
Government Hacking Tools Leaked to Cybercriminals
US government iPhone hacking tools have leaked to Russian spies and Chinese hackers. The 'Coruna' exploit kit can breach iOS devices up to 17.2.1 through simple web visits
23 Vulnerabilities Chained Together to Break iPhones
A single hacking toolkit is making a dangerous journey around the world. Meet 'Coruna' – a sophisticated exploit kit believed to be created by the US government that can breach iPhone defenses in five different ways. All it takes is clicking one malicious link.
The problem? This tool has escaped government control. First spotted in February 2025 during a surveillance operation for a government customer, it later surfaced in Russian espionage campaigns targeting Ukrainians. Most recently, it's been used by financially motivated hackers in China.
From Government Asset to Criminal Weapon
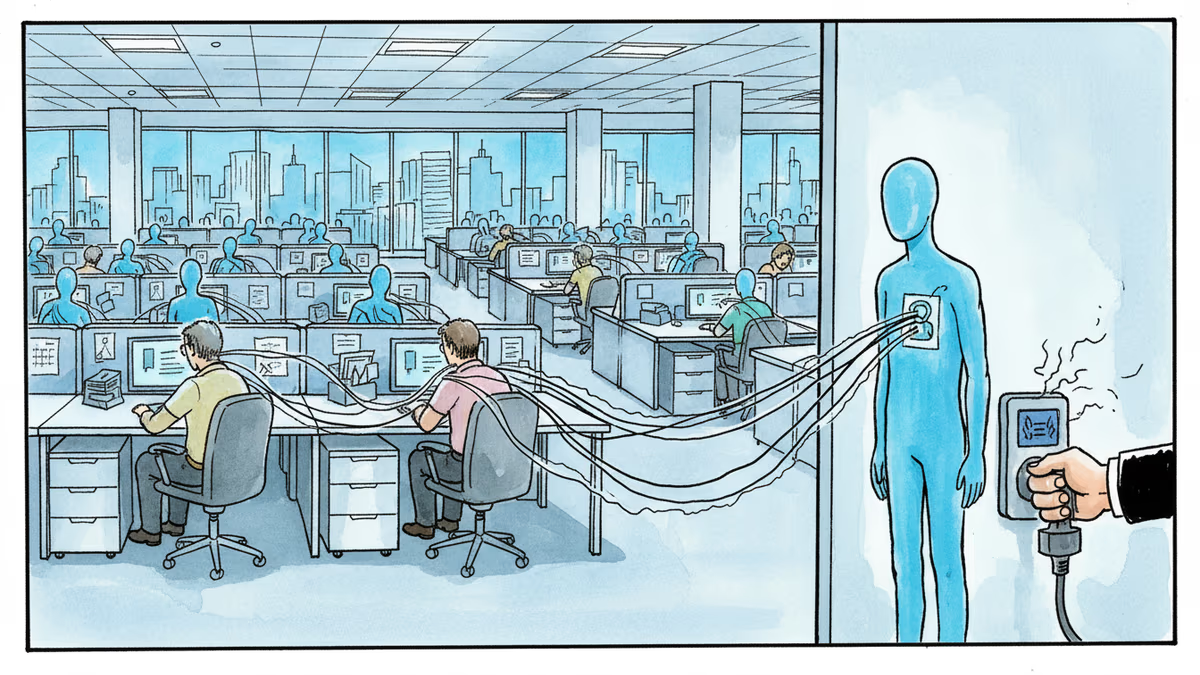
Google's security researchers are sounding the alarm about an emerging "secondhand exploit" market. Government-grade hacking tools are leaking into the hands of cybercriminals who want to extract maximum profit from these powerful capabilities.
Mobile security firm iVerify reverse-engineered the Coruna kit and linked it to the US government based on similarities to previously attributed American hacking tools. Their analysis reveals a troubling reality about cyber weapon proliferation.
"The more widespread the use, the more certain a leak will occur," iVerify warned. "These tools will find their way into the wild and will be used unscrupulously by bad actors."
No Safe Harbor for iPhone Users
Coruna's reach is extensive. It targets iPhone models running iOS 13 through 17.2.1, which was released in December 2023. That means millions of devices remained vulnerable well into 2024.
The attack method is elegantly simple: "watering hole" attacks that compromise devices through malicious website visits. No app installation required, no complex user interaction needed. Just visit the wrong site, and your iPhone is compromised.
Intriguingly, Coruna contains components previously used in "Operation Triangulation," a hacking campaign that Russian cybersecurity firm Kaspersky claimed in 2023 was used by the US government to target its employees' iPhones.
A Pattern of Leaks
Government hacking tool leaks aren't unprecedented. In 2017, the NSA's Windows hacking tool "EternalBlue" was stolen and later weaponized in North Korea's WannaCry ransomware attack that crippled hospitals and businesses worldwide.
More recently, Peter Williams, former head of US defense contractor L3Harris Trenchant, was sentenced to over seven years in prison for stealing and selling eight exploits to brokers known to work with the Russian government. Prosecutors said Williams' exploits could hack "millions of computers and devices" globally.
The Stakeholder Divide
Government agencies argue these tools are essential for national security and law enforcement. They need capabilities to investigate serious crimes and counter foreign threats.
Privacy advocates see this as validation of their warnings about government backdoors. They argue that any vulnerability created for "good guys" will eventually be exploited by "bad guys."
Tech companies find themselves caught in the middle, trying to balance security with compliance demands while protecting user privacy.
Cybersecurity professionals are pragmatic: they know these leaks are inevitable and focus on detection and mitigation rather than prevention of government tool development.
Authors
Related Articles

UK Visa Portal, a private immigration service mistaken for an official government site, has been exposing passport scans and selfies of over 100,000 applicants. The breach remains unpatched.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.

CBP admits buying location data from ad industry while Meta contractors watch users in bathrooms through smart glasses. The digital privacy boundary is crumbling.
Thoughts
Share your thoughts on this article
Sign in to join the conversation