LinkedIn Was Scanning Your Browser. Did You Know?
Two class action lawsuits allege LinkedIn secretly scanned users' browsers to identify installed extensions. Here's what happened, who's behind it, and why it matters.
You logged into LinkedIn to check job postings. LinkedIn, it turns out, may have been checking something about you.
What Happened
On Monday, two separate class action complaints landed in the US District Court for the Northern District of California — filed by two different law firms, on behalf of two different plaintiffs, but with the same central allegation: LinkedIn scanned users' browsers without consent to identify which extensions they had installed.
Both suits seek to represent all LinkedIn users in the United States — a pool estimated at over 200 million people. The complaints lean heavily on a report dubbed 'BrowserGate,' published by a German entity called Fairlinked, which describes itself as a trade association and advocacy group for commercial LinkedIn users.
The timing is notable. This isn't LinkedIn's first legal skirmish of the year.
The Backstory Gets Complicated
Here's where the story gets layered. Fairlinked appears to be operated by the same people behind Teamfluence, an Estonian software company that sued LinkedIn in Munich in January 2026. LinkedIn's position on Teamfluence is pointed: the company distributed a browser extension that scraped LinkedIn user data in violation of its terms of service, and its accounts were suspended as a result.
In other words, the entity that produced the 'BrowserGate' report — the document now anchoring two US class action lawsuits — is run by people who were themselves sanctioned by LinkedIn for allegedly scraping user data.
That doesn't automatically make the underlying privacy allegations false. But it does mean the courtroom drama here has more than one protagonist with skin in the game. Whether this is whistleblowing or litigation strategy is a question worth sitting with.
Why This Matters Beyond the Headlines
Browser fingerprinting and extension detection are not new techniques. Security researchers, ad-tech companies, and fraud prevention systems have used them for years. The legal and ethical question isn't whether the technology exists — it's whether deploying it on users without explicit disclosure crosses a line.
For cybersecurity professionals, the stakes are immediate. Browser extensions can reveal a lot: which password managers someone uses, whether they're running ad blockers or VPNs, even which competitor-analysis or productivity tools they rely on. In a professional networking context, that information carries weight.
For privacy advocates, the concern is structural. LinkedIn is owned by Microsoft, one of the largest data ecosystems on the planet. If a platform can silently audit your browser environment, what else is being observed that users haven't been told about?
For LinkedIn itself, the defense rests on platform integrity. Scraping bots and automated tools are a genuine threat to professional networks. If browser scanning was a security measure to detect such tools, the company will argue it had legitimate grounds — and that the real bad actors were the scrapers, not the scanner.
Three Seats at the Table
Users are left with a familiar discomfort: discovering that a platform they trusted was collecting information they didn't know they were sharing. Even if a court ultimately sides with LinkedIn, the reputational cost of the 'we were watching your browser' headline is real.
Regulators are watching for precedent. The US still lacks a comprehensive federal privacy law. How this case resolves could help draw a clearer line on what platforms are permitted to observe about users' local environments — a question that extends well beyond LinkedIn.
Competitors and the broader industry are quietly attentive. If LinkedIn loses, every platform that uses similar detection techniques will need to revisit its disclosure practices. If LinkedIn wins, the ruling may effectively greenlight a range of browser-side monitoring behaviors that users currently have no visibility into.
Authors
Related Articles
GitHub confirmed hackers stole data from 3,800 internal repositories via a poisoned VS Code extension. Here's why developer tools are now the most dangerous attack surface in tech.
Google's Gmail Live lets you ask your inbox questions out loud. Announced at I/O 2026, it's AI's pitch to skeptics — and a reminder of how much Google already knows about you.
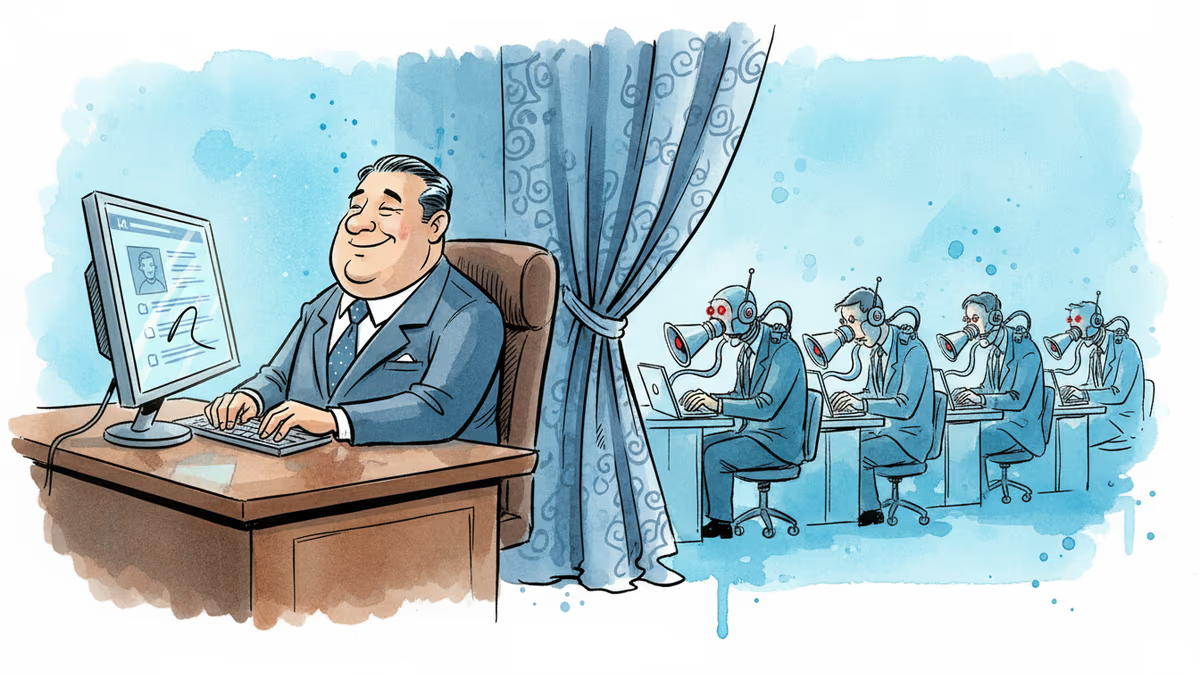
Filipino virtual assistants using AI to ghost-manage LinkedIn profiles for executives is now a structured industry. 30 comments a day, fake engagement rings, and a platform struggling to tell real from fabricated.

OpenAI has reorganized for the second time in a month, merging ChatGPT and Codex into a single agentic platform under president Greg Brockman's unified product leadership.
Thoughts
Share your thoughts on this article
Sign in to join the conversation