2025 Supply-Chain Attack Trends: Lessons from the Solana Smart Contract Breach
Analysis of 2025 supply-chain attack trends, featuring the Solana blockchain breach and the systemic vulnerabilities of Fortune 500 companies in the current threat landscape.
One breach, millions of victims. Supply-chain attacks have evolved from a niche threat into a recurring nightmare for global organizations in 2025. According to Ars Technica, the sheer scale of these attacks has reached a tipping point, dangerously close to inflicting a global catastrophe across various sectors.
Mapping the 2025 Supply-Chain Attack Landscape
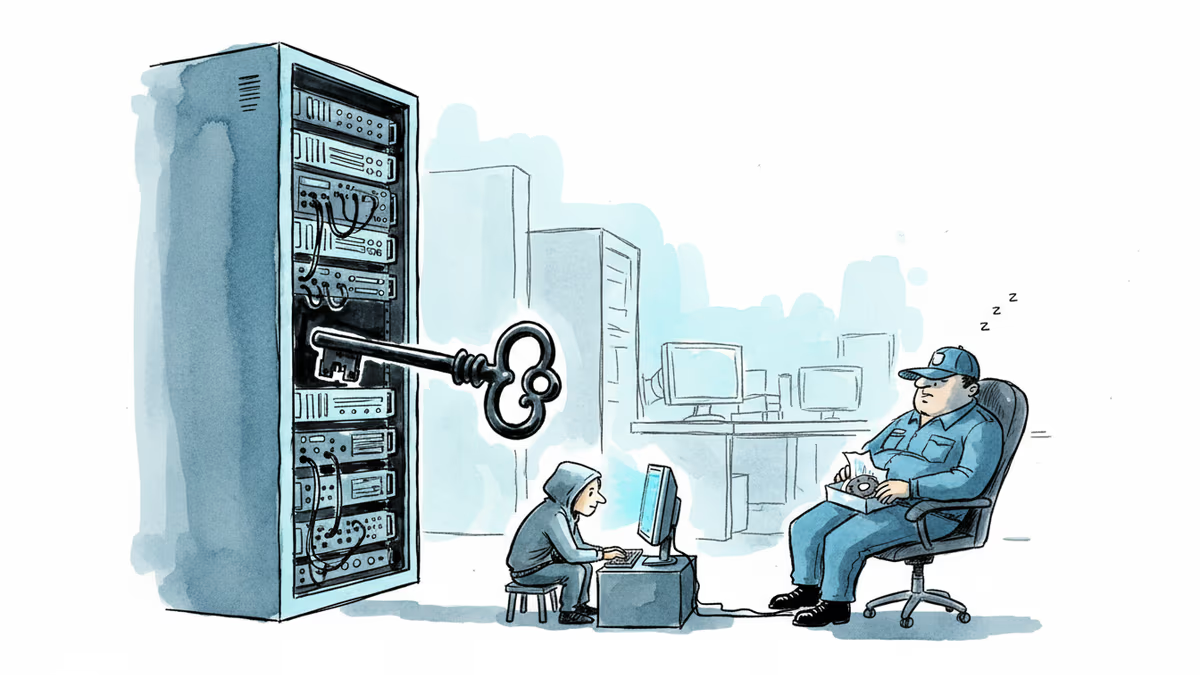
For threat actors, this method is the gift that keeps on giving. By compromising a single target—such as a cloud service or a maintainer of widely used open source software—attackers can infect an entire ecosystem of downstream users. This strategy was prominently seen throughout 2024 and has continued unabated into 2025.
A defining moment occurred in December 2024, when hackers successfully targeted the Solana blockchain. By poisoning smart-contract parties, they siphoned as much as $155,000 from thousands of participants. This incident highlighted the vulnerability of decentralized infrastructure when the underlying supply chain is compromised.
Authors
Related Articles

A critical vulnerability in Starlette—downloaded 325 million times per week—puts millions of AI agent servers at risk, exposing stored credentials for email, databases, and third-party services.
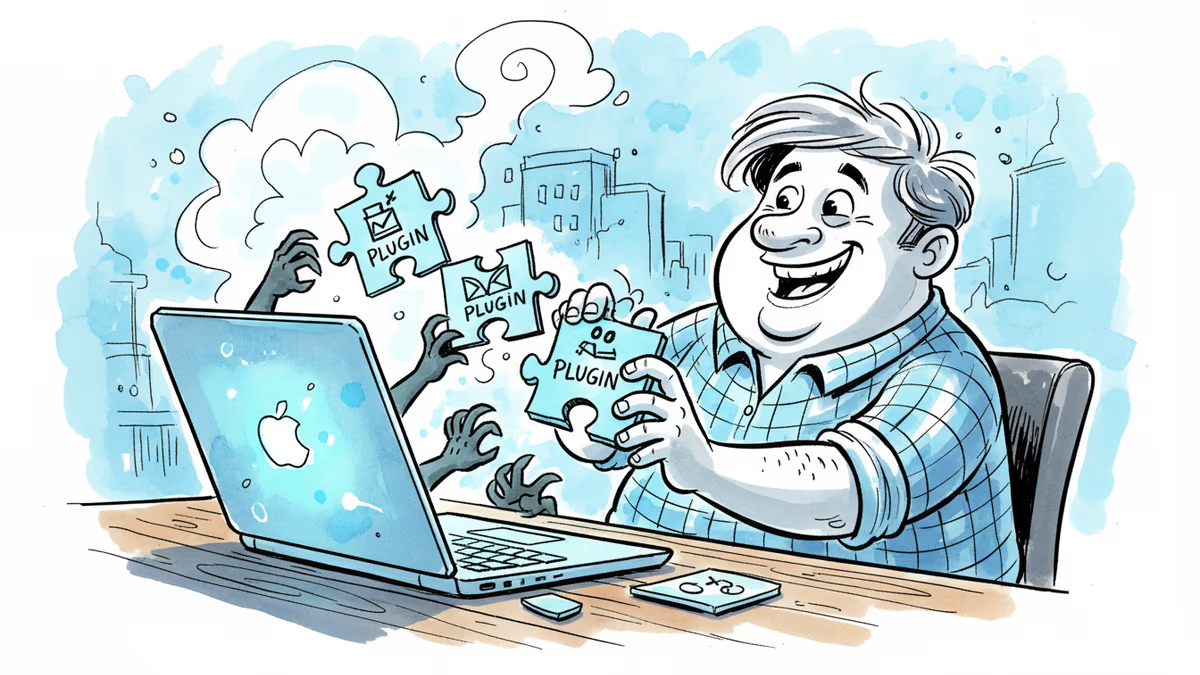
GitHub confirmed hackers stole data from 3,800 internal repositories via a poisoned VS Code extension. Here's why developer tools are now the most dangerous attack surface in tech.

A Utah woman was sentenced to life in prison partly because of her Google searches and deleted texts. The Kouri Richins case reveals how digital footprints have become the courtroom's most reliable witness.
Dirty Frag gives low-privilege users root access on virtually every Linux distro. The exploit code leaked three days ago. Microsoft says attackers are already experimenting with it.
Thoughts
Share your thoughts on this article
Sign in to join the conversation