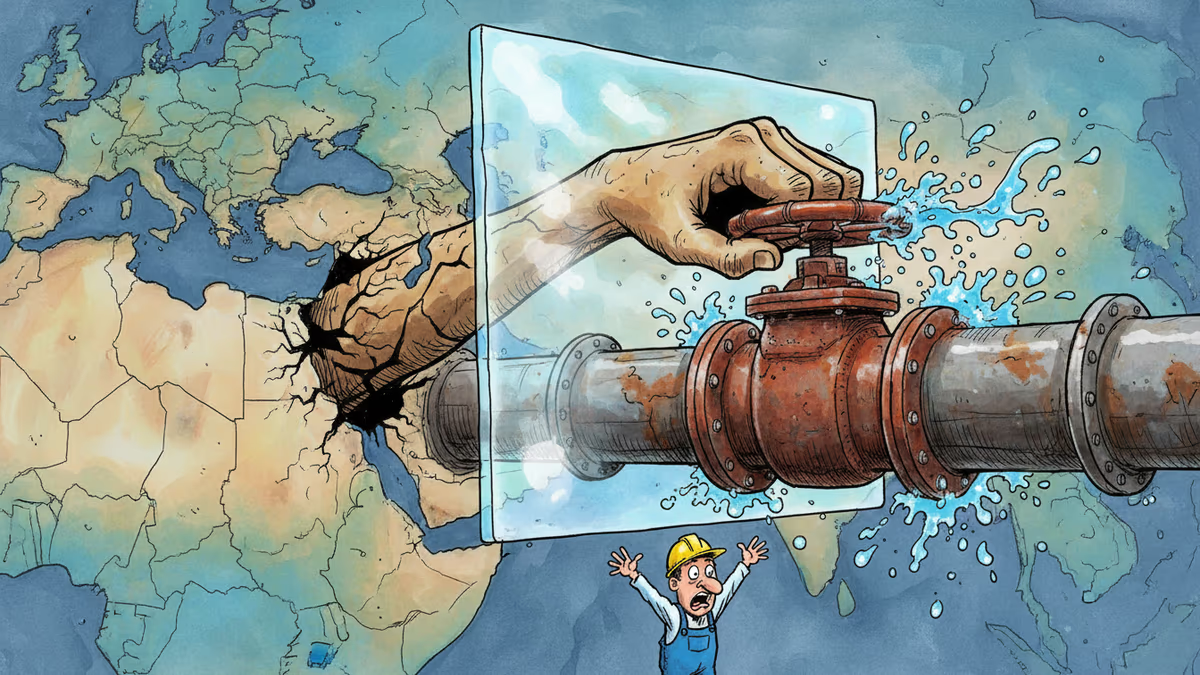
Iran Is Now Turning Water Taps Into Weapons
Iranian government-backed hackers have escalated from data theft to physically manipulating U.S. water, power, and local government control systems. A joint FBI-NSA-CISA-DOE advisory confirms operational disruption has already occurred.
Someone turned a valve. No one in the building did it.
On April 7, the FBI, NSA, CISA, and the U.S. Department of Energy issued a rare joint advisory: Iranian government-backed hackers have moved beyond stealing data. They are now reaching into the physical systems that pump your water, run your power grid, and keep local government facilities operational — and manipulating them remotely. The advisory confirmed that these intrusions have already caused "operational disruption and financial loss." The targets haven't been named. The damage is real.
What Was Actually Attacked — and Why It Matters
The technical targets sound dry: programmable logic controllers (PLCs) and supervisory control and data acquisition (SCADA) systems. But strip away the jargon and you're left with something visceral. These are the devices that open and close water valves, regulate pump pressure, manage power flow, and control industrial equipment across America's essential services. They are, in effect, the nervous system of physical infrastructure.
According to the four agencies, the hackers exploited internet-facing versions of these systems — a known and persistent vulnerability in aging infrastructure — and did two things. First, they manipulated what operators see on their screens: changing displayed readings so that real problems appear normal, or normal conditions appear alarming. Second, they altered the project files that store device configurations, the equivalent of quietly rewriting the rulebook the machines operate by. The agencies were careful not to name specific facilities or companies, but the confirmation that disruption has already occurred is significant.
The Geopolitical Fuse
Timing is everything here. The agencies explicitly linked this escalation to the ongoing U.S.-Israel conflict with Iran, which began on February 28 when airstrikes killed Iran's supreme leader. Since then, an Iranian government-linked hacking group called Handala has been running an unusually aggressive campaign.
Handala's recent hits read like a threat actor's greatest hits reel. The group breached U.S. medical technology giant Stryker and used the company's own security tools to remotely wipe thousands of employee devices. It leaked portions of FBI Director Kash Patel's private email account. And Iran hasn't limited itself to cyberspace: U.S.-owned and operated data centers across the Middle East have been struck by missiles and airstrikes, causing measurable disruption to regional cloud services.
The advisory landed on the same day President Trump posted a social media message warning that "a whole civilization will die tonight" if Iran didn't agree to open the Strait of Hormuz by end of day. Diplomatic ultimatum and cyber warning, issued within hours of each other. Whether that's coordination or coincidence, the effect is the same: the pressure is escalating on every front simultaneously.
Three Stakeholders, Three Very Different Problems
For the intelligence community, this advisory serves a dual purpose. It's a warning to operators, yes — but it's also a public attribution, a way of saying: we know who you are, we know what you did, and we're telling the world. Public attribution is a tool of deterrence, even when deterrence is clearly not working as hoped.
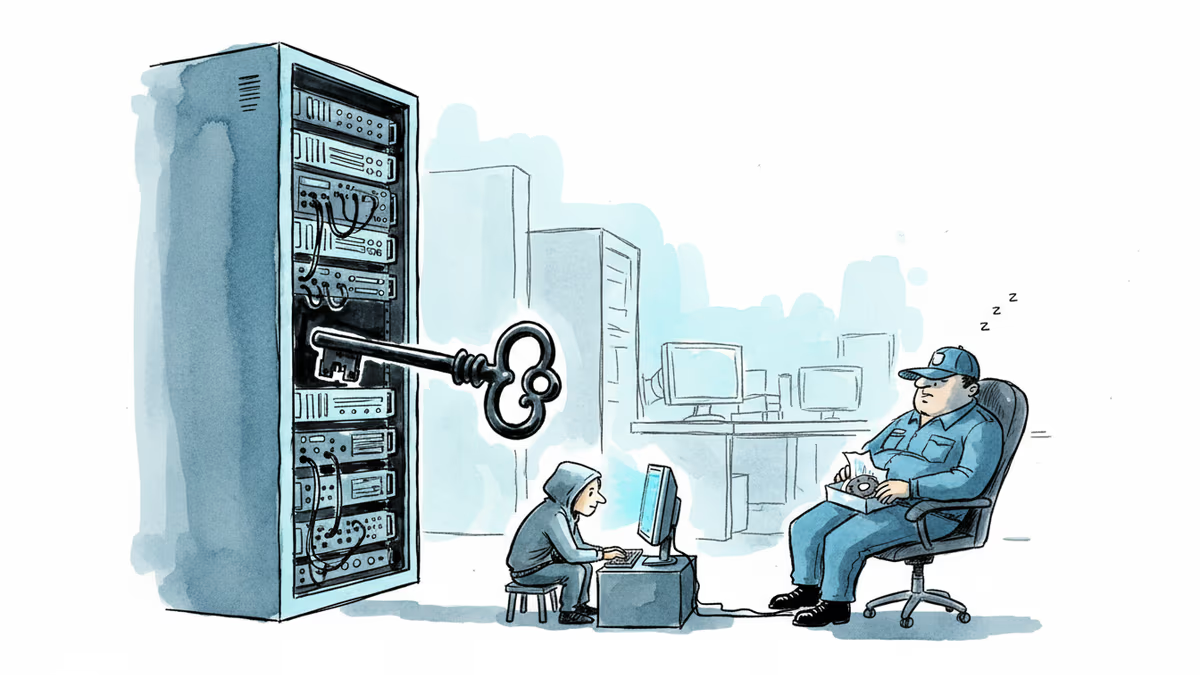
For infrastructure operators — the water utilities, municipal power managers, local government IT teams — the advisory lands differently. Many of these organizations run on thin budgets, aging equipment, and skeleton cybersecurity staff. The PLCs and SCADA systems now being targeted were often designed before internet connectivity was assumed, then networked later for operational convenience. Patching them is slow, expensive, and sometimes impossible without taking systems offline. The advisory tells them they're targets. It doesn't solve the underlying problem of why they're vulnerable.
For the private sector broadly, Stryker's breach is the most instructive case study. The attackers didn't need zero-days or exotic malware. They used the company's own security tools to cause destruction. This is the adversary's evolution: instead of breaking through defenses, exploit the defenses themselves. Every enterprise security team should be asking whether their tooling could be turned against them.
The Structural Vulnerability That Outlasts Any Conflict
Here's the uncomfortable truth that no ceasefire will fix: the attack surface isn't going anywhere. Thousands of internet-connected industrial control devices remain exposed, many with default credentials unchanged, many running software with known, unpatched vulnerabilities. CISA maintains a public catalog of these known-exploited vulnerabilities. The list grows faster than the patching rate.
The U.S. government has pushed for stronger ICS security standards for years, but enforcement is uneven and the economics are difficult. Upgrading a small municipal water system's control infrastructure can cost millions — money that most small utilities simply don't have. The gap between "what should be done" and "what can be done" is where adversaries like Handala operate.
Iran has now demonstrated, with confirmed results, that this gap is exploitable at scale. The question isn't whether other state actors have noticed. They have.
Authors
Related Articles
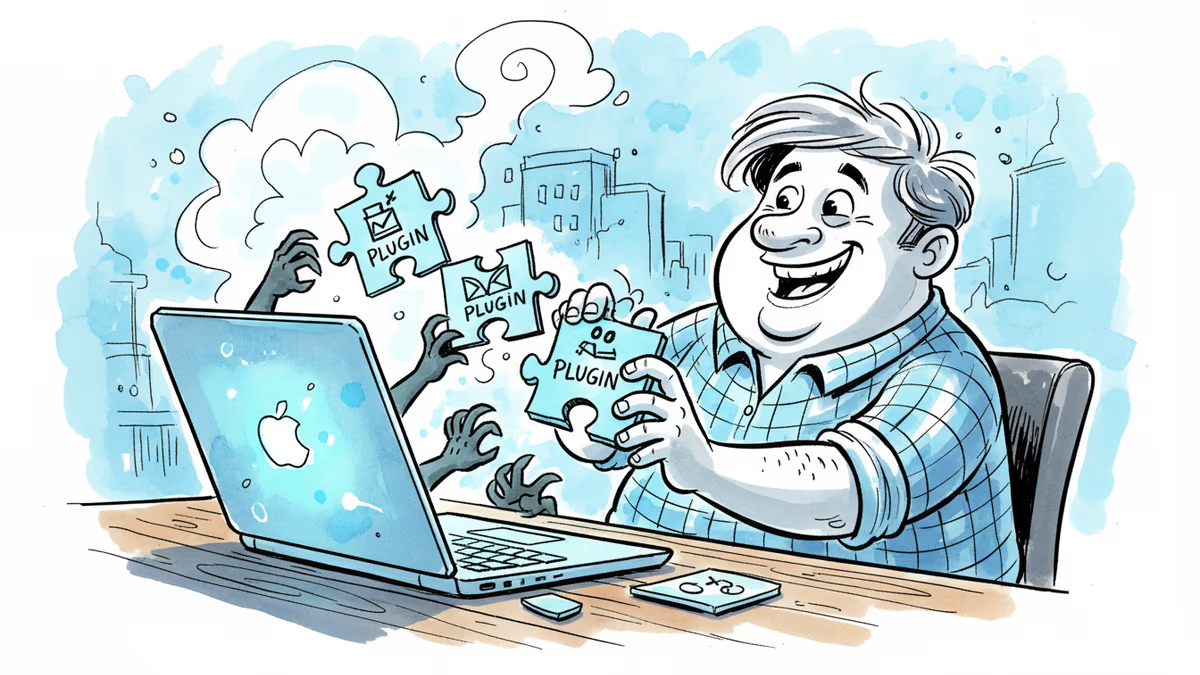
GitHub confirmed hackers stole data from 3,800 internal repositories via a poisoned VS Code extension. Here's why developer tools are now the most dangerous attack surface in tech.

A Utah woman was sentenced to life in prison partly because of her Google searches and deleted texts. The Kouri Richins case reveals how digital footprints have become the courtroom's most reliable witness.
Dirty Frag gives low-privilege users root access on virtually every Linux distro. The exploit code leaked three days ago. Microsoft says attackers are already experimenting with it.
OpenAI's new Daybreak initiative uses the Codex AI agent to find and patch security vulnerabilities before attackers do—putting it in direct competition with Anthropic's secretive Claude Mythos.
Thoughts
Share your thoughts on this article
Sign in to join the conversation