Hackers Breach FBI's Wiretap System - What Are They Really After?
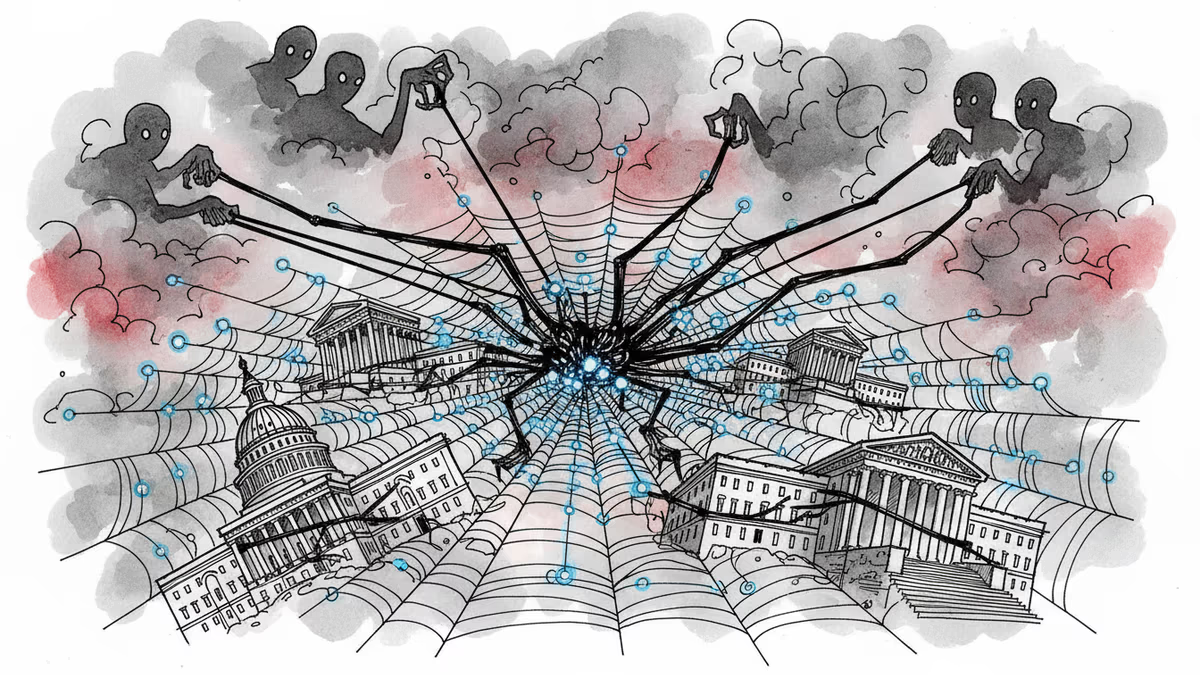
FBI's wiretapping and surveillance systems have been hacked. We analyze the strategic pattern behind China's cascade of cyberattacks and what it means for national security.
The Heart of US Intelligence Just Got Pierced
The FBI confirmed what cybersecurity experts feared most: hackers have breached the bureau's wiretapping and surveillance systems. This isn't just another data breach—it's an attack on the very infrastructure used to manage court-authorized wiretaps and foreign intelligence surveillance warrants.
"The FBI identified and addressed suspicious activities on FBI networks," a spokesperson said Thursday, offering no details about scope or attribution. But the timing tells a story. This breach comes as 200+ US companies have fallen victim to coordinated attacks, suggesting a systematic campaign rather than opportunistic hacking.
A Pattern Emerges from the Chaos
The past 12 months reveal a troubling escalation. Chinese hackers infiltrated the Treasury Department and the National Nuclear Security Administration—the agency overseeing America's nuclear stockpile. Russian operatives stole sealed court records. Meanwhile, the Chinese government group Salt Typhoon has systematically compromised telecommunications giants including AT&T, Verizon, Lumen, and Charter Communications.
Each target seems carefully chosen. Nuclear security, financial oversight, judicial records, telecommunications infrastructure—and now the FBI's surveillance apparatus. This isn't random; it's strategic mapping of America's most sensitive operations.
The Surveillance Paradox
Here's the uncomfortable irony: hackers have penetrated the very system designed to catch them. The FBI's wiretapping infrastructure, built to monitor threats to national security, has become a window for foreign adversaries to understand how America watches the world.
For telecom companies, this creates a nightmare scenario. If hackers can access FBI surveillance systems, they potentially know which communications are being monitored—and which aren't. It's like giving criminals the police patrol schedule.
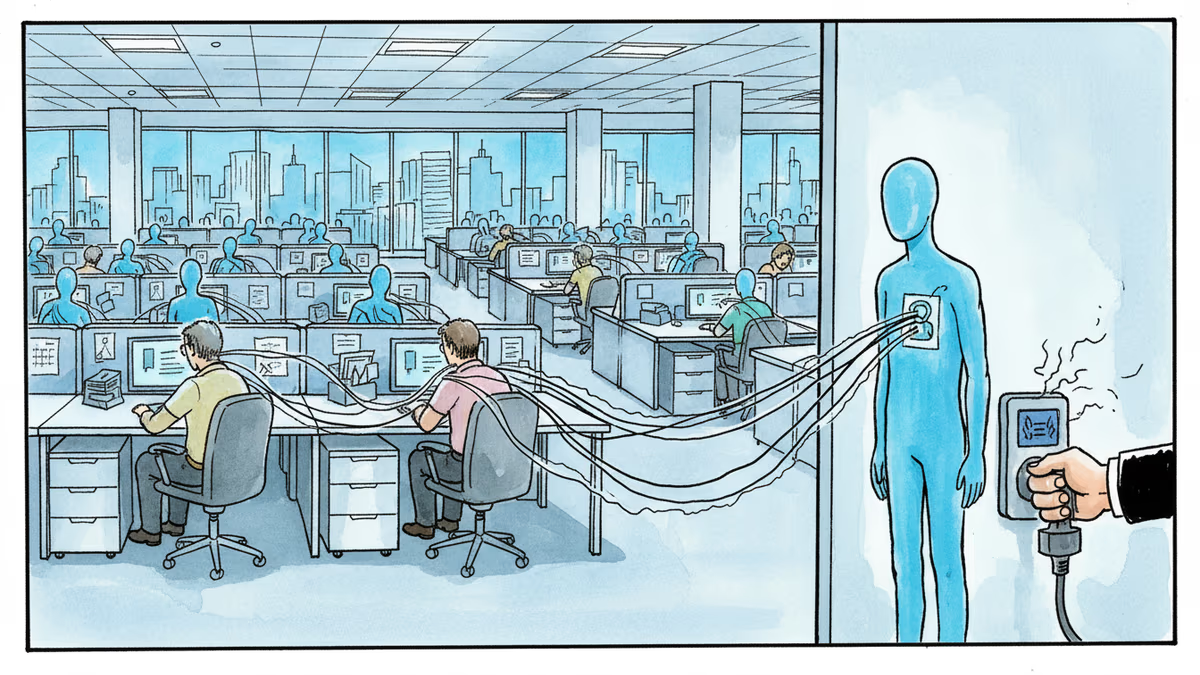
Beyond Government: Private Sector Vulnerability
While headlines focus on government breaches, the private sector faces equal risk. The 200 companies compromised by Salt Typhoon represent critical infrastructure: energy grids, financial networks, supply chains. Each breach provides attackers with deeper insight into American operations.
Cybersecurity professionals are asking hard questions: Are current defenses fundamentally inadequate? Should critical infrastructure be isolated from internet connectivity entirely? How do you protect systems when the threat comes from nation-states with unlimited resources?
This content is AI-generated based on source articles. While we strive for accuracy, errors may occur. We recommend verifying with the original source.
Related Articles
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
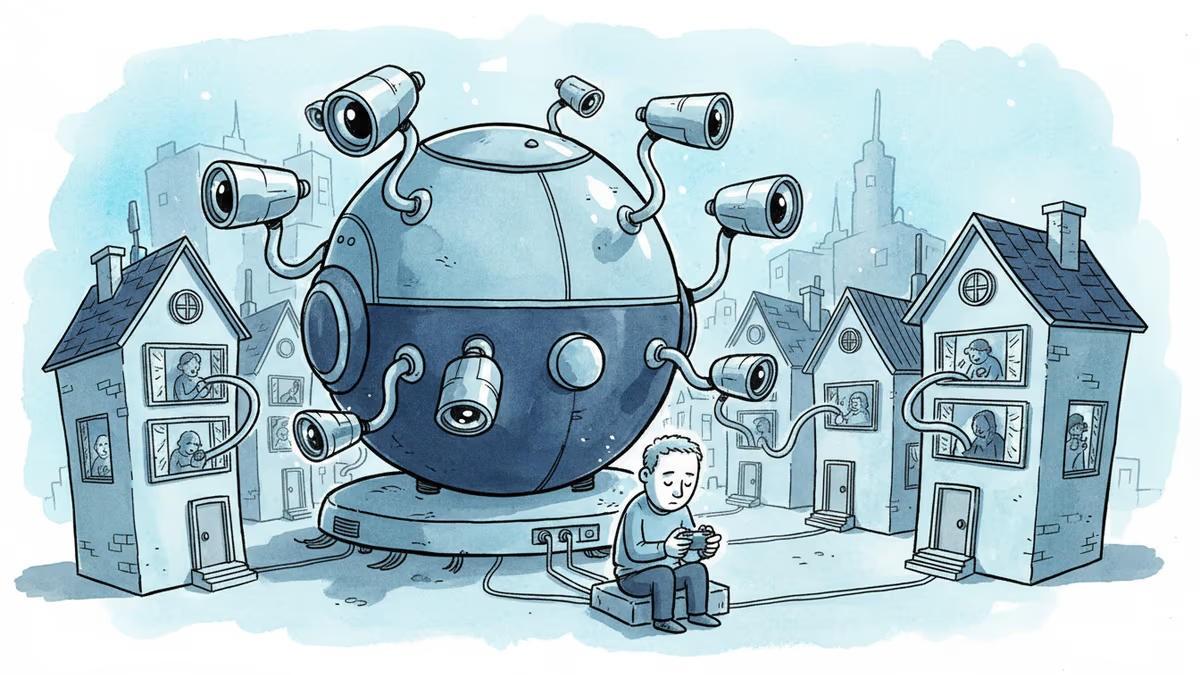
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
CISA orders emergency patches for iOS vulnerabilities exploited by sophisticated Coruna toolkit, revealing how cybercriminals weaponize already-patched flaws
Thoughts
Share your thoughts on this article
Sign in to join the conversation