
What a Hacked Journalist Learned 14 Years Later
A 2012 hack that wiped out a journalist's digital life reveals the eternal cat-and-mouse game between technology and crime. Are we safer now?
Everything Gone in an Instant
2012. An iPhone suddenly shut down. When restarted, it was factory-reset clean. Panicked, the owner opened his laptop—also mid-restart. Then the screen went gray. Remote wipe in progress. The iPad? Same fate. Google account? Compromised. Twitter? Hijacked and spewing vile comments.
The perpetrators? Two kids. They didn't use sophisticated hacking techniques. Instead, they weaponized publicly available information and a fake credit card number to social-engineer their way into an Amazon account, discovered real credit card digits, then pivoted to Apple. From there, linked Gmail and Twitter accounts fell like dominoes.
Living in the Gap
The truly unsettling revelation came later: this wasn't an isolated incident. Technology had become commonplace, but its risks weren't yet understood—creating exploitable gaps. The victim simply had the misfortune of storing everything in that gap.
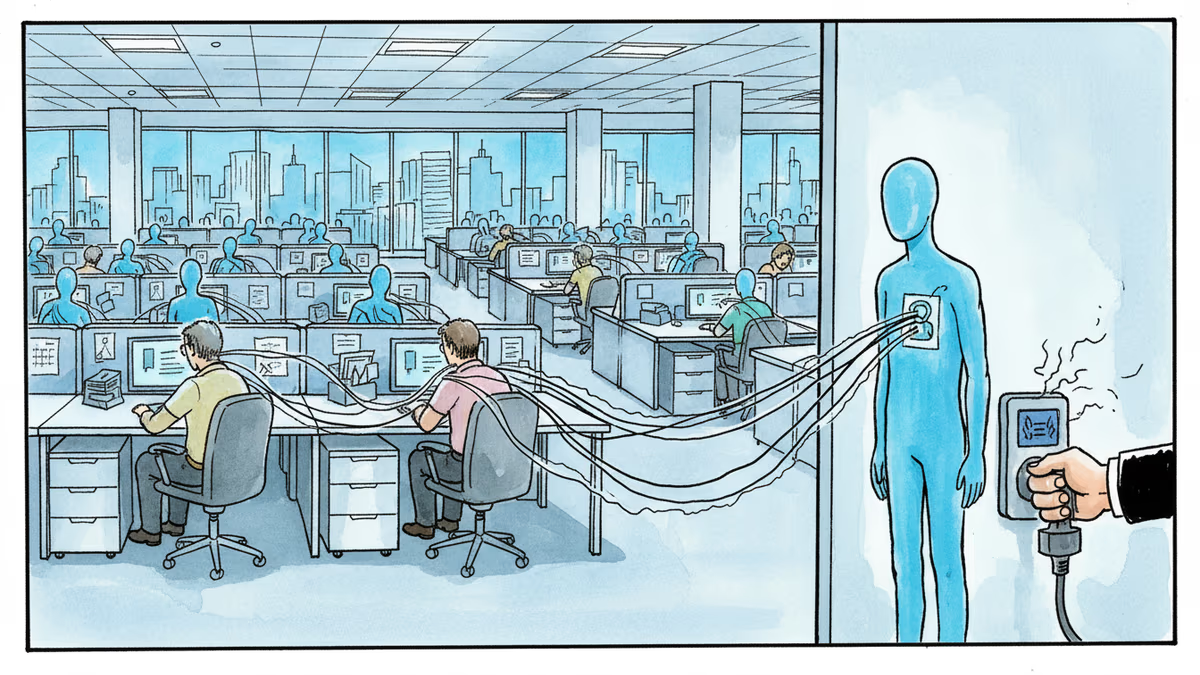
Today's gaps look different. Crypto wallets. Deepfake voices. Sometimes both. Crime's goals remain constant—value and power—but new technologies create new vulnerabilities, new tactics, new ways to evade capture.
Why Law Always Lags Behind
Law is inherently backward-looking. It relies on precedent, not innovation. It's intentionally slow and deliberate. This used to protect our democratic society—protecting us from each other through careful consideration.
But those same technologies enabling crime have also empowered law enforcement. Consider how Golden State Killer investigators used DNA samples and genealogy databases years after the murders, launching a new era of genetic investigations. Technology has made crime and prosecution a cat-and-mouse game.
Best Time for Crime, Best Time to Fight It
Cryptocurrency and off-the-shelf autonomous systems make this an excellent era for crime. Simultaneously, pervasive surveillance and digital infrastructure make it an excellent era for fighting crime—sometimes at the expense of what we once considered fundamental civil rights.
The journalist never pressed charges against those kids. The biggest outcome? Apple implemented two-factor authentication months later. Today, no one expects their personal data to be meaningfully secure. Yet somewhere online, a new generation is undoubtedly crafting novel crimes.
Authors
Related Articles

UK Visa Portal, a private immigration service mistaken for an official government site, has been exposing passport scans and selfies of over 100,000 applicants. The breach remains unpatched.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.

CBP admits buying location data from ad industry while Meta contractors watch users in bathrooms through smart glasses. The digital privacy boundary is crumbling.
Thoughts
Share your thoughts on this article
Sign in to join the conversation