
One Angry Researcher Just Handed Hackers the Keys
A disgruntled security researcher published working exploit code for three unpatched Windows Defender vulnerabilities. Hackers weaponized it within days. Here's what it means for everyone running Windows.
The code went online. The attacks followed within days.
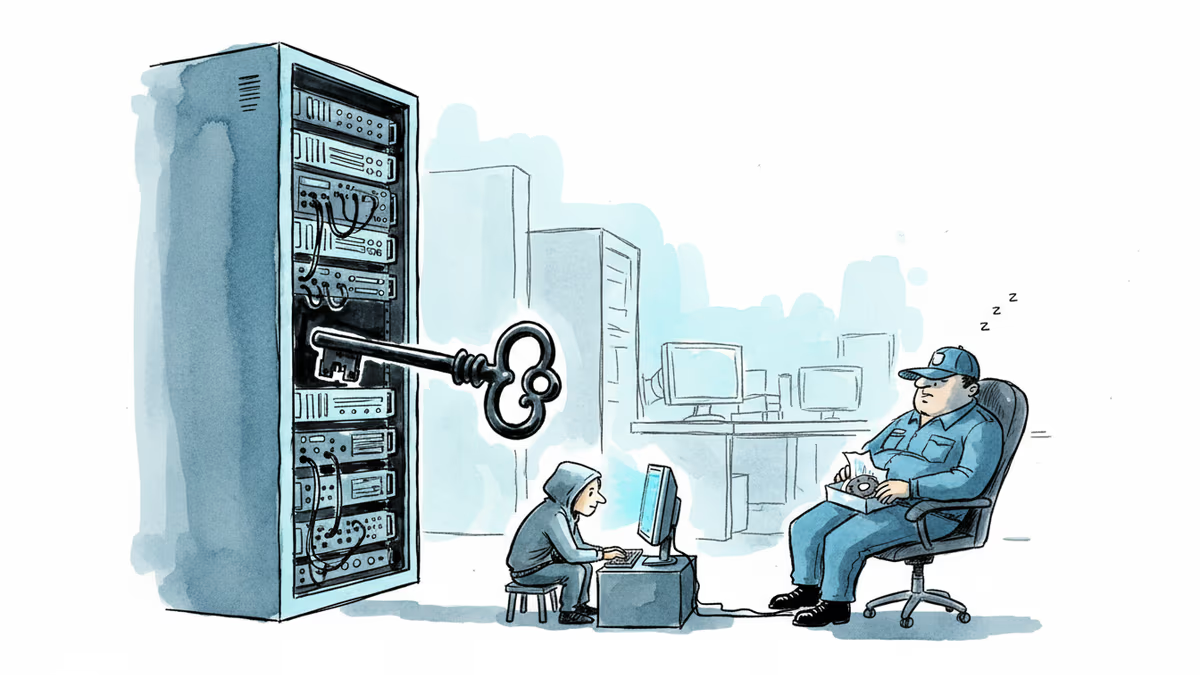
A security researcher, apparently fed up with Microsoft, posted working exploit code for unpatched Windows vulnerabilities on their public GitHub page. Hackers picked it up almost immediately and used it to breach at least one real organization. Cybersecurity firm Huntress confirmed the attacks on Friday — and two of the three vulnerabilities involved still have no patch.
What Actually Happened
The researcher, who operates under the handle Chaotic Eclipse, published the first exploit earlier this month alongside a pointed message: "I was not bluffing Microsoft and I'm doing it again." They signed off with a sardonic note of thanks to Microsoft's Security Response Center — the team responsible for handling exactly these kinds of reports.
Over the following days, Chaotic Eclipse published two more exploits, dubbed UnDefend and RedSun, joining the first, called BlueHammer. All three target Windows Defender — the antivirus software that ships with every copy of Windows — and all three allow an attacker to escalate from a standard user to full administrator access on an affected machine.
Microsoft patched BlueHammer earlier this week. UnDefend and RedSun remain unpatched as of today.
Huntress researcher John Hammond put it plainly: "With these being so easily available now, and already weaponized for easy use, for better or for worse I think that ultimately puts us in another tug-of-war match between defenders and cybercriminals."
The Disclosure Dilemma
This isn't a new problem. It has a name: full disclosure.
The standard playbook goes like this: a researcher finds a flaw, quietly reports it to the vendor, the vendor investigates and patches it, and both parties agree on when the details go public. Microsoft calls this "coordinated vulnerability disclosure" and reiterated its support for the practice in a statement this week.
But the playbook only works when both sides are talking. When a vendor goes quiet, drags its feet, or disputes the severity of a finding, researchers are left in an uncomfortable position — sitting on dangerous knowledge with no leverage. Some choose to go public as a pressure tactic. Chaotic Eclipse went further: not just describing the vulnerabilities, but publishing ready-to-run exploit code that anyone could deploy with minimal technical skill.
That last step is what separates a warning shot from an open invitation.
Three Ways to Read This
For enterprise security teams, this is a reminder that the threat landscape doesn't wait for patch cycles. Windows Defender runs on an estimated 1.4 billion Windows devices worldwide. When a working exploit for it hits GitHub, the question isn't whether attackers will use it — it's how fast. Security teams running unpatched Windows environments right now are in a race they didn't choose to enter.
For Microsoft, the deeper problem is reputational. The company hasn't disclosed what went wrong in its relationship with Chaotic Eclipse, but the fact that a researcher felt compelled to publicly mock MSRC leadership while dropping exploit code suggests the breakdown was serious. Bug bounty programs and researcher relations exist precisely to prevent this scenario — and this time, they failed.
For the security research community, the reaction is genuinely split. Some researchers argue that full disclosure — even with exploit code — is the only tool that reliably forces vendors to act. Others argue that publishing weaponized code crosses a line, turning a legitimate grievance into collateral damage for innocent organizations. Both positions have merit, and neither fully resolves the tension.
What Comes Next
Microsoft has not given a public timeline for patching UnDefend or RedSun. Until those fixes arrive, organizations are advised to monitor for unusual privilege escalation activity, restrict local user permissions where possible, and treat any anomalous Windows Defender behavior as a potential indicator of compromise.
Hammond framed the immediate reality bluntly: "Defenders frantically try to protect against ill-intended actors who rapidly take advantage of these exploits… especially now as it is just ready-made attacker tooling."
The researcher Chaotic Eclipse has not responded to press inquiries.
Authors
Related Articles

A critical vulnerability in Starlette—downloaded 325 million times per week—puts millions of AI agent servers at risk, exposing stored credentials for email, databases, and third-party services.
GitHub confirmed hackers stole data from 3,800 internal repositories via a poisoned VS Code extension. Here's why developer tools are now the most dangerous attack surface in tech.

A Utah woman was sentenced to life in prison partly because of her Google searches and deleted texts. The Kouri Richins case reveals how digital footprints have become the courtroom's most reliable witness.
Dirty Frag gives low-privilege users root access on virtually every Linux distro. The exploit code leaked three days ago. Microsoft says attackers are already experimenting with it.
Thoughts
Share your thoughts on this article
Sign in to join the conversation