
Cracking Passwords for $600: The Mandiant NTLMv1 rainbow table database Release
Mandiant has released an NTLMv1 rainbow table database, allowing passwords to be cracked in under 12 hours with $600 hardware. A wake-up call for legacy security.
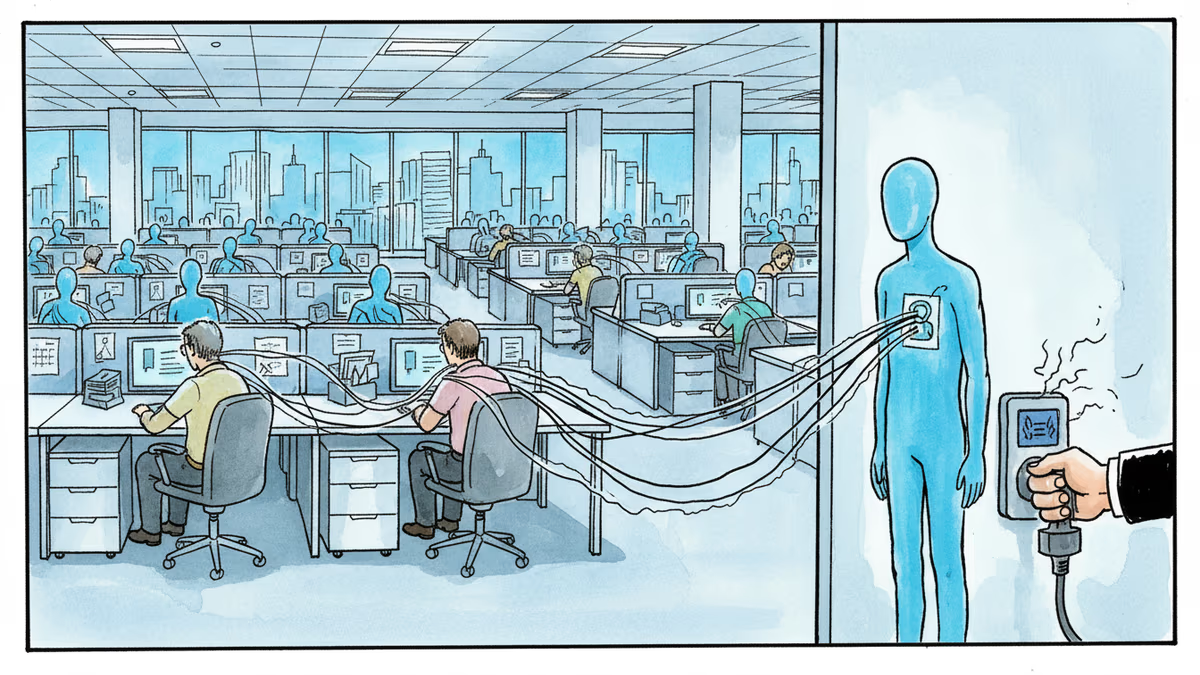
Legacy security just met its executioner. Cybersecurity firm Mandiant has released a massive rainbow table database designed to crack any administrative password protected by Microsoft’s aging NTLMv1 hashing algorithm.
Mandiant NTLMv1 rainbow table database: A death sentence for legacy auth
By making this database public, Mandiant is essentially forcing the hands of IT administrators who haven't yet migrated to more secure protocols. NTLMv1 has been known to be weak for over two decades, but its limited keyspace makes it an easy target for precomputed hash matching. Mandiant’s release drastically lowers the barrier to entry for such attacks.
| Metric | Requirement / Result |
|---|---|
| Hardware Cost | Under $600 USD |
| Cracking Time | Less than 12 hours |
| Platform | Google Cloud |
| Target | Net-NTLMv1 (SMB, Network Auth) |
New ammo for security professionals and hackers alike
According to Mandiant, the database allows researchers to recover passwords in under 12 hours using consumer-grade hardware. While intended as a tool for defenders to prove vulnerabilities, it’s equally accessible to malicious actors. The data specifically targets Net-NTLMv1 passwords used in network authentication, such as SMB file sharing.
Authors
Related Articles

UK Visa Portal, a private immigration service mistaken for an official government site, has been exposing passport scans and selfies of over 100,000 applicants. The breach remains unpatched.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
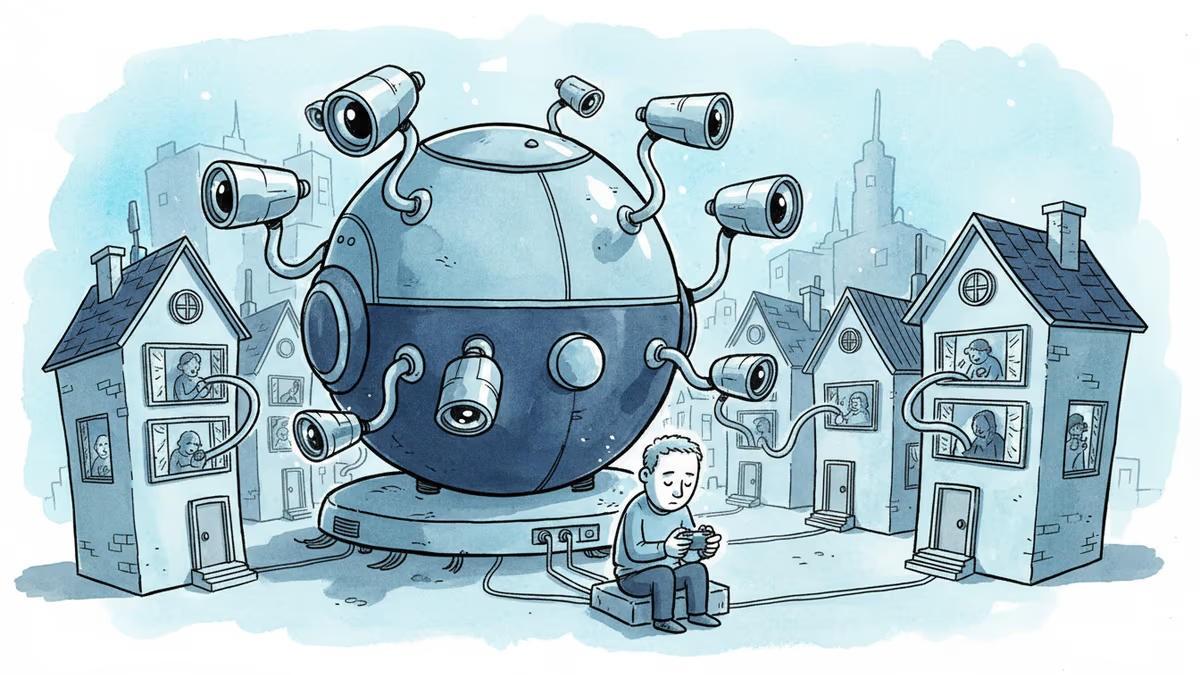
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
Thoughts
Share your thoughts on this article
Sign in to join the conversation