Your Phone Has a Hidden OS. Google Just Found a Hole In It.
Google's Project Zero proved Pixel modem firmware can be remotely exploited. The fix for Pixel 10? Rust. Here's why that matters—and why the rest of the industry is watching.
Your phone's screen is off. Your apps are closed. You think you're safe. The modem disagrees.
While Android's security model gets regular scrutiny, software updates, and public audits, there's a quieter operating system running beneath all of it — the cellular modem's baseband firmware. It's always on, always connected, and until recently, largely overlooked as an attack surface. Google's Project Zero team just changed that conversation by demonstrating remote code execution on Pixel phone modems over the internet. No physical access. No user interaction required.
The Problem Hiding in Plain Sight
Modem firmware is one of the last great bastions of legacy code in consumer electronics. Built to comply with 3GPP cellular standards developed over decades, the baseband is written almost entirely in C and C++ — languages that are fast and hardware-friendly, but require developers to manage memory manually. That's a problem.
Manual memory management means human error, and human error in this context means buffer overflows, use-after-free bugs, and memory leaks. These aren't theoretical vulnerabilities — they're the bread and butter of real-world exploits. When they exist in a component that sits below the main OS, handles all incoming radio data, and runs with elevated privileges, the consequences can be severe: an attacker could potentially gain a foothold on your device without you ever clicking a single suspicious link.
The uncomfortable truth is that the industry has known about this class of problem for years. The reason nothing changed faster comes down to two words: technical debt. Modem vendors have been layering code on top of code since the 2G era. Rewriting it from scratch isn't just expensive — it risks breaking the precise real-time behavior that keeps calls connected and data flowing.
Google's Pragmatic Fix
Google's answer for the Pixel 10 wasn't to burn it all down and start over. Instead, the team took a surgical approach: identify the highest-risk components — the parsers and protocol handlers that first touch untrusted data from the network — and rewrite those specific pieces in Rust.
Rust is a systems programming language designed to make memory safety guarantees at compile time. It physically prevents entire categories of bugs — the same bugs that enable the exploits Project Zero demonstrated — from ever making it into production binaries. The compiler rejects unsafe code before it ships.
This hybrid strategy is notable precisely because it's realistic. You don't need to replace 100% of legacy firmware to meaningfully reduce risk. Protecting the attack surface's most exposed edges — the entry points for external data — can close the most dangerous doors without demanding a full architectural overhaul.
Who's Watching, and Who Should Be
The cybersecurity community's reaction has been cautiously positive. Replacing even a fraction of modem code with memory-safe alternatives is a meaningful step, and Google publishing its methodology creates a blueprint others can follow.
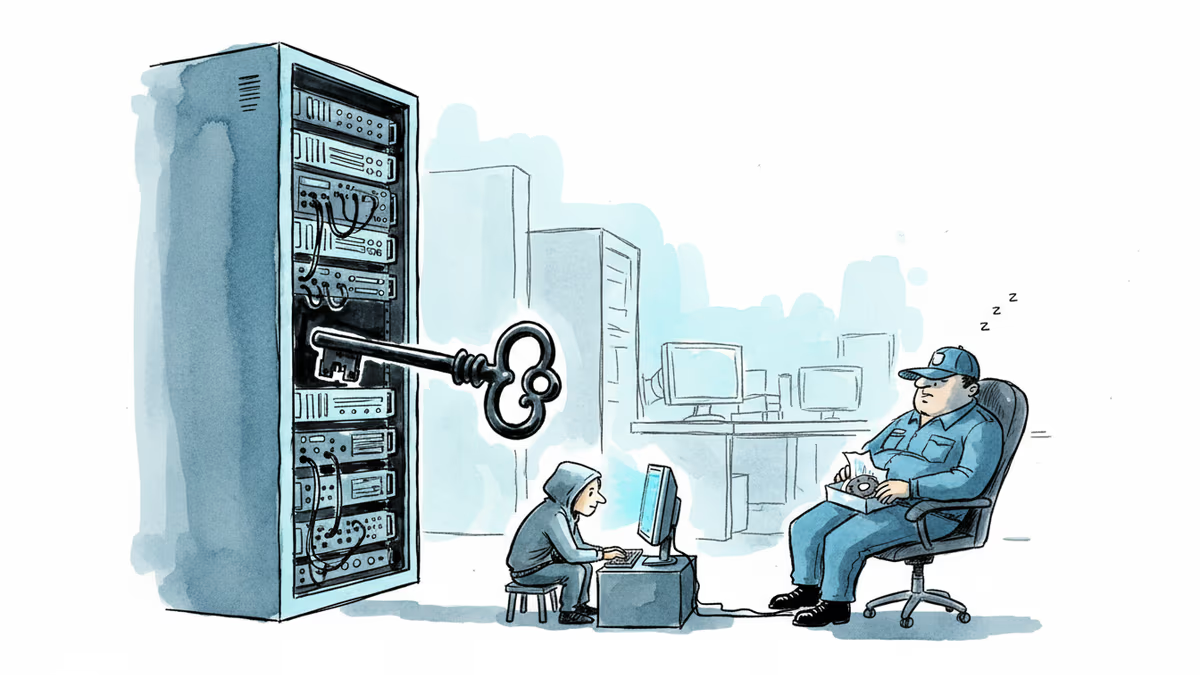
But Google controls its own silicon for Pixel devices. The broader Android ecosystem is a different story. Qualcomm modems power the majority of flagship Android phones worldwide, while Samsung's Exynos chips appear in hundreds of millions of devices. Neither company has publicly committed to a comparable Rust migration path for baseband firmware. Google's move puts quiet pressure on the entire supply chain — but pressure and action aren't the same thing.
For consumers, the frustrating reality is that modem firmware updates don't work like app updates. They flow through a slow pipeline: chipmaker to OEM to carrier to device. A vulnerability discovered today might not be patched on your specific handset for months — if ever, depending on your device's support lifecycle. The 3-5 year software support windows that Google and Samsung now advertise cover the main OS. Modem firmware is a separate promise, rarely made explicitly.
Security researchers point to a broader concern: as 5G expands the attack surface with more complex protocols and more devices connected to cellular networks — including cars, medical devices, and industrial equipment — modem security stops being just a smartphone problem.
Authors
Related Articles

A critical vulnerability in Starlette—downloaded 325 million times per week—puts millions of AI agent servers at risk, exposing stored credentials for email, databases, and third-party services.
GitHub confirmed hackers stole data from 3,800 internal repositories via a poisoned VS Code extension. Here's why developer tools are now the most dangerous attack surface in tech.

A Utah woman was sentenced to life in prison partly because of her Google searches and deleted texts. The Kouri Richins case reveals how digital footprints have become the courtroom's most reliable witness.
Dirty Frag gives low-privilege users root access on virtually every Linux distro. The exploit code leaked three days ago. Microsoft says attackers are already experimenting with it.
Thoughts
Share your thoughts on this article
Sign in to join the conversation