
Google's Quantum Defense Dilemma: Security vs Speed in Chrome
Google unveils quantum-resistant HTTPS certificates for Chrome, but 40x larger certificates threaten internet speed. The trade-off between security and usability begins.
When Security Meets Reality: The 40x Problem
Google's Friday announcement seemed straightforward: Chrome will use quantum-resistant HTTPS certificates to defend against future quantum computer attacks. But the devil's in the details—and the details are massive.
Today's X.509 certificates clock in at a modest 64 bytes. Their quantum-resistant replacements? A hefty 2.5 kilobytes. That's roughly 40 times bigger, and every byte must travel across the internet each time you visit a website.
"The bigger you make the certificate, the slower the handshake and the more people you leave behind," warns Bas Westerbaan, principal research engineer at Cloudflare, which is partnering with Google on this transition.
The Human Factor in Cryptographic Evolution
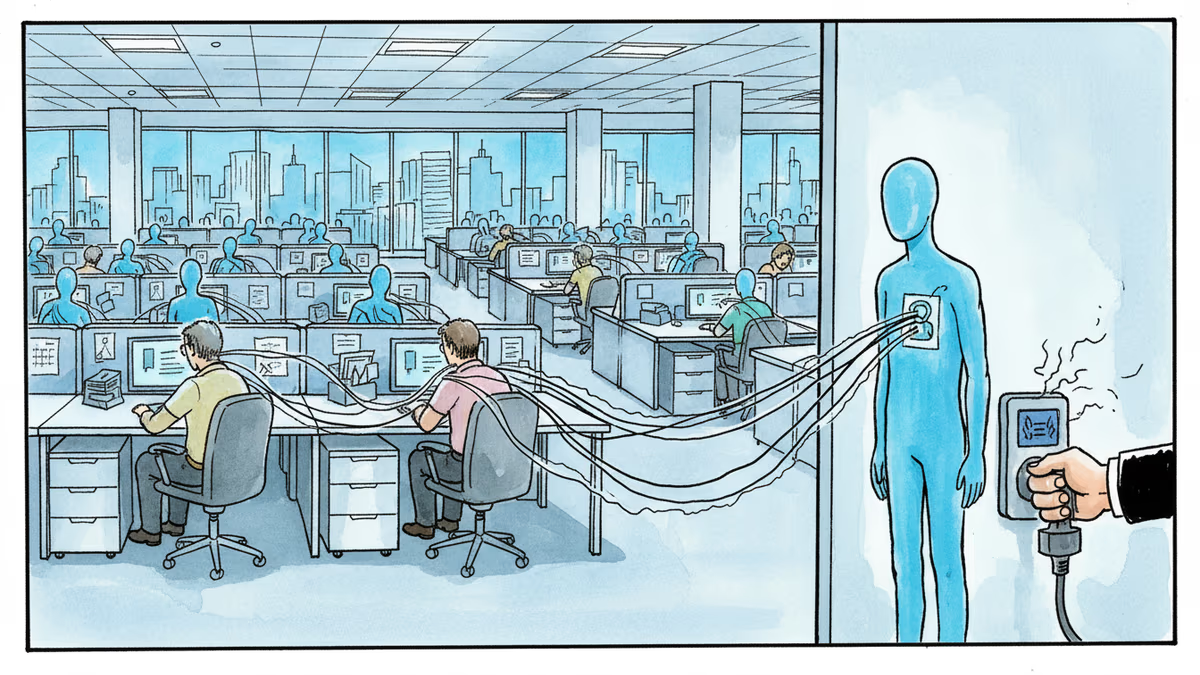
The technical challenge is only half the story. The real problem is human behavior. Westerbaan's concern isn't just theoretical—if browsing slows down noticeably, people will simply disable the new encryption. Security theater becomes meaningless if nobody uses it.
The infrastructure impact extends beyond individual browsers. "Middle boxes"—the network equipment sitting between your browser and destination websites—may struggle to process the dramatically larger certificates. These devices, often overlooked in security discussions, could become the weakest link in the quantum-resistant chain.
The Economics of Future-Proofing
For internet service providers and content delivery networks, the math is sobering. A 40x increase in certificate data translates directly to bandwidth costs, server processing power, and storage requirements. Smaller companies might find themselves priced out of robust quantum-resistant security.
This isn't just a technical upgrade—it's an economic reshuffling of who can afford premium security. The irony? The organizations most vulnerable to quantum attacks might be the least equipped to implement defenses.
Beyond the Browser: Mobile and IoT Implications
While Google focuses on Chrome, the ripple effects extend far beyond desktop browsing. Mobile devices, already balancing performance against battery life, face additional strain from processing larger certificates. IoT devices with minimal processing power might struggle entirely.
The timing creates another wrinkle. Quantum computers capable of breaking today's encryption don't exist yet—at least not publicly. We're essentially slowing down the internet today to defend against tomorrow's threats.
Authors
Related Articles

UK Visa Portal, a private immigration service mistaken for an official government site, has been exposing passport scans and selfies of over 100,000 applicants. The breach remains unpatched.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
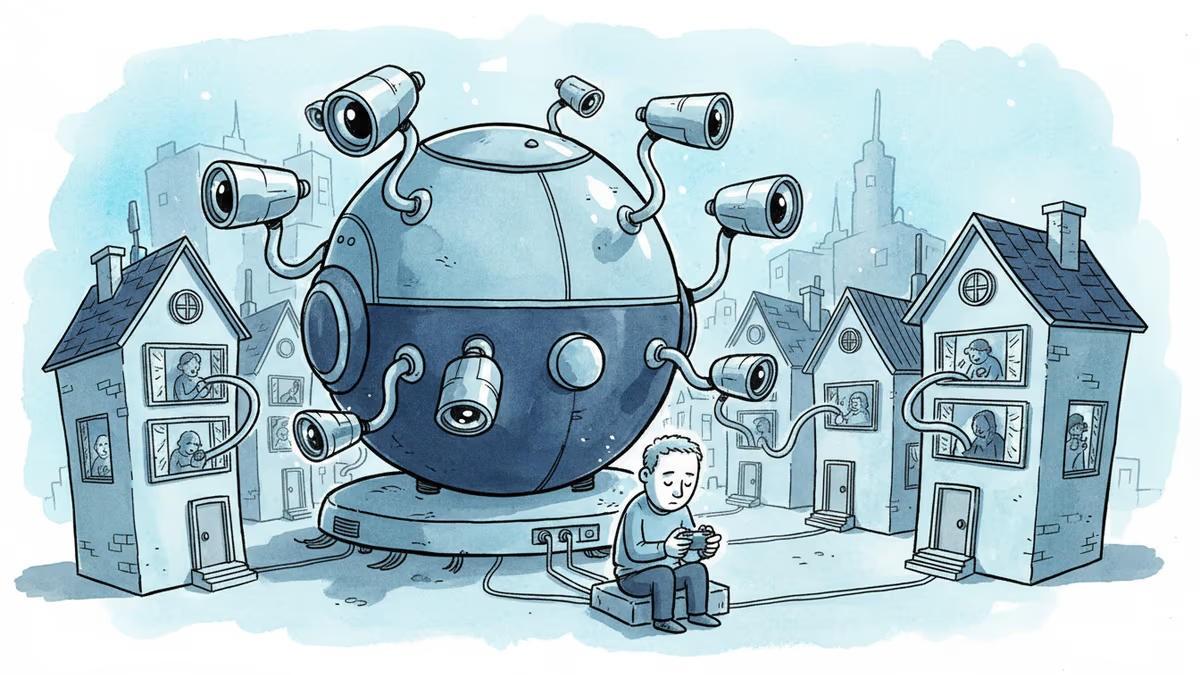
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
Thoughts
Share your thoughts on this article
Sign in to join the conversation