
27 Stalkerware Companies Hacked, Industry Still Thriving
Despite massive data breaches exposing hundreds of thousands of victims, the stalkerware industry continues to operate with impunity, raising questions about digital privacy and abuse.
Half a Million Payment Records Just Hit the Dark Web
A hacktivist just dumped the payment information of 500,000 customers from uMobix, a company that sells software to spy on family members. But here's the kicker: this isn't even close to being the first time.
Since 2017, at least 27 stalkerware companies have been hacked or accidentally leaked sensitive data online. That's not a typo. Twenty-seven companies in an industry built on violating privacy have themselves become victims of privacy violations.
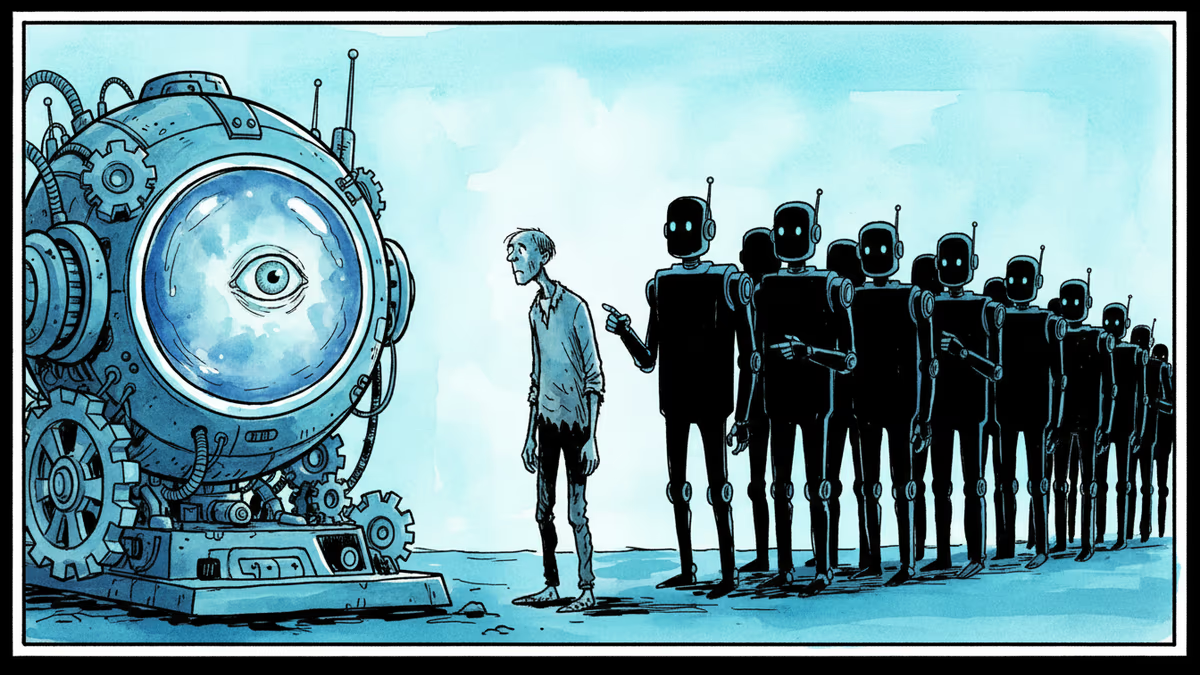
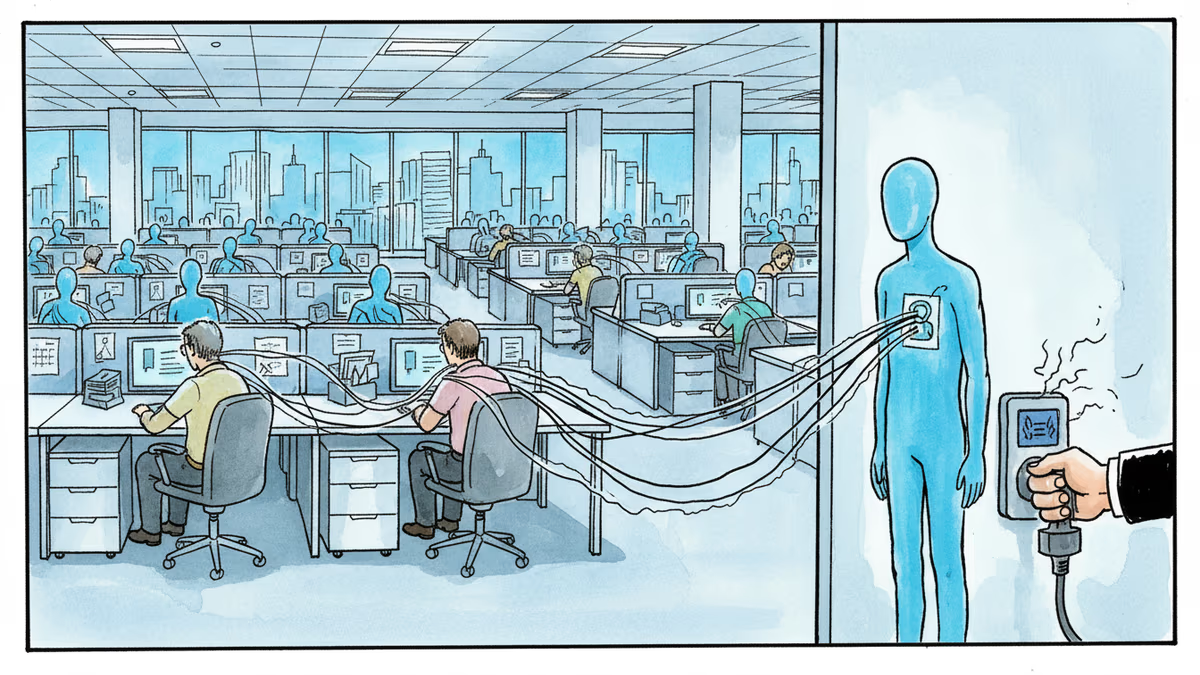
Stalkerware apps are marketed as "family protection" tools, but they're primarily used by jealous partners to secretly monitor their victims' phones. Location tracking, text messages, call logs, photos—everything becomes accessible to the person doing the spying.
The irony is stark: companies that profit from surveillance can't even protect their own data, let alone their customers' payment information or their victims' most intimate communications.
When Hacktivists Become Digital Vigilantes
This isn't random cybercrime. It's targeted digital activism.
The campaign began in 2017 when hackers systematically breached Retina-X and FlexiSpy. "I'm going to burn them to the ground," one hacker told Motherboard at the time. They weren't just stealing data—they were wiping servers entirely, trying to destroy these companies from the inside.
Some succeeded. Retina-X shut down after getting hacked twice. pcTattletale's founder announced he was closing shop after hackers defaced his website and leaked internal data. The company's founder later pled guilty to computer hacking charges.
But for every company that closes, others keep operating. FlexiSpy, despite being breached in 2017, is still active today. Of the 27 breached companies, only 8 have actually shut down.
The Double Victimization Problem
The real tragedy isn't what happens to these companies—it's what happens to the people caught in the crossfire.
First, they're illegally surveilled by partners or family members. Then, when these poorly secured companies get hacked, their most private data ends up on the internet. Most victims don't even know they're being monitored in the first place.
"The people who run these companies are perhaps not the most scrupulous or really concerned about the quality of their product," Eva Galperin from the Electronic Frontier Foundation told TechCrunch.
That might be an understatement. Some companies didn't even get "hacked"—they just left data sitting in the open. SpyFone left an Amazon server unprotected. FamilyOrbit secured 281 gigabytes of personal data with an easy-to-guess password. Xnore had a bug that let any customer access other customers' stolen data.
Regulation Exists, But Enforcement Lags
The Federal Trade Commission has banned SpyFone and its CEO from the surveillance industry entirely—a first-of-its-kind action. New York's attorney general has gone after companies that explicitly encourage illegal surveillance.
But regulatory whack-a-mole isn't working. Companies rebrand, relocate, or simply ignore the rules. The global nature of the industry makes enforcement even harder—FlexiSpy operates from Thailand, WebDetetive from Brazil, others from jurisdictions with minimal oversight.
Meanwhile, the human cost keeps mounting. Studies consistently link digital stalking to real-world violence and abuse. Every data breach potentially exposes victims to further harm.
The stalkerware industry's security failures aren't just technical problems—they're symptoms of a business model that treats human privacy as a commodity. Until we address that fundamental issue, the cycle of surveillance, breach, and harm will continue.
Authors
Related Articles

UK Visa Portal, a private immigration service mistaken for an official government site, has been exposing passport scans and selfies of over 100,000 applicants. The breach remains unpatched.
Tinder now rewards users who scan their irises at a World orb with free in-app boosts. As AI agents flood dating apps, 'being human' is becoming a verified status — and a business model.

Wisconsin Governor Tony Evers vetoed an age verification bill for adult sites, citing privacy concerns. With 25+ states going the other way, the debate cuts to the heart of online freedom vs. child protection.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.
Thoughts
Share your thoughts on this article
Sign in to join the conversation