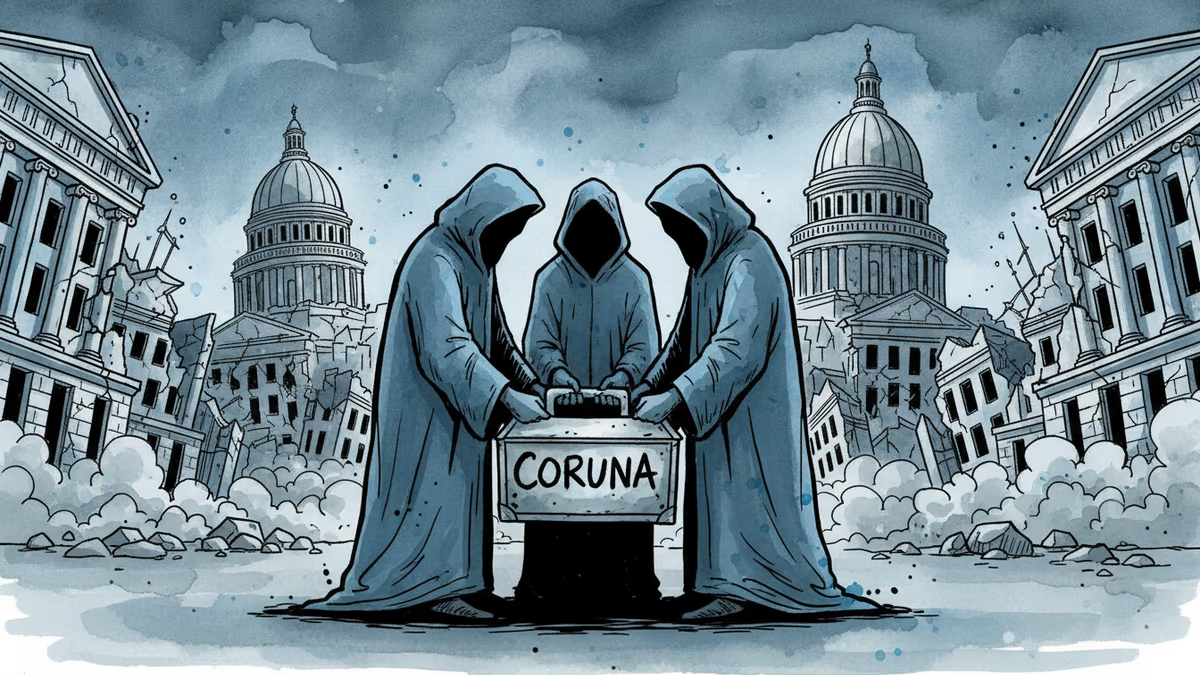
Federal Agencies Breached for 10 Months by 'Second-Hand' Hacking Kit
CISA orders emergency patches for iOS vulnerabilities exploited by sophisticated Coruna toolkit, revealing how cybercriminals weaponize already-patched flaws
10 Months of Federal Agencies Getting Hacked
The Cybersecurity and Infrastructure Security Agency just issued an emergency patch order to federal agencies. The reason? Three separate hacking groups spent 10 months exploiting the same iOS vulnerabilities to breach government systems.
Google's Thursday report revealed these groups all used 'Coruna'—a sophisticated hacking kit that bundled 23 iOS exploits into 5 potent attack chains. This wasn't some amateur operation. The toolkit featured extensive documentation with native English comments and advanced, non-public exploitation techniques.
The 'Used Car' Vulnerability Market
Here's the kicker: by the time Google observed these attacks, Apple had already patched every single vulnerability. So how did the hackers keep succeeding?
Simple. People don't update their phones.
The attackers knew this. They weaponized what security researchers call "second-hand zero-days"—vulnerabilities that were once cutting-edge threats but became accessible tools for anyone targeting outdated systems.
"The core technical value of this exploit kit lies in its comprehensive collection of iOS exploits," Google researchers noted. These weren't script kiddies. The documentation quality and bypass techniques suggested professional-grade development.
Why Even the Government Delays Updates
From IT administrators' perspective: Government agencies often delay updates for legitimate reasons. New iOS versions need security review, compatibility testing with existing infrastructure, and approval through bureaucratic channels. What looks like negligence might actually be cautious protocol.
From users' perspective: But let's be honest—individual government employees probably delayed updates for the same reasons we all do. "It'll slow down my phone," or "I don't want to learn new features right now."
From attackers' perspective: This human tendency to postpone updates creates a predictable attack surface. Why burn a fresh zero-day when you can exploit a six-month-old patch that half your targets haven't installed?
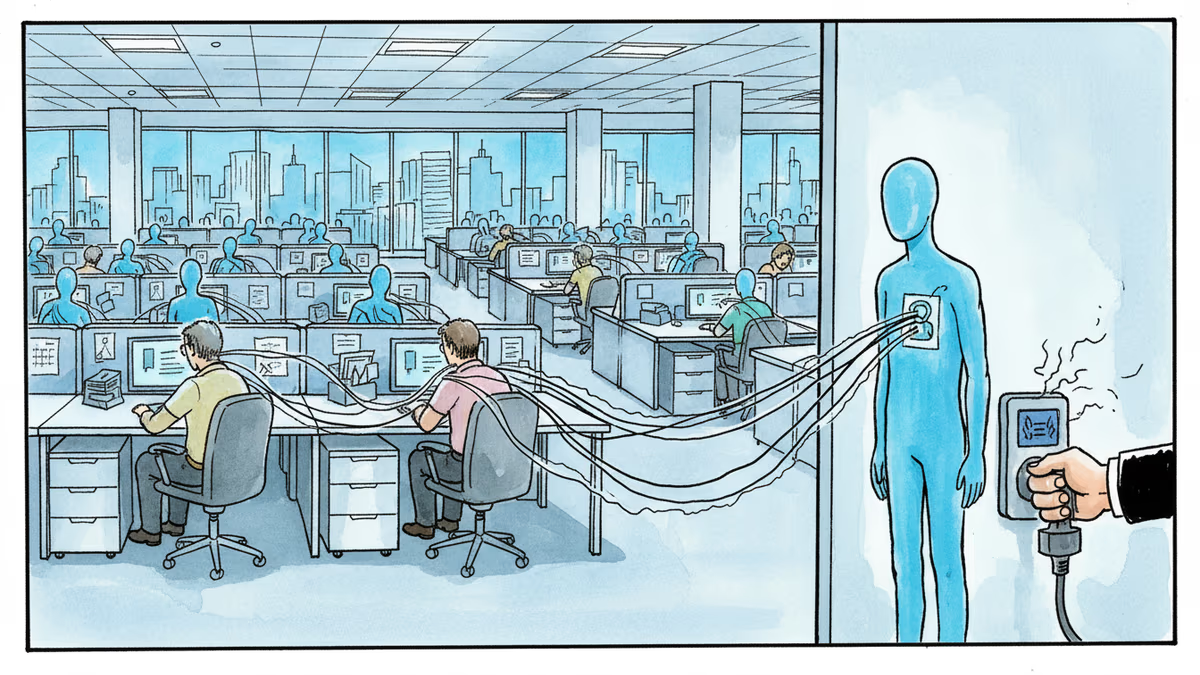
The Enterprise Vulnerability Window
This incident exposes a broader enterprise security challenge. Large organizations—whether government agencies, Fortune 500 companies, or tech startups—face the same dilemma: balancing security updates with operational stability.
Apple releases iOS updates frequently, sometimes weekly. But enterprises can't realistically test and deploy each one immediately. This creates what security experts call the "vulnerability window"—the gap between patch release and deployment where organizations remain exposed.
Cybersecurity professionals argue this is why mobile device management (MDM) systems exist. But even the best MDM can't force users to actually install updates if they keep dismissing notifications.
Government agencies now face pressure to accelerate their update cycles, but this conflicts with their need for thorough security vetting. It's a catch-22: move fast and risk breaking critical systems, or move slowly and risk getting hacked.
The Coruna Ecosystem Reveals Broader Trends
What makes Coruna particularly concerning isn't just its technical sophistication—it's the business model it represents. The toolkit's professional documentation suggests it was designed for sharing or selling among multiple groups.
This points to the maturation of the exploit-as-a-service economy. Instead of each hacking group developing their own tools, they're sharing resources and techniques. It's efficiency through collaboration, just applied to cybercrime.
Tech companies like Google and Apple are essentially playing defense against an increasingly organized offense. The traditional model of "patch and pray" isn't keeping pace with the professionalization of cyber threats.
Authors
Related Articles

UK Visa Portal, a private immigration service mistaken for an official government site, has been exposing passport scans and selfies of over 100,000 applicants. The breach remains unpatched.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
Thoughts
Share your thoughts on this article
Sign in to join the conversation