
When Hackers Became as Deadly as Fighter Jets
Cyber operations played a pivotal role in the U.S.-Israeli strikes against Iran, disrupting communications and hijacking broadcasts. A new era of warfare where code is as powerful as bombs.
168 children died when bombs hit an Iranian girls' school. But the deadliest weapon in the U.S.-Israeli assault on Iran might not have been the missiles—it was the hackers who made sure Iran couldn't see them coming.
The Invisible First Strike
Gen. Dan Caine didn't mince words: "Coordinated space and cyber operations effectively disrupted communications and sensor networks" across Iran before the kinetic strikes began. The goal? Leave the enemy "without the ability to see, coordinate or respond effectively."
This wasn't just digital support—it was warfare's new reality. After bombing Iran's state broadcaster IRIB, Israeli hackers hijacked the airwaves to broadcast speeches by Trump and Netanyahu, urging Iranians to "join the fight against the regime." The message was clear: we control not just your skies, but your information space.
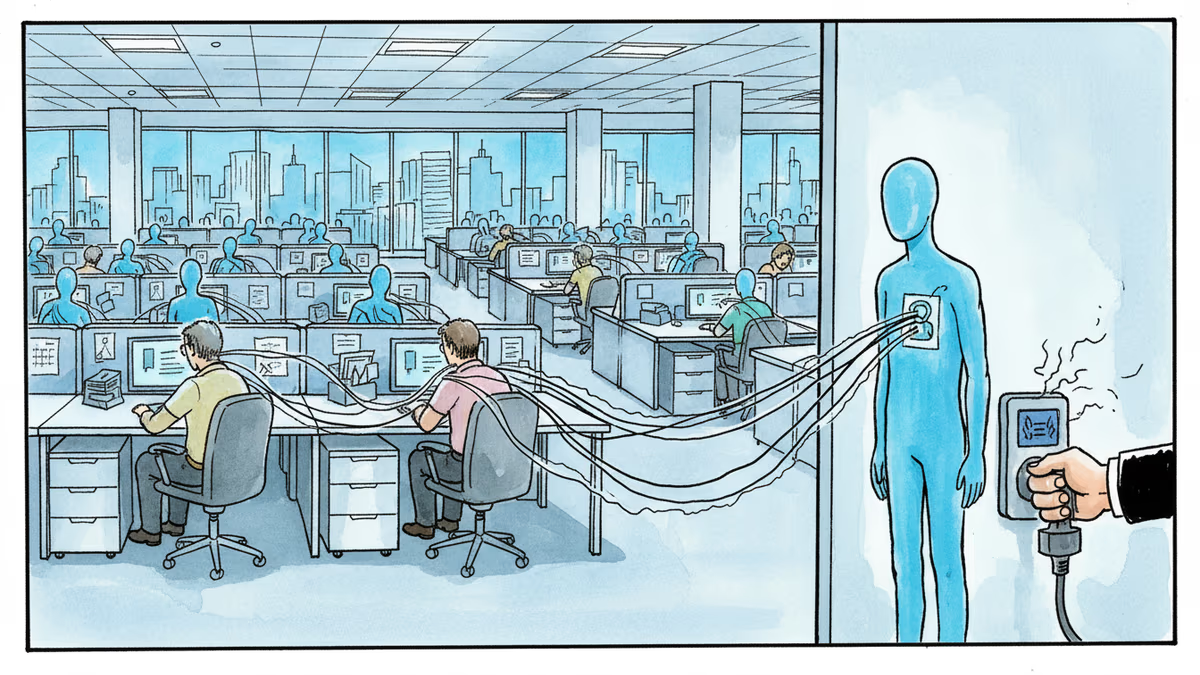
Tehran's Eyes Belonged to the Enemy
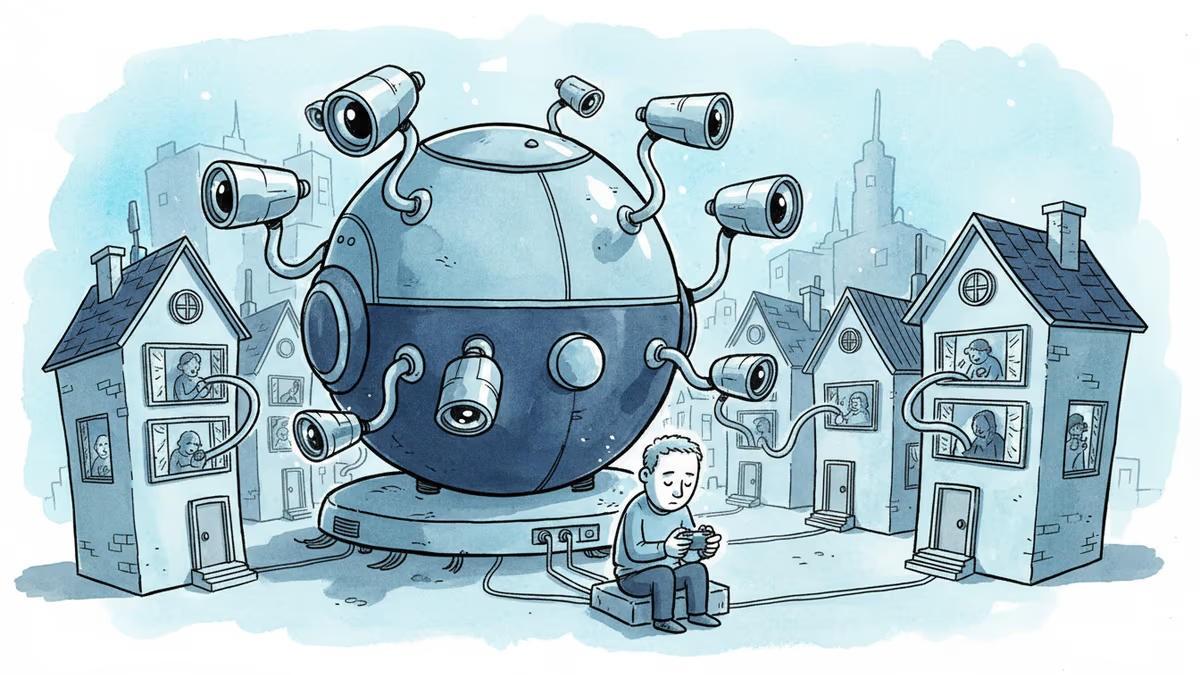
The assassination of Supreme Leader Ali Khamenei relied on intelligence gathered through years of digital infiltration. Israeli spies had hacked Tehran's traffic camera network and "deeply penetrated mobile phone networks," according to the Financial Times. Every street corner, every phone call—all feeding intelligence to the attackers.
The psychological operations were equally sophisticated. Hackers breached BadeSaba Calendar, a popular prayer app, sending messages to users: "For the freedom of our Iranian brothers and sisters... lay down your weapons or join the forces of liberation. Only in this way can you save your lives."
The Asymmetry Problem
Iran's cyber response has been "largely ineffective," Bloomberg reports. This digital divide reveals a troubling reality for smaller nations: cyber capabilities require sustained investment, technical expertise, and institutional knowledge that can't be built overnight.
For U.S. policymakers, this raises uncomfortable questions about escalation. When cyber operations can blind an entire nation's defenses, the line between preparation and provocation becomes dangerously thin.
The Exaggeration Factor
Not everything is as it appears in the fog of cyber war. Earlier this year, U.S. officials claimed hackers caused power outages in Caracas during operations against Venezuela's Nicolás Maduro. Analysis later suggested fighter jets destroying electrical substations were the more likely culprit.
This pattern of inflating cyber capabilities serves a strategic purpose: psychological warfare works best when the enemy believes you're omnipresent in their networks. But it also makes assessing the true role of cyber operations nearly impossible.
What This Means for Modern Conflict
The Iran operation represents a maturation of cyber warfare from espionage tool to combat enabler. Unlike previous conflicts where hacking was largely separate from kinetic operations, this war demonstrated seamless integration: cyber attacks clearing the path for airstrikes, intelligence gathering enabling precision targeting, and information operations supporting strategic objectives.
For cybersecurity professionals, the implications are stark. The infrastructure they protect—traffic cameras, mobile networks, broadcasting systems—isn't just civilian infrastructure anymore. It's potential military infrastructure.
Authors
Related Articles

UK Visa Portal, a private immigration service mistaken for an official government site, has been exposing passport scans and selfies of over 100,000 applicants. The breach remains unpatched.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
Thoughts
Share your thoughts on this article
Sign in to join the conversation