
The $10 Billion Backdoor: When Cost-Cutting Becomes National Risk
How private equity's efficiency drive created a cybersecurity nightmare that compromised 119 organizations and exposed the hidden cost of corporate cost-cutting.
119 Organizations. One Hidden Backdoor. Five Years.
In February 2021, software giant Ivanti discovered something that would redefine corporate cybersecurity nightmares. Chinese hackers hadn't just breached their subsidiary Pulse Secure—they'd planted a secret backdoor in the VPN software that dozens of companies and government agencies worldwide relied on for secure remote access.
The scope was staggering: 119 organizations compromised through a single point of failure. According to new Bloomberg reporting, the hackers exploited this backdoor to gain access to European and U.S. military contractors, with security firm Mandiant alerting Ivanti to the breach's devastating reach.
But here's what makes this story different: the backdoor wasn't just a technical failure. It was a business decision.
The PE Playbook: Efficiency at What Cost?
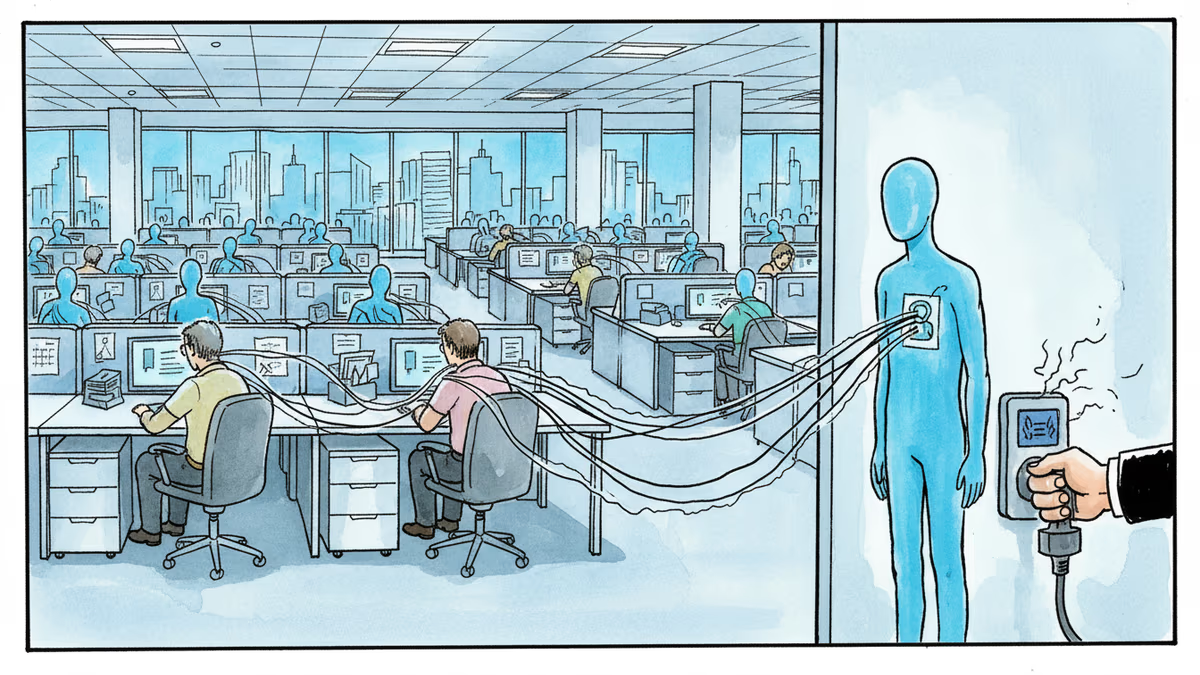
When private equity giant Clearlake Capital Group acquired Ivanti in 2017, they brought their standard playbook: streamline operations, cut redundancies, maximize returns. The strategy worked—for shareholders. For cybersecurity, it was catastrophic.
Bloomberg's investigation reveals rounds of cuts, particularly brutal ones in 2022, targeting employees with deep institutional knowledge of Ivanti's products and their security architecture. These weren't just layoffs—they were the systematic dismantling of the company's defensive capabilities.
The pattern isn't unique to Ivanti. Remote access provider Citrix followed an eerily similar trajectory after Elliott Investment Management and Vista Equity Partners acquired it in 2022. Large-scale layoffs followed by a string of cybersecurity incidents and critical flaws.
When 'Efficiency' Meets National Security
The consequences extended far beyond corporate networks. In early 2024, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued an unprecedented order: all federal agencies had 48 hours to disconnect their Ivanti VPN appliances. Hackers were actively exploiting vulnerabilities that Ivanti itself didn't even know existed.
This wasn't just another security patch—it was a national emergency response to a private company's structural failures.
Last year brought yet another critical flaw in Ivanti's Connect Secure product, with hackers exploiting it to breach corporate customers. The pattern was clear: this wasn't bad luck or sophisticated attackers. It was systematic vulnerability.
The Hidden Economics of Cybersecurity
Private equity's efficiency metrics work brilliantly for manufacturing or retail. Cut redundant staff, streamline processes, boost margins. But cybersecurity operates on different economics entirely.
Security expertise isn't just about individual knowledge—it's about institutional memory. The engineer who remembers why a particular code was written that way. The analyst who recognizes attack patterns from three years ago. The architect who understands the subtle interdependencies that aren't documented anywhere.
When you cut these people to improve quarterly numbers, you're not just reducing headcount. You're creating blind spots that can persist for years.
The Ripple Effect: Who's Really Paying?
The cost of Ivanti's efficiency drive wasn't borne by Clearlake Capital or Ivanti's shareholders. It was paid by the 119 organizations that trusted their VPN infrastructure, the government agencies forced into emergency disconnections, and the countless employees whose personal data may have been compromised.
This externalization of risk—where private gains come at the cost of public security—represents a fundamental market failure. The companies making cost-cutting decisions aren't the ones paying the full price of cybersecurity failures.
Authors
Related Articles

UK Visa Portal, a private immigration service mistaken for an official government site, has been exposing passport scans and selfies of over 100,000 applicants. The breach remains unpatched.
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
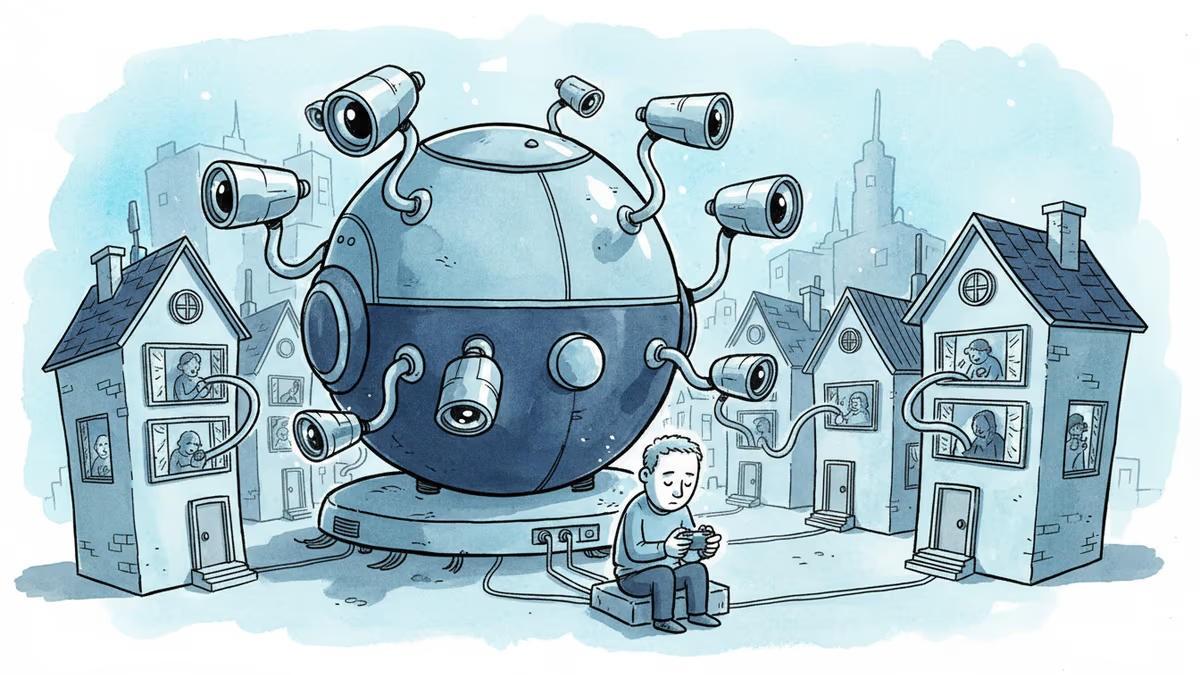
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
Thoughts
Share your thoughts on this article
Sign in to join the conversation