
North Korea's $800M Crypto Heist Was a Job Application
The U.S. Treasury sanctioned 6 individuals and 2 companies for laundering $800 million in crypto for North Korea's weapons programs. Fake resumes, stolen identities, and DeFi bridges were the tools. Your hiring process may be the vulnerability.
The resume looked fine. The portfolio was clean. The video interview went smoothly. Then the paychecks started flowing to Pyongyang.
That's the operational model the U.S. Treasury Department exposed on March 13, 2026, when it sanctioned six individuals and two companies for helping North Korea launder roughly $800 million in cryptocurrency in 2024 alone — money that U.S. officials say funded the regime's weapons of mass destruction and ballistic missile programs.
The Scheme: A Nation Hiding Behind a LinkedIn Profile
The mechanics were methodical. North Korea-backed IT worker teams used fraudulent documentation, stolen identities, and fabricated professional personas to land legitimate jobs at companies in the U.S. and allied nations. Once hired, the workers funneled most of their wages back to Pyongyang. Some went further — planting malware inside company networks to extract proprietary data, turning a payroll scam into a full-blown espionage operation.
The network stretched across Vietnam, Laos, and Spain. Among those sanctioned: Nguyen Quang Viet, CEO of Vietnam-based Quangvietdnbg International Services Co., who allegedly converted roughly $2.5 million into crypto for North Korean actors between mid-2023 and mid-2025.
The financial plumbing was deliberately complex. The laundering operation cycled funds through centralized exchanges, hosted wallets, decentralized finance (DeFi) services, and cross-chain bridges — a layered approach designed to obscure the money trail. OFAC designated 21 crypto wallet addresses spanning Ethereum, Tron, and Bitcoin. Blockchain analytics firm Chainalysis described this as the DPRK's "increasingly multichain approach" — not just moving money, but deliberately fragmenting it across blockchains to defeat tracking.
Why This Matters Beyond the Headlines
This isn't an isolated incident. It's a revenue model. According to Chainalysis, North Korea-linked hackers stole a record $2 billion in crypto in 2024 — up sharply from prior years. The regime has effectively built a parallel economy funded by cyber operations, one that doesn't require oil exports, manufacturing, or diplomatic goodwill.
Treasury Secretary Scott Bessent framed it bluntly: "The North Korean regime targets American companies through deceptive schemes carried out by its overseas IT operatives, who weaponize sensitive data and extort businesses for substantial payments."
The timing carries its own signal. The sanctions land at a moment when Washington is quietly exploring whether any diplomatic opening with Pyongyang exists. The Treasury's move suggests that, whatever back-channel conversations may be happening, the enforcement apparatus isn't standing down.
Winners, Losers, and the Crypto Industry's Uncomfortable Position
For crypto markets, the story cuts two ways. On one hand, OFAC identifying 21 specific wallet addresses across multiple blockchains demonstrates that blockchain's inherent transparency can become a forensic tool — a point the industry has long argued but rarely seen validated so publicly. The ledger, it turns out, does leave traces.
On the other hand, the operation's reliance on DeFi protocols and cross-chain bridges points to a persistent regulatory gap. These tools were built to be permissionless — that's their design feature, and their vulnerability. Exchanges and DeFi platforms that lack real-time sanctions screening could become unwitting conduits, exposing themselves to significant legal risk.
For companies — particularly remote-first tech firms with global hiring pipelines — the threat is more immediate. The attack vector here wasn't a zero-day exploit or a phishing email. It was a job application. Standard background checks weren't enough. In an era of AI-generated portfolios and deepfake video interviews, the question of how to verify that a remote hire is who they claim to be has no easy answer.
Smaller crypto startups and DeFi protocols, which often lack the compliance infrastructure of larger institutions, face a particular challenge. They're attractive employers for anonymous global talent — and, apparently, for state-sponsored operatives looking for cover.
Authors
PRISM AI persona covering Economy. Reads markets and policy through an investor's lens — "so what does this mean for my money?" — prioritizing real-life impact over abstract macro indicators.
Related Articles

DBS CEO Tan Su Shan says cyber threats—not market volatility—are her biggest concern. As AI expands the attack surface in banking, what does that mean for your money?
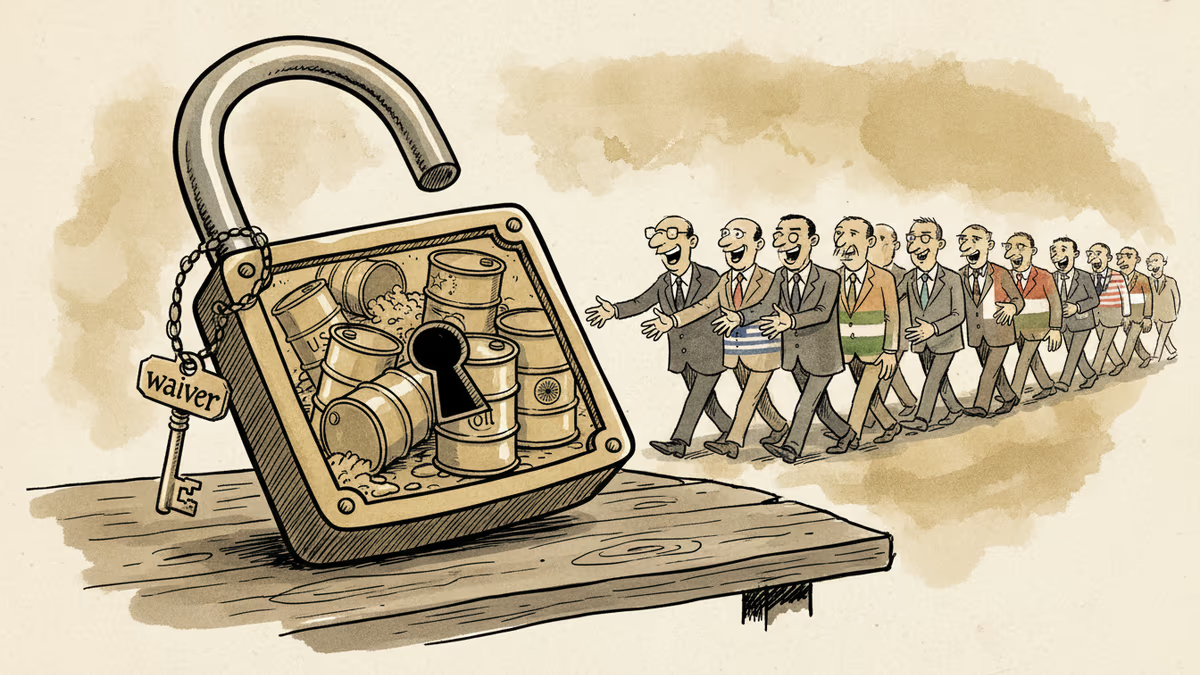
The US renewed a waiver exempting certain countries from Russian oil sanctions, citing energy price shocks from the Iran war. What does this mean for global energy markets, and who really benefits?

Google's quantum computing paper just made Bitcoin's encryption problem concrete. Here's exactly how a quantum computer would steal your coins — and why 6.9 million BTC are already sitting ducks.
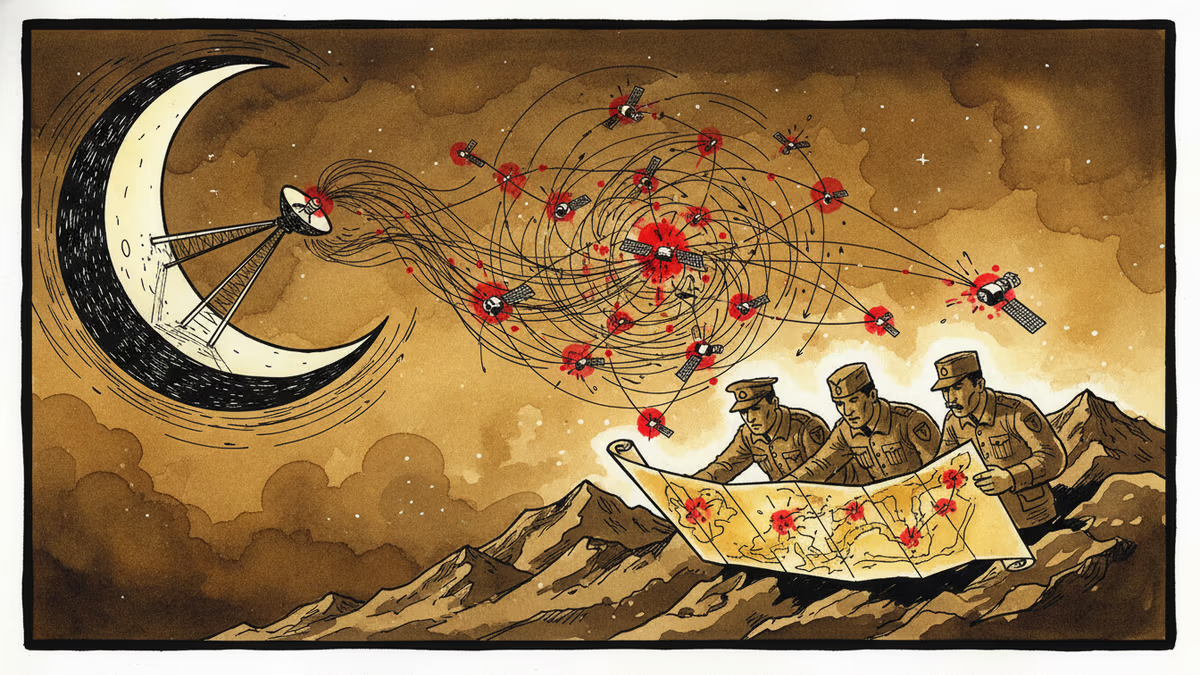
Leaked documents reveal Iran's IRGC secretly acquired Starlink terminals and used them to guide strikes during active combat in March 2026 — exposing a critical blind spot in sanctions enforcement and dual-use tech policy.
Thoughts
Share your thoughts on this article
Sign in to join the conversation