
Your Computer Is Broadcasting Your Secrets
US lawmakers demand investigation into side-channel attacks as decades-old surveillance technique threatens modern devices. Why computers and phones still leak data through physics.
The $300 Pita Bread That Can Steal Your Passwords
Right now, as you read this, your computer is quietly betraying you. Every keystroke, hard drive movement, and electrical current flowing through semiconductor wires creates radio waves, sound, and vibrations that radiate in all directions. With the right equipment and enough espionage skill, someone can intercept these signals and reconstruct your private data.
This isn't science fiction. It's physics—and it's been a known problem for nearly 80 years.
Why Congress Is Finally Paying Attention
On Wednesday, Senator Ron Wyden and Representative Shontel Brown sent a bombshell letter to the Government Accountability Office, demanding an investigation into how vulnerable everyday Americans are to these "side-channel attacks." Their concern: what the NSA has long called TEMPEST—the surveillance technique that turns your device's accidental emanations into an open book.
The timing isn't coincidental. While Wyden declined to reveal whether classified intelligence sparked his letter, he's historically used public warnings to address threats he can't directly discuss. His message is clear: "Surveillance technologies eventually trickle down from the most sophisticated intelligence agencies... to private investigators and criminals."
The vulnerability has been hiding in plain sight since the 1940s, when Bell Labs discovered their military encryption machines were broadcasting secrets through electromagnetic radiation. A declassified 1972 NSA report warned these signals could travel over half a mile—or much farther through power lines and water pipes.
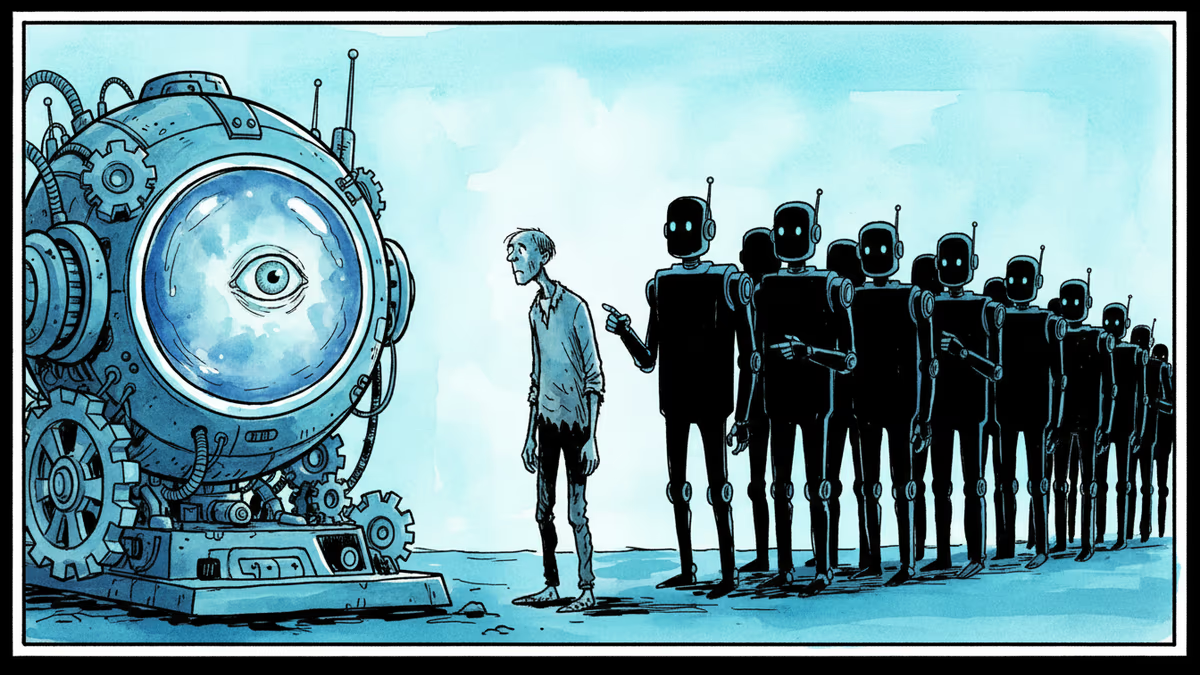
The Democratization of Espionage
What's changed isn't the physics—it's the accessibility. In 2015, Tel Aviv University researchers built a radio spying device for under $300 that could steal computer data from several feet away. The device? Small enough to hide inside a pita bread.
The same team proved they could extract cryptographic keys just by listening to a computer's high-pitched operational sounds using an ordinary smartphone. No hacking required—just physics and signal processing.
The Government's Double Standard
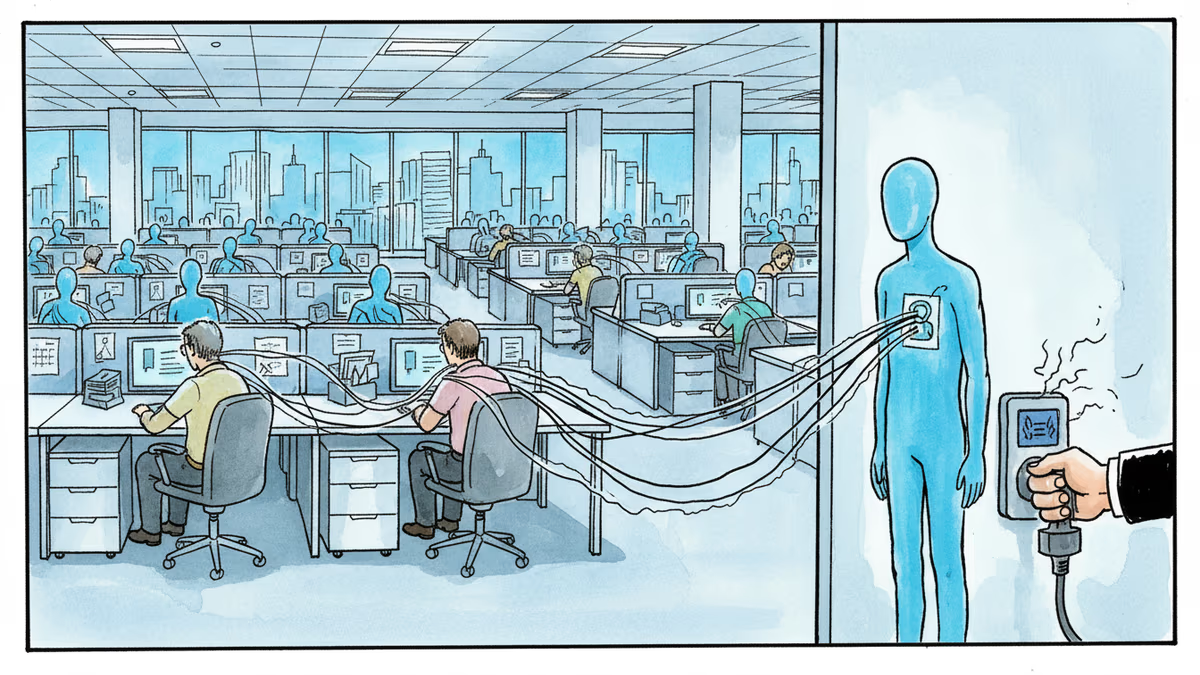
Here's the kicker: the US government has known about this threat for decades and protects itself accordingly. Classified facilities use SCIFs (Sensitive Compartmented Information Facilities)—radio-shielded spaces that block electromagnetic emanations. Yet as Wyden and Brown point out, the government has "neither warned the public about this threat, nor imposed requirements on manufacturers... to build technical countermeasures into their products."
Meanwhile, Apple, Google, and other tech giants continue shipping devices with no mandated protections against side-channel attacks. The government has essentially left consumers "vulnerable and in the dark."
Corporate America: Sitting Ducks or Smart Targets?
Not everyone needs to worry equally. "The average American does not need to worry about Russian or Chinese spies parked outside their home," Wyden notes. But US businesses developing "strategically important technologies" are obvious targets for industrial espionage.
Security researcher Cooper Quintin from the Electronic Frontier Foundation puts it bluntly: "The people that need to worry about this are people in national security or who work in fields where international state-backed industrial espionage is a concern."
Yet the threat landscape is evolving. Hacker Samy Kamkar warns that while major manufacturers like Apple and Google have reduced electromagnetic leakage through battery optimization, the explosion of smart devices—from speakers to industrial control systems—may be creating new vulnerabilities.
The AI Wild Card
There's another factor that could tip the scales: artificial intelligence. AI's improving ability to find meaningful signals in noisy data might make side-channel attacks significantly easier to execute. What once required sophisticated intelligence agencies could become accessible to smaller actors with the right algorithms.
The Congressional Research Service report commissioned by Wyden and Brown suggests several regulatory paths forward. The FCC could impose security requirements on radio equipment. The FTC could target companies making security claims while ignoring TEMPEST-style vulnerabilities as engaging in "unfair or deceptive practices."
The Cloud Paradox
Interestingly, some modern trends work in our favor. The shift to cloud computing means more processing happens in data centers, where would-be spies would struggle to get close enough to intercept emanations. Battery life optimization has also led to more efficient, less "leaky" components.
But as Kamkar notes, this protection doesn't extend to all devices. Industrial systems, smart home gadgets, and IoT devices may still be broadcasting secrets to anyone with the skills to listen.
Authors
Related Articles
Tinder now rewards users who scan their irises at a World orb with free in-app boosts. As AI agents flood dating apps, 'being human' is becoming a verified status — and a business model.

Wisconsin Governor Tony Evers vetoed an age verification bill for adult sites, citing privacy concerns. With 25+ states going the other way, the debate cuts to the heart of online freedom vs. child protection.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
Thoughts
Share your thoughts on this article
Sign in to join the conversation