
The Public Wi-Fi Paradox: Your Free Connection Is a Security Minefield
Free public Wi-Fi isn't a utility; it's a transaction. PRISM analyzes the hidden security risks and why treating every connection as hostile is the new standard.
The Lede: The Unmanaged Risk in Your Pocket
The free Wi-Fi at your airport lounge or local coffee shop isn't a utility; it's an unmanaged, high-risk extension of your personal and corporate network. For the busy executive, every connection to these public networks is a roll of the dice, expanding your organization's attack surface to an insecure environment you don't control. The perceived convenience masks a critical vulnerability that threat actors actively exploit.
Why It Matters: The True Cost of 'Free'
The ubiquity of public Wi-Fi has created a dangerous paradox. As connectivity has become an ambient expectation, our collective security posture has dangerously eroded. This has profound second-order effects:
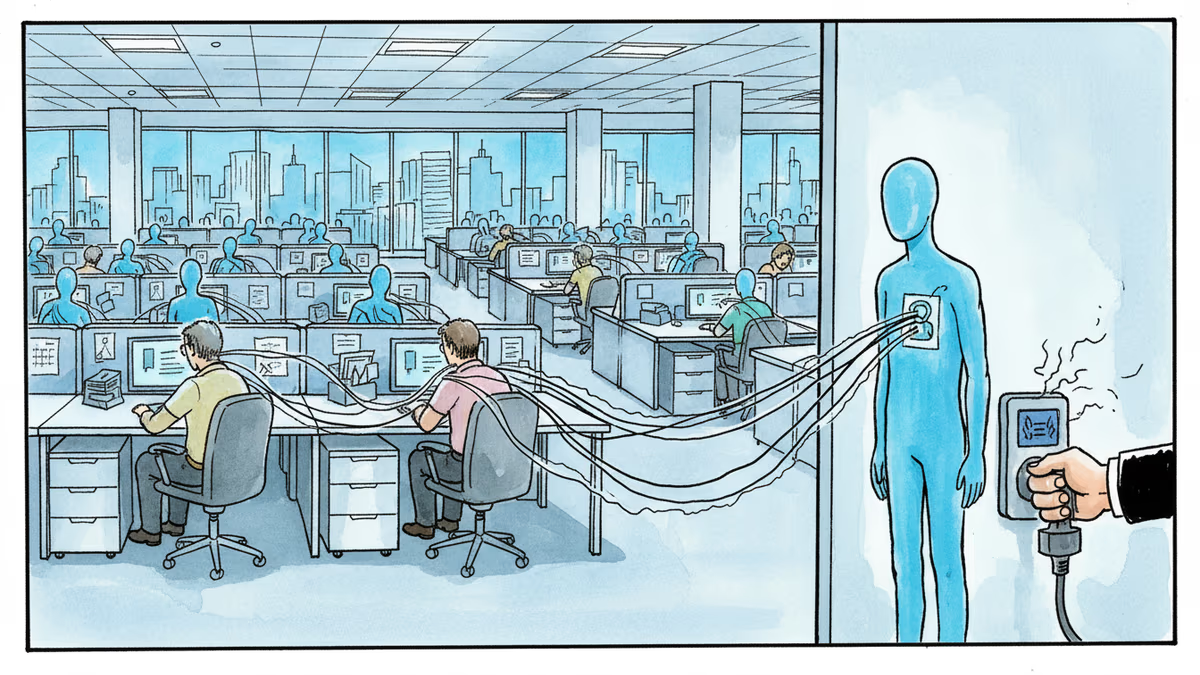
- The Normalization of Data Harvesting: Venues offering 'free' Wi-Fi are not altruistic. They are data brokers. The price of admission is your email address, which is immediately funneled into marketing databases, or worse, your browsing habits, which are tracked and sold.
- The Distributed Workforce's Achilles' Heel: The 'work-from-anywhere' revolution is built on a foundation of insecure public infrastructure. A single employee accessing sensitive corporate data from a compromised coffee shop network can trigger a multi-million dollar breach.
- The Consumer as the Product: This ecosystem thrives on a transactional relationship where user data is the currency. This trains consumers to trade privacy for convenience, a behavioral shift with long-term consequences for digital rights.
The Analysis: From Paid Amenity to Insecure Expectation
In the early 2000s, public Wi-Fi was a premium, paid service from providers like Boingo. It was a deliberate act to connect. Today, it’s a 'freemium' expectation, and the underlying technology has not kept pace with the security threats. Most public hotspots are open, unencrypted networks, making them trivial environments for Man-in-the-Middle (MitM) attacks. An attacker on the same network can easily intercept traffic, steal credentials, and monitor activity.
The advice to use a VPN or a disposable email address treats the symptom, not the disease. The core issue is a fundamental misalignment: we are placing 21st-century data needs onto a 20th-century security architecture. The convenience has completely overshadowed the inherent risk, and platform providers have done little to enforce higher security standards like WPA3 or Hotspot 2.0 (Passpoint) which would automate secure connections.
PRISM's Take: Treat Every Network as Actively Hostile
Public Wi-Fi is a legacy convenience clashing with modern security realities. The default action should no longer be to connect, but to question the necessity. Simple tips and tricks are no longer sufficient; a fundamental mindset shift is required. Every public network must be treated as actively hostile until proven otherwise. For most tasks, your smartphone's secure cellular hotspot is a vastly superior and safer alternative. The convenience of 'free' Wi-Fi is a siren song that often leads directly to data exposure and compromise. In the current threat landscape, the price of free is simply too high.
Authors
Related Articles
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Age verification laws are turning VPNs from a niche privacy tool into everyday infrastructure. What happens when governments decide to shut the door?

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
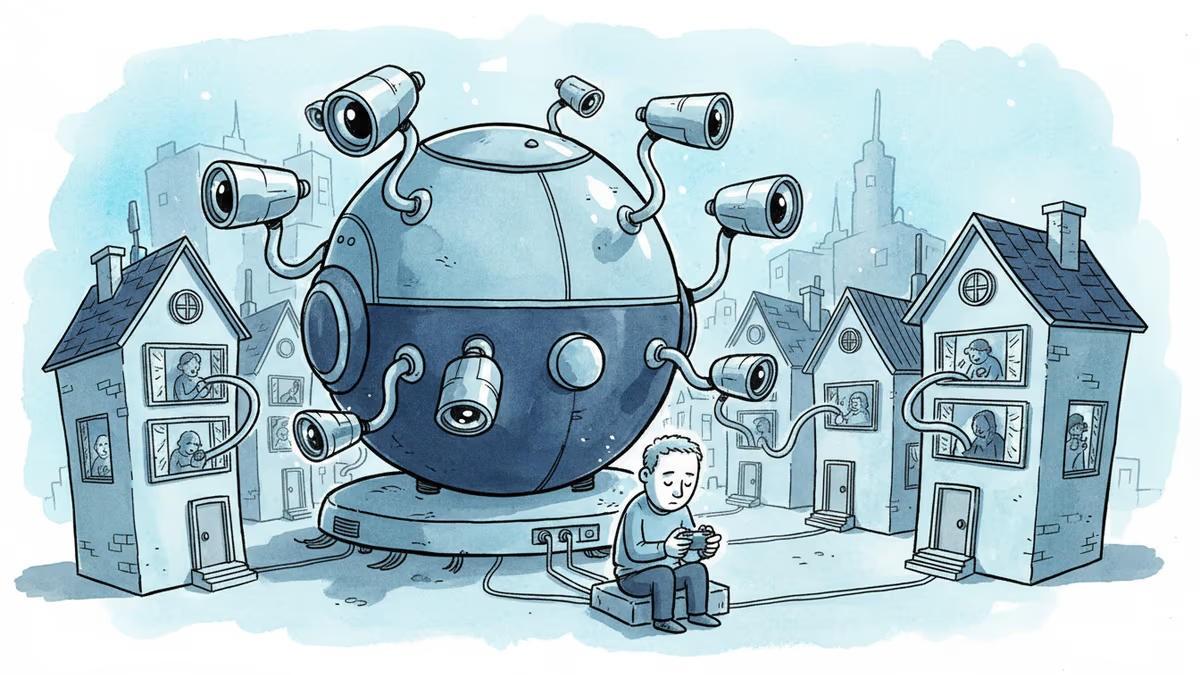
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
Thoughts
Share your thoughts on this article
Sign in to join the conversation