Coupang Data Leak: 3,000 Customers' Info Recovered, But 33 Million Accounts Were Accessed
Coupang reports a data breach by a former employee who accessed 33 million accounts but only saved data from 3,000, which has been recovered. No data was shared externally.
While Coupang insists no data was shared externally, the government is treating it with urgency. The e-commerce giant announced on Thursday that it has recovered all leaked personal information involving approximately 3,000 customers, attributing the breach to a former employee. The company stated that no data was transferred to any outside party.
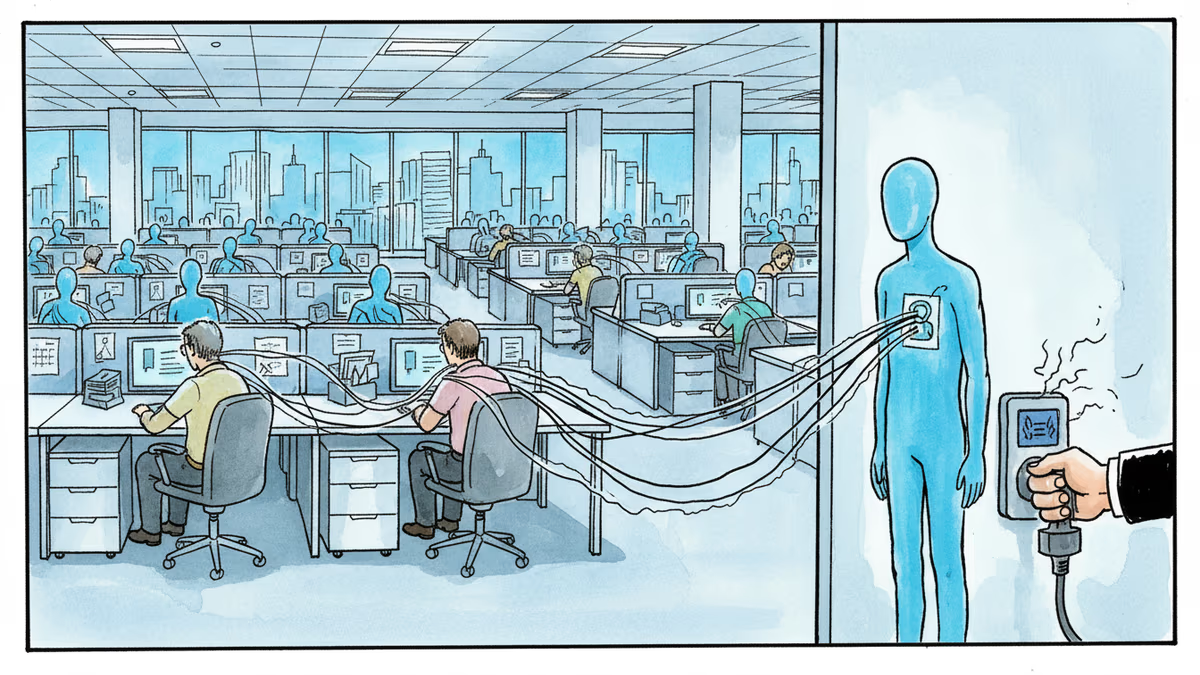
An Inside Job: How It Happened
According to a press release from Coupang, the company identified the ex-employee using forensic evidence. The individual reportedly confessed, detailing how they used stolen security keys to access basic customer information from a pool of approximately 33 million accounts. However, the company claims data from only about 3,000 accounts was actually saved and later deleted by the suspect.
The accessed information included customers' names, email addresses, phone numbers, and home addresses. Coupang stressed that no sensitive information, such as payment details, login credentials, or customs clearance numbers, was breached. The company added that it has secured all devices used in the incident, including a hard drive, and an internal investigation found no evidence of data being shared with third parties.
Government Response and Market Jitters
Coupang's announcement came on the heels of news reports that the South Korean presidential office was set to hold an emergency meeting on the case. This suggests the government is taking the potential fallout from the data breach very seriously, despite the company's assurances that the situation is contained.
Authors
Related Articles
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
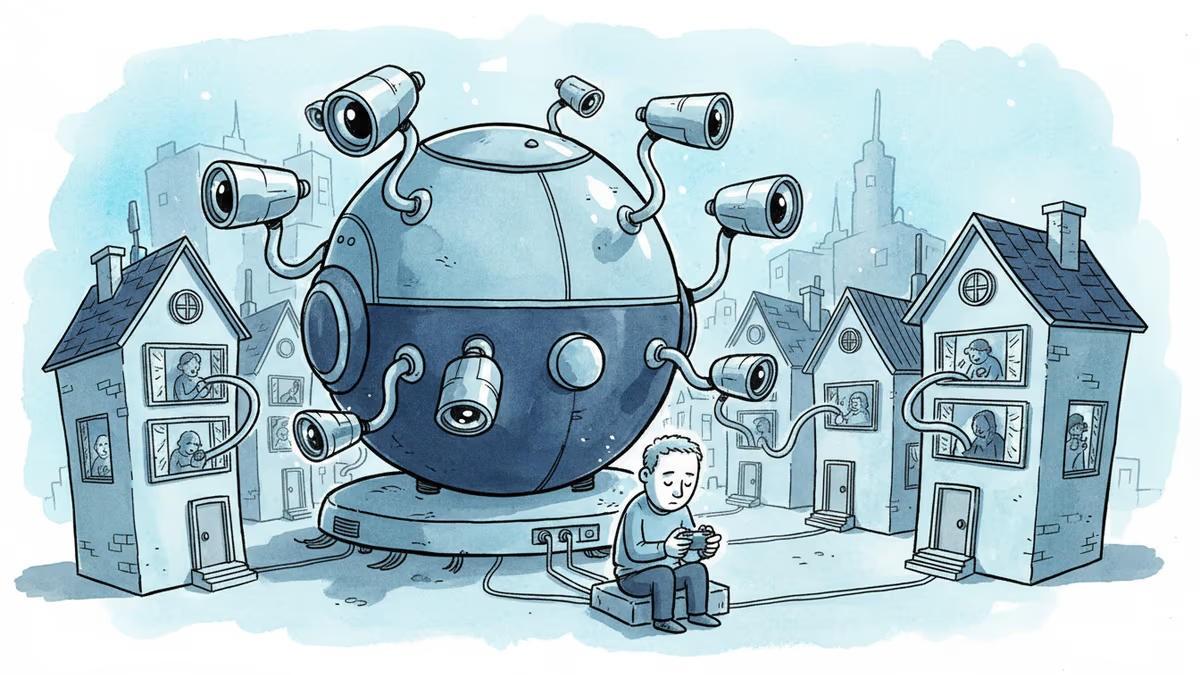
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
CISA orders emergency patches for iOS vulnerabilities exploited by sophisticated Coruna toolkit, revealing how cybercriminals weaponize already-patched flaws
Thoughts
Share your thoughts on this article
Sign in to join the conversation