The Digital Black Market That Just Lost 142,000 'Customers
US and EU police shut down LeakBase, a massive hacker forum with 142,000 members trading stolen credentials. What does this takedown reveal about the evolution of cybercrime?
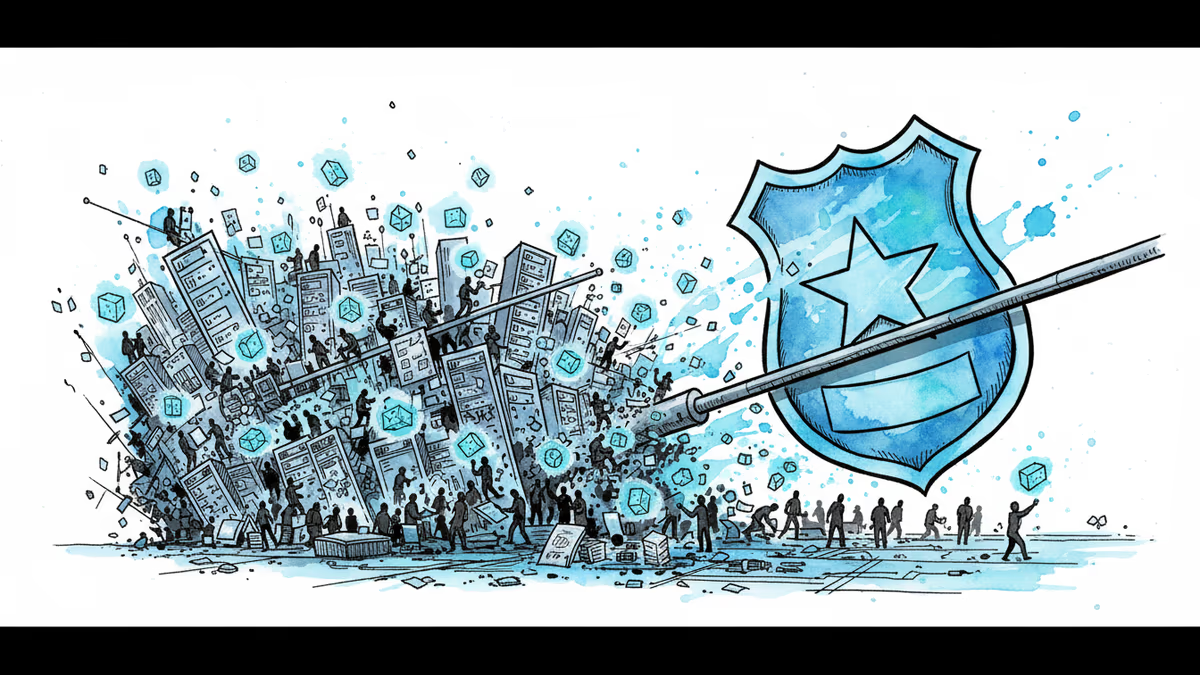
142,000 members. That's not just a user count—it's the size of a digital city where cybercriminals gathered for five years to trade in human misery. This week, US and European law enforcement dismantled LeakBase, what prosecutors called "one of the world's largest online forums for cybercriminals." The takedown reveals how cybercrime has evolved from lone wolves to organized digital marketplaces.
The Amazon of Stolen Data
LeakBase wasn't just another hacker forum. Operating since 2021, it functioned as a sophisticated criminal infrastructure where members could:
- Access hundreds of millions of stolen account credentials
- Purchase credit card numbers and banking information
- Download hacking tools and malware
- Exchange 215,000+ messages coordinating attacks
This wasn't random chaos—it was organized crime with customer service, product reviews, and reputation systems. Think eBay, but for your personal data.
A Global Coordinated Strike
The takedown wasn't a simple server seizure. According to FBI cyber official Brett Leatherman, the operation involved:
- 100 enforcement actions worldwide
- 13 arrests across multiple countries
- 33 suspects under investigation
- Targeted measures against the top 37 active users
The FBI's decision to redirect LeakBase's domain to display a seizure notice sent a clear message: "We're watching, and we have everything." The psychological impact on the cybercriminal community might be as valuable as the operational disruption.
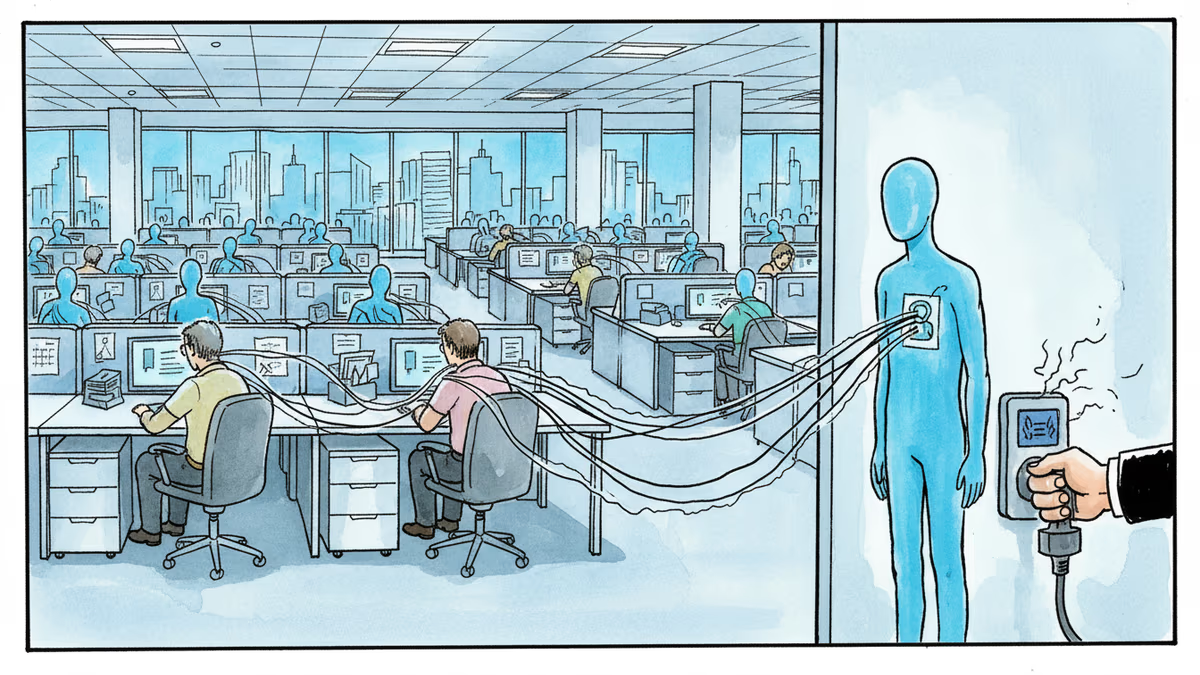
The Professionalization of Cybercrime
What makes LeakBase significant isn't just its size—it's what it represents. Cybercrime has industrialized. Where hackers once worked in isolation, platforms like LeakBase created economies of scale, specialization, and reduced barriers to entry.
A novice criminal could buy stolen credentials for pennies, while sophisticated operators sold zero-day exploits for thousands. The rise of cryptocurrency made these transactions seamless and pseudo-anonymous, accelerating the market's growth.
The Hydra Problem
Cybersecurity experts are cautiously optimistic but realistic about the limitations. "When you cut off one head, two more appear," explains the challenge facing law enforcement. Previous takedowns of major criminal marketplaces like Silk Road and AlphaBay were followed by new platforms that learned from their predecessors' mistakes.
The deeper issue is that the stolen data from LeakBase doesn't disappear with the forum. Those hundreds of millions of compromised credentials are still out there, likely being redistributed through smaller, more secretive channels.
What This Means for Regular Users
For the average internet user, LeakBase's closure offers both relief and a sobering reminder. Your email, password, or credit card information may have been traded on this platform. The forum's database preservation by authorities might help identify victims, but it also highlights how exposed we all are.
The incident underscores why security experts constantly preach password hygiene, two-factor authentication, and regular monitoring of financial accounts. In a world where criminal marketplaces can operate for years with six-figure membership, individual vigilance becomes crucial.
Authors
Related Articles

UK Visa Portal, a private immigration service mistaken for an official government site, has been exposing passport scans and selfies of over 100,000 applicants. The breach remains unpatched.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
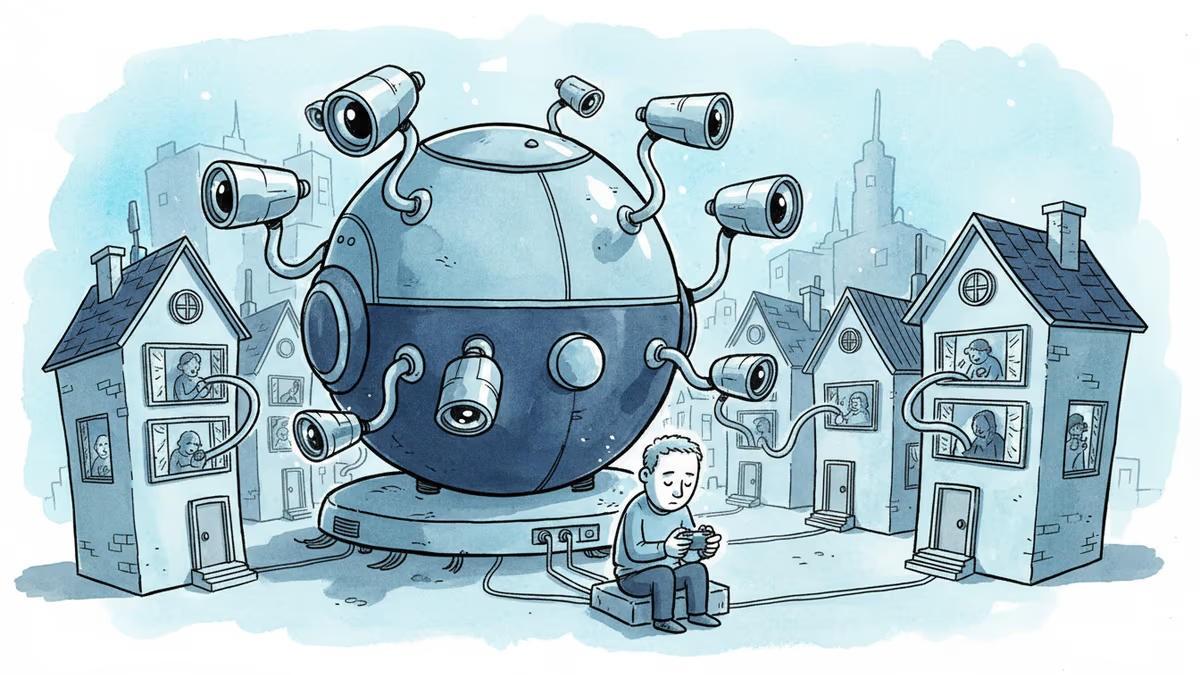
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
Thoughts
Share your thoughts on this article
Sign in to join the conversation