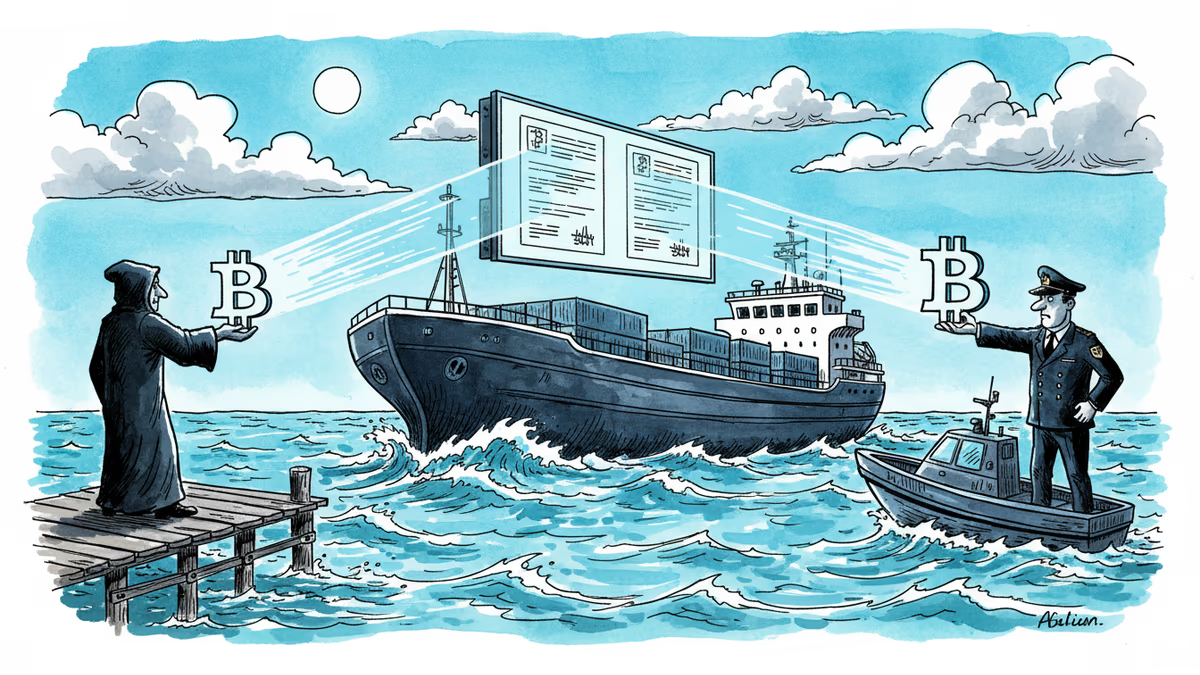
Fake Iran, Real Bitcoin: The Scam Preying on Hormuz Ships
Scammers posing as Iranian authorities are demanding bitcoin and tether from ships near the Strait of Hormuz—exploiting the fact that Iran already does exactly this.
The perfect scam doesn't invent a threat. It borrows one that already exists.
Somewhere near the Strait of Hormuz—the narrow chokepoint through which one-fifth of the world's oil and LNG passes every day—ship operators are receiving messages demanding bitcoin or tether as a "transit fee." Some are paying. And at least one vessel that paid may not have realized it was handing money to a fraudster, not the Iranian government. The problem: Iran has been making the same demand for real.
What's Actually Happening
On April 20, Greek maritime risk management firm MARISKS issued an alert to shipowners: scammers impersonating Iranian authorities were contacting shipping companies and demanding cryptocurrency payments—specifically bitcoin and tether (USDT)—for safe passage through the strait. Reuters was first to report the warning.
But the alert came with an uncomfortable caveat. Iranian authorities have, in fact, been requiring cryptocurrency payments from oil tankers to pass through the waterway. They've also been ordering ships to follow routes close to Iran's coastline for so-called inspections. The line between the real demand and the fraudulent one has become dangerously thin. At least one ship that came under Iranian fire may have already paid the scammers—believing it had settled with the actual Iranian government.
For ship operators, this creates a near-impossible verification problem. There is no official channel to confirm which message is legitimate. Both demand the same thing, in the same currency, through the same untraceable medium.
Why Crypto, Why Now
Iran's use of the Strait of Hormuz as geopolitical leverage is decades old. What's new is the payment method. Under sweeping international sanctions, Iran has been systematically cut off from dollar-based financial infrastructure. Cryptocurrency—pseudonymous, borderless, and difficult to freeze—has become a practical workaround.
That same utility, however, makes it a scammer's ideal tool. Crypto transactions are largely irreversible. Once funds are sent to a fraudulent wallet, recovery is nearly impossible. A shipping company that pays a scammer is still exposed to Iran's actual demands—and now has less capital to deal with them.
The structural genius of this scam is that it requires no deception about the nature of the threat. The threat is real. Only the recipient is fake.
Three Ways to Read This Story
For maritime and insurance industries, the implications are immediate. War risk insurance premiums in the region were already climbing before this scam emerged. Adding crypto fraud to the equation creates a new liability that most maritime insurance policies weren't written to cover. Expect legal disputes over whether payments to fraudsters constitute "loss" under existing war risk frameworks.
For cryptocurrency advocates and regulators, this is an inconvenient data point. Bitcoin and tether are being used simultaneously as tools of state coercion by a sanctioned government and as instruments of criminal fraud mimicking that coercion. The argument that crypto enables financial freedom looks different when the most prominent use cases in a given geography involve Iranian naval pressure and impersonation scams.
For geopolitical analysts, the deeper story is about how sanctions regimes create perverse incentives. By pushing Iran outside the conventional financial system, sanctions inadvertently pushed Iranian state demands into the same space that scammers occupy—anonymous, unverifiable, and irreversible. The policy designed to constrain Iran may have inadvertently handed it a tool that's almost impossible to police.
The Verification Problem Has No Easy Fix
The core challenge here isn't technical—it's epistemic. How does a ship's operator, under pressure in a contested waterway, verify the identity of the entity demanding payment in a currency designed to obscure identity? Blockchain analytics firms can sometimes trace wallets after the fact, but that's cold comfort when a vessel is already in Iranian territorial waters.
Some maritime security experts have suggested that shipping companies establish pre-verified communication channels with relevant authorities before entering the strait. But that assumes those authorities are willing to cooperate—and in Iran's case, that's a significant assumption.
Authors
Related Articles

China is restricting AI researchers and startup founders from traveling abroad as the U.S.-China AI performance gap narrows to just 2.7%. What Beijing's talent lockdown means for the global AI race.

US Space Command confirms Russia has deployed operational anti-satellite weapons tracking American spy satellites in low-Earth orbit. What does this mean for space security?
North Korean hackers used ChatGPT, Cursor, and AI web tools to steal $12M in crypto in 90 days—without knowing how to code. What this means for cybersecurity's future.
A small pro-Iran team is racking up millions of views with AI-generated Lego videos that mock Trump — and Americans are sharing them. What does that tell us about information warfare?
Thoughts
Share your thoughts on this article
Sign in to join the conversation