Your Security Camera Just Became a Weapon of War
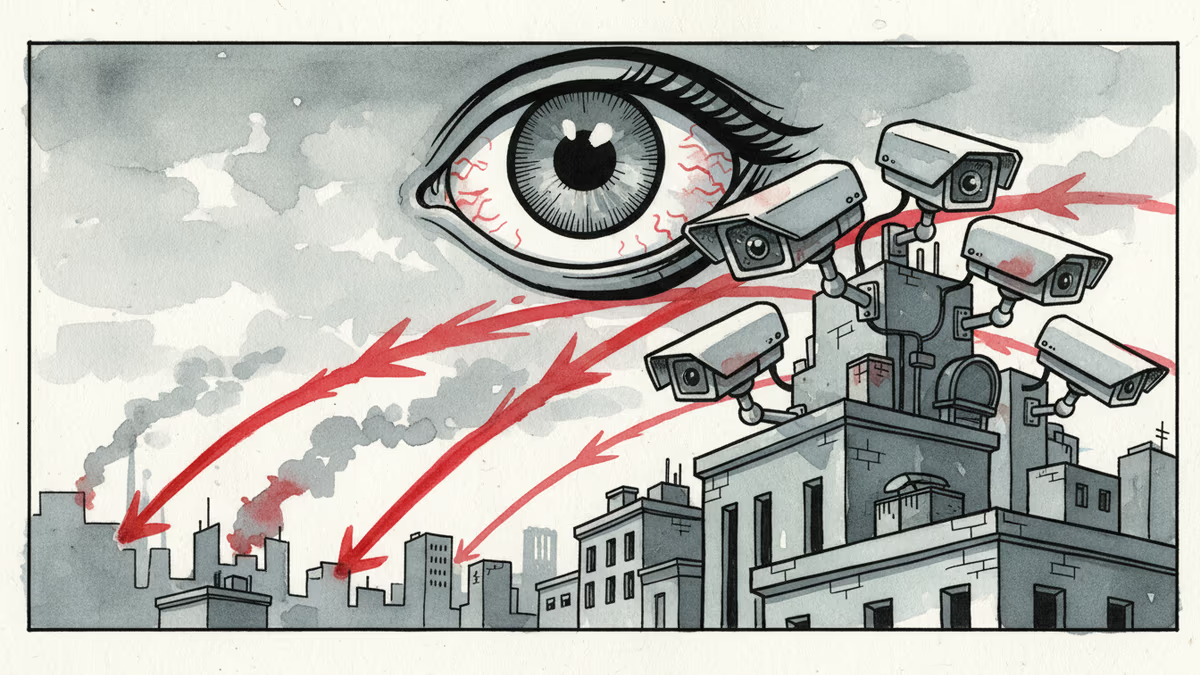
Iranian and Israeli forces are turning civilian security cameras into military surveillance tools, revealing how everyday IoT devices become part of modern warfare's kill chain.
Thousands of traffic cameras across Tehran had become Israel's eyes. They watched Iran's Supreme Leader Ali Khamenei's daily routines in real-time, feeding crucial intelligence for an assassination operation. "We knew Tehran like we know Jerusalem," an Israeli intelligence source told the Financial Times.
This isn't science fiction. This is warfare in 2026.
When Your Doorbell Cam Joins the Military
On Wednesday, Israeli security firm Check Point revealed that Iranian-linked hackers attempted to compromise hundreds of civilian security cameras across the Middle East. The timing wasn't coincidental—these hacking attempts aligned precisely with Iran's missile and drone strikes on Israel, Qatar, and Cyprus.
The targets? Ordinary Hikvision and Dahua cameras installed outside homes and on city streets across Bahrain, Cyprus, Kuwait, Lebanon, Qatar, and the UAE. In Israel alone, hundreds of intrusion attempts were detected.
"Now hacking cameras has become part of the playbook of military activity," says Sergey Shykevich, Check Point's threat intelligence researcher. "You get direct visibility without using expensive military satellites, often with better resolution."
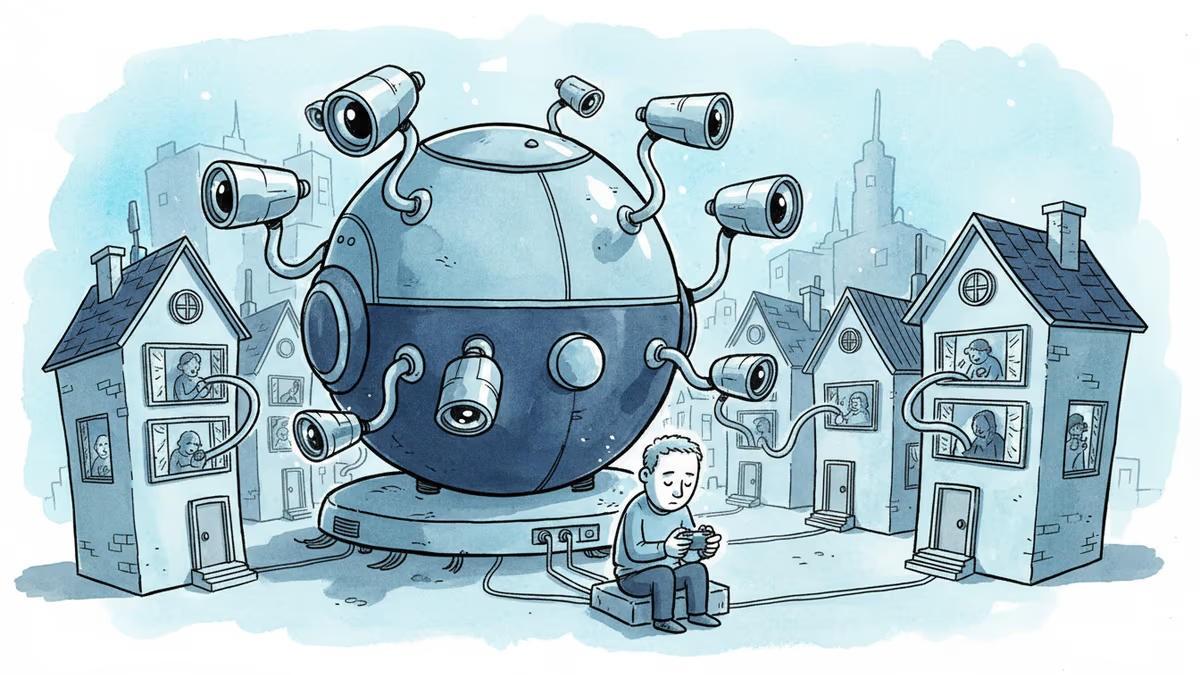
Five Vulnerabilities, Years of Neglect
The hackers exploited five distinct vulnerabilities—none sophisticated, all patched years ago. The oldest dates back to 2017. Yet these security holes persist because camera owners rarely install updates or even know they exist.
"It's straightforward for any attacker planning military activity," Shykevich explains. "Easy and provides very good value for your effort."
The attack timeline tells the story: concentrated efforts on February 28 and March 1 coincided with US and Israeli airstrikes on Iran. Earlier attempts in mid-January aligned with Iranian protests and strike preparations.
Ukraine Wrote the Playbook
This camera-hacking warfare first emerged in Ukraine. Russian forces compromised two security cameras in Kyiv to observe Ukrainian infrastructure and air defenses. "The aggressor used these cameras to collect data to prepare and adjust strikes on Kyiv," Ukraine's intelligence service reported.
Ukraine's response was dramatic: they disabled 10,000 internet-connected cameras that Russia could potentially exploit. Citizens were urged to stop online broadcasts from street webcams.
Yet Ukraine adopted the same tactics. When Ukrainian forces used underwater drones to destroy a Russian submarine in Sevastopol Bay, the published footage appeared to come from hacked surveillance cameras. Ukrainian hacktivist group One Fist was officially commended for hacking cameras to monitor Russian materiel movements across the Kerch Bridge.
The Economics of Digital Espionage
"The advantages are presence and expense," explains Peter W. Singer, a military researcher at the New America Foundation. "The adversary's already done the work for you. They've placed cameras all around a city."
Hacked cameras cost virtually nothing compared to satellites or high-altitude drones. They're stealthier than drones, which can be detected and shot down. Ground-level cameras also provide angles impossible from a satellite's bird's-eye view—perfect for reconnaissance, targeting, and "bomb damage assessment" after strikes.
The Accountability Gap
Here's the problem: those with the power to secure these devices rarely suffer the consequences of surveillance. "The manufacturer and owner aren't the victim," notes Beau Woods, former adviser to the US Cybersecurity and Infrastructure Security Agency. "So the victim isn't in a position to control the tool used by the adversary."
Hikvision and Dahua are effectively banned in the US due to security concerns, but millions of their cameras operate worldwide. Neither company responded to requests for comment about the hacking campaign.
The responsibility vacuum means this surveillance technique will persist across future conflicts. "Who's liable, who's responsible, who's accountable?" Woods asks. "The camera itself isn't directly causing harm. But it's part of the kill chain."
This content is AI-generated based on source articles. While we strive for accuracy, errors may occur. We recommend verifying with the original source.
Related Articles
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
CISA orders emergency patches for iOS vulnerabilities exploited by sophisticated Coruna toolkit, revealing how cybercriminals weaponize already-patched flaws
Thoughts
Share your thoughts on this article
Sign in to join the conversation