
850 Records Exposed: The Iran WhatsApp Phishing Campaign 2026 Deep Dive
A sophisticated Iran WhatsApp phishing campaign has exposed 850 records of activists and officials. Learn how hackers used QR codes and DuckDNS to bypass security.
A single tap was all it took to turn a smartphone into a pocket-sized spy. A sophisticated hacking operation targeting Iranian activists and Middle Eastern officials has been unmasked. According to TechCrunch, an investigation into a phishing link shared by activist Nariman Gharib revealed that over 850 records of victim data were left exposed on an unprotected server.
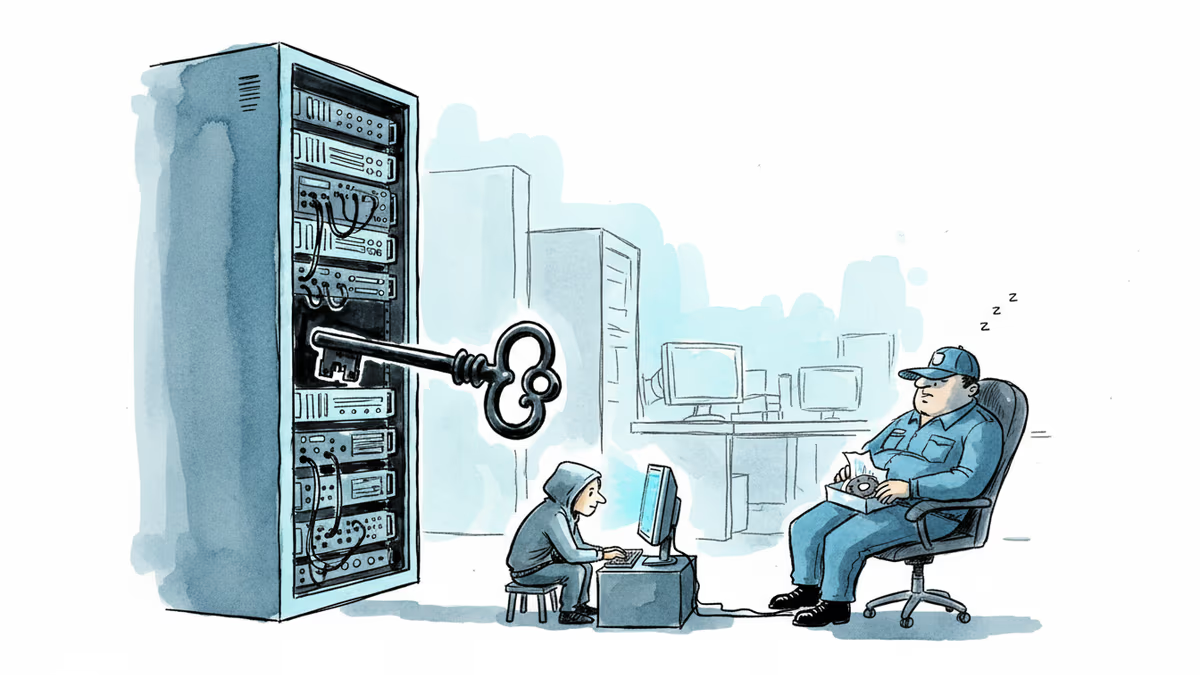
Tactics of the Iran WhatsApp Phishing Campaign 2026
The attackers utilized WhatsApp messages to lure targets into fake virtual meeting rooms. By leveraging dynamic DNS providers like DuckDNS, they masked their malicious infrastructure. The most alarming tactic involved a QR code lure that, once scanned, granted hackers full access to the victim's messaging history via device-linking features.
- Credential Theft: Fake Gmail login pages captured 2FA codes in real-time.
- Surveillance: The site requested browser permissions to track GPS coordinates.
- AV Capture: The code was designed to snap photos every 3-5 seconds.
High-Value Targets and IRGC Links
The list of confirmed victims includes an Israeli drone maker CEO, a Lebanese cabinet minister, and various academics. Security researcher Gary Miller noted that the attack bears the hallmarks of an IRGC-linked campaign, suggesting a state-sponsored espionage motive rather than simple cybercrime.
Authors
Related Articles

A critical vulnerability in Starlette—downloaded 325 million times per week—puts millions of AI agent servers at risk, exposing stored credentials for email, databases, and third-party services.
GitHub confirmed hackers stole data from 3,800 internal repositories via a poisoned VS Code extension. Here's why developer tools are now the most dangerous attack surface in tech.

A Utah woman was sentenced to life in prison partly because of her Google searches and deleted texts. The Kouri Richins case reveals how digital footprints have become the courtroom's most reliable witness.
Dirty Frag gives low-privilege users root access on virtually every Linux distro. The exploit code leaked three days ago. Microsoft says attackers are already experimenting with it.
Thoughts
Share your thoughts on this article
Sign in to join the conversation