
Your Security Camera Could Be Scouting Tomorrow's Missile Targets
Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
When Your Doorbell Camera Becomes a Military Asset
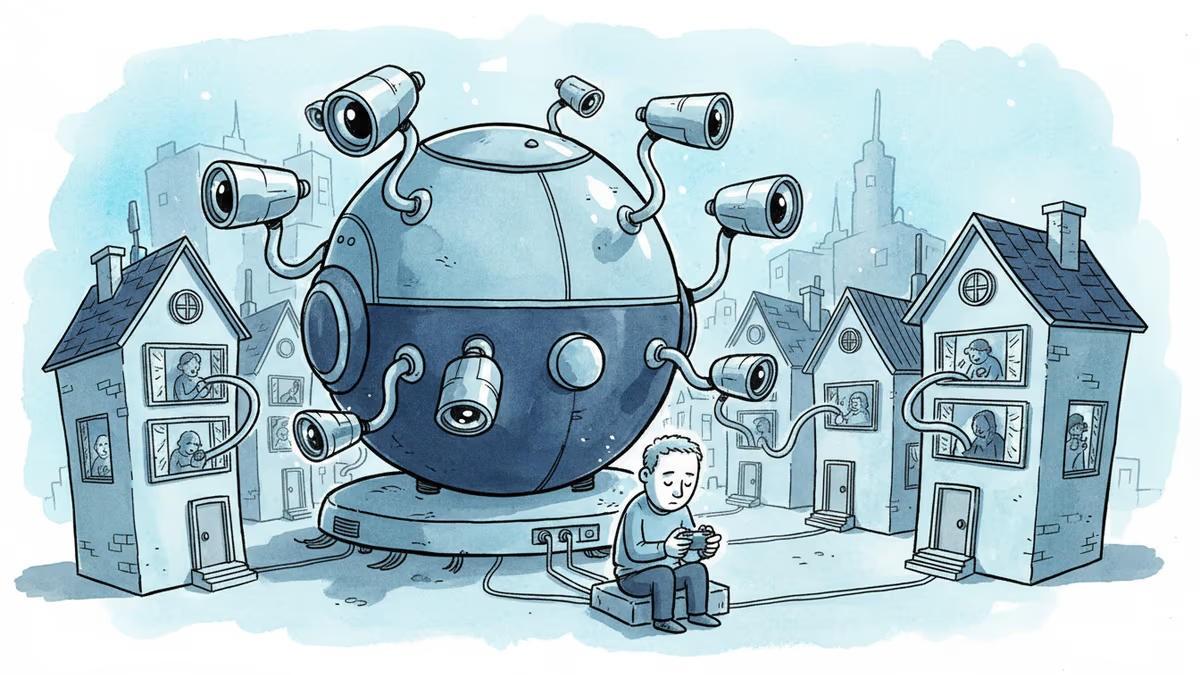
What if the security camera protecting your front door was simultaneously scouting targets for a foreign military? That scenario moved from hypothetical to reality this week, as Israeli security firm Check Point revealed hundreds of hacking attempts targeting consumer-grade security cameras across the Middle East—many timed precisely with Iran's recent missile strikes on Israel, Qatar, and Cyprus.
The hackers weren't after your vacation photos. They wanted something far more valuable: real-time intelligence on bombing targets, strike planning data, and damage assessment capabilities. All delivered through the humble security cameras that millions of people install to feel safer.
The Democratization of Military Surveillance
This isn't Iran's innovation alone. The Financial Times reported that Israeli forces accessed "nearly all" traffic cameras in Tehran, partnering with the CIA to target the air strike that killed Iran's supreme leader. In Ukraine, both sides have turned civilian surveillance networks into military assets—Russia hacking Ukrainian cameras to track troop movements, while Ukrainian hackers hijack Russian cameras to monitor enemy positions.
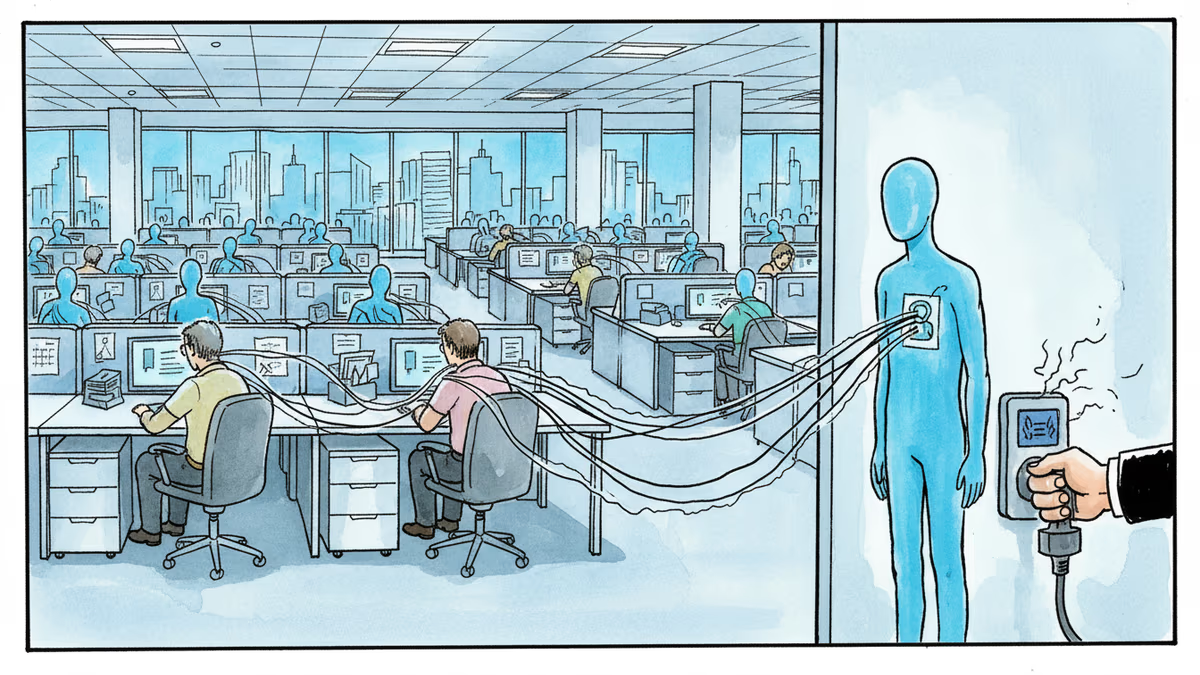
The appeal is obvious: why spend millions on military satellites when you can hack thousands of internet-connected cameras for free? Most consumer security devices ship with default passwords, receive infrequent security updates, and sit on networks with minimal protection. They're the soft underbelly of modern surveillance.
From Tehran to Main Street
For cybersecurity professionals, this represents a fundamental shift in threat modeling. The attack surface isn't just corporate networks or government systems anymore—it's every Ring doorbell, every traffic camera, every security system in a strip mall near a military installation.
Consider the implications for US infrastructure. Military bases, government buildings, and critical facilities are surrounded by civilian cameras. A foreign adversary could theoretically map troop movements, identify security protocols, and plan attacks using nothing but hacked consumer devices.
Amazon and Google have invested heavily in securing their camera ecosystems, but millions of cheaper devices from lesser-known manufacturers remain vulnerable. The Pentagon has already banned certain Chinese-made cameras from military facilities, but what about the ones across the street?
The Privacy-Security Paradox
This creates an uncomfortable paradox for policymakers. Stronger regulations on IoT security could protect against military exploitation—but they might also limit innovation and increase costs for consumers. Meanwhile, the cameras that make us feel safer in our neighborhoods could be making our nations less secure.
The European Union's Cyber Resilience Act aims to mandate security standards for connected devices, but implementation won't begin until 2025. In the US, similar legislation remains stalled in Congress.
The question isn't whether foreign militaries will continue hacking civilian cameras. It's whether we're prepared for a world where our most mundane devices become instruments of war.
Authors
Related Articles

UK Visa Portal, a private immigration service mistaken for an official government site, has been exposing passport scans and selfies of over 100,000 applicants. The breach remains unpatched.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

The same heartbeat reading, DNA sample, or facial scan has radically different legal protections depending on where you live. From 23andMe's bankruptcy to post-Dobbs data weaponization, here's how five legal regimes treat the data your body generates — and why 640 million smartwatch users should care.
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
Thoughts
Share your thoughts on this article
Sign in to join the conversation