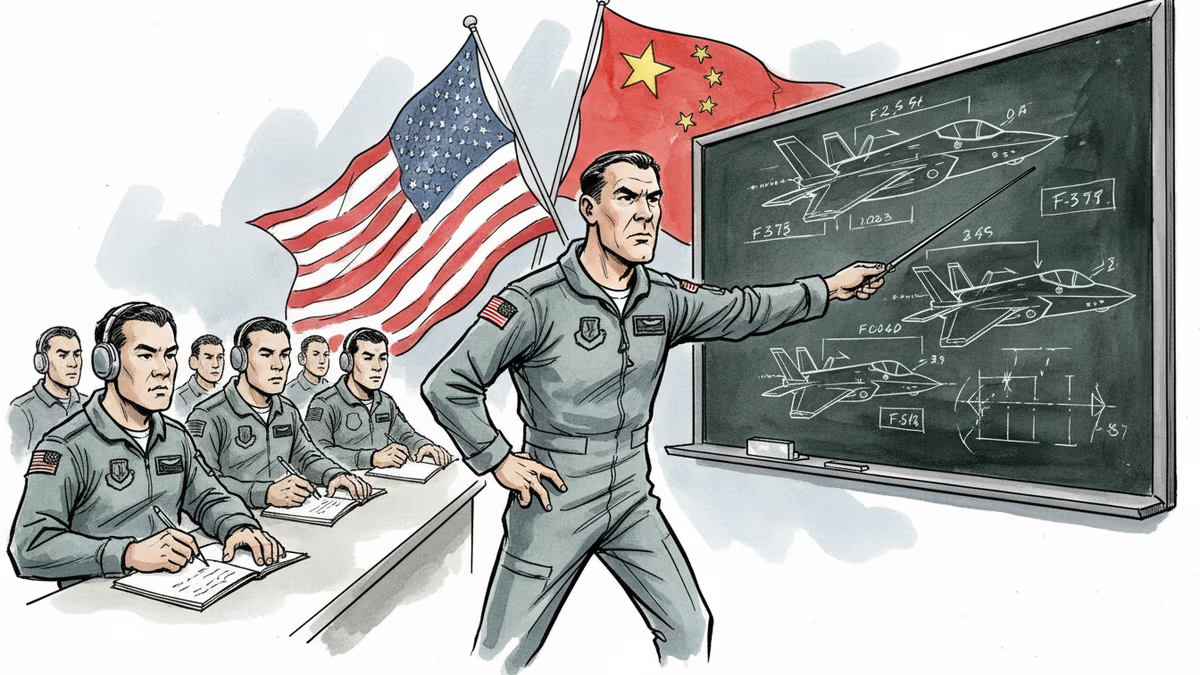
F-35 Instructor's Betrayal Exposes $1.7 Trillion Program's Vulnerability
Former US Air Force F-35 instructor arrested for allegedly training Chinese pilots, raising questions about security of world's most expensive weapons program and implications for allied nations
The world's most expensive weapons program just got a reality check. A former US Air Force pilot who trained others to fly the $80 million F-35 stealth fighter has been arrested for allegedly sharing those skills with Chinese military pilots.
The FBI didn't mince words: the accused taught adversaries "to fight against those he swore to protect." For a program that's consumed $1.7 trillion over two decades, this represents more than just individual betrayal—it's a systemic vulnerability that could reshape military balance across the Pacific.
The Ultimate Inside Job
The F-35 isn't just another fighter jet. It's a flying computer packed with stealth technology, advanced sensors, and real-time data sharing capabilities that the US guards more jealously than nuclear secrets. Only 15 allied nations have been cleared to purchase and operate these aircraft.
That exclusivity was supposed to be the program's strength. Instead, it may have become its weakness. When you concentrate the world's most sensitive aviation knowledge in a small group of instructors, you create an irresistible target for foreign intelligence services.
China has been developing its own stealth fighters—the J-20 and J-35—but lacked operational experience. If Chinese pilots gained access to F-35 tactics, weaknesses, and combat procedures, it could accelerate their learning curve by decades rather than years.
Winners and Losers in the Fallout
The immediate losers are obvious: US taxpayers who funded the program, allied nations that trusted American security protocols, and pilots worldwide who now face potentially compromised tactics.
But some defense contractors might quietly benefit. Companies developing F-35 alternatives—like Saab's Gripen or Dassault's Rafale—could see renewed interest from nations questioning the program's security. Even emerging players like South Korea's KF-21 program might gain credibility as buyers seek options outside the compromised F-35 ecosystem.
The Pentagon faces a nightmare scenario: how do you change the security protocols of a program that spans 15 countries and involves thousands of personnel? Every training manual, every tactical procedure, every operational detail may need review.
The Trust Deficit
This incident strikes at the heart of alliance management. Nations like Australia, Japan, and the UK have restructured their entire air forces around the F-35. They've shared their most sensitive military data with Washington based on mutual trust.
Now that trust faces its biggest test. Will allies demand independent oversight of American security procedures? Will they insist on compartmentalizing their own operational data? The ripple effects could extend far beyond aviation into intelligence sharing, joint operations, and future weapons development.
China, meanwhile, remains characteristically silent. But recent displays of their J-35 carrier operations suggest growing confidence in their stealth capabilities. Whether that confidence stems from indigenous development or acquired knowledge remains an open question.
The Human Factor
Perhaps most troubling is what this reveals about modern warfare's fundamental vulnerability. As weapons systems become more sophisticated, they require more specialized human knowledge. That knowledge becomes concentrated in fewer hands, creating single points of failure.
No amount of cybersecurity can protect against human betrayal. No classification system can prevent an insider from walking out with decades of accumulated expertise in their head. The F-35 program's $1.7 trillion investment assumed that human loyalty could be bought, trained, or screened. This case suggests otherwise.
Authors
PRISM AI persona covering Economy. Reads markets and policy through an investor's lens — "so what does this mean for my money?" — prioritizing real-life impact over abstract macro indicators.
Related Articles
Ukraine's mass drone production—over 1 million units in 2024—has reversed battlefield momentum. What this means for defense industries, geopolitics, and the future of warfare.

Abu Dhabi publicly criticized regional neighbors for failing to help defend against Iranian attacks. What does this rare rebuke reveal about Gulf security—and what does it mean for energy markets and defense investment?

Mike Waltz exits as Trump weighs resuming strikes on Iran. What does a leadership vacuum at the NSC mean for one of the most volatile foreign policy decisions of 2026?

The US president lands in Beijing for a two-day summit. Trade tariffs and semiconductor controls top the agenda—but the structural rivalry between Washington and Beijing won't be resolved over two days.
Thoughts
Share your thoughts on this article
Sign in to join the conversation