
When Password Managers Break Their Zero-Knowledge Promise
ETH Zurich researchers exposed critical flaws in major password managers' zero-knowledge claims, revealing that even security tools recommended by experts aren't bulletproof.
The $10,000 Question: Can We Trust Our Digital Safes?
For over a decade, cybersecurity experts have preached the same gospel: use a password manager. "Create unique, strong passwords for every account," they said. "It's the only practical way." Millions listened, trusting companies like Bitwarden, Dashlane, and LastPass with their most sensitive credentials.
But what happens when the safe isn't as secure as promised?
Researchers at ETH Zurich and USI Lugano just delivered a wake-up call. Their analysis of major password managers revealed that the industry's "zero-knowledge" promises—the guarantee that even the companies themselves can't access your passwords—are riddled with holes.
The Cracks in "Zero-Knowledge" Armor
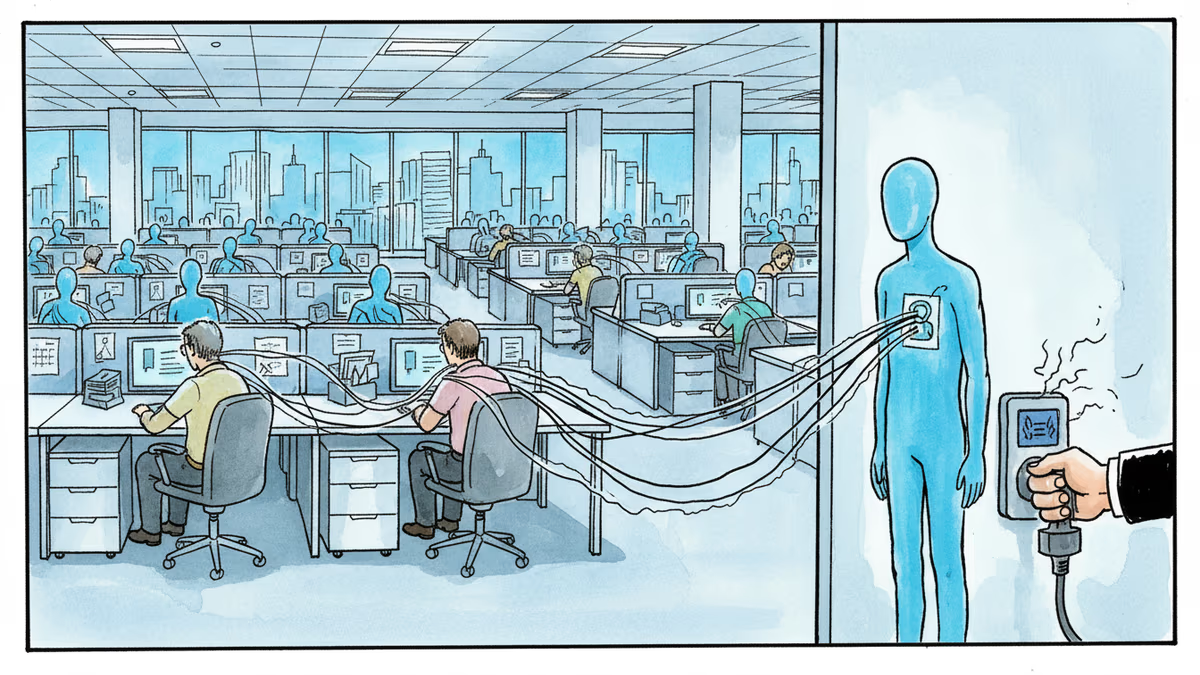
Password manager companies have built their reputations on a simple promise: your data is encrypted so thoroughly that even they can't see it. It's a compelling pitch in an era of data breaches and corporate surveillance.
Yet the researchers found they could often bypass these protections entirely. In some cases, they gained access to users' complete password "vaults." In others, they could modify stored credentials at will. The vulnerabilities weren't sophisticated exploits—they were relatively simple flaws that exposed the lack of rigorous security auditing in the industry.
The problems were particularly acute in key escrow systems, the features that allow password backup and recovery. These convenience features, designed to prevent users from being locked out of their accounts, became backdoors for potential attackers.
The Enterprise Dilemma: Convenience vs. Control
For businesses, this research creates a perfect storm of competing concerns. Companies have spent years training employees to use password managers, investing in enterprise licenses, and building security policies around these tools. Now they're facing uncomfortable questions about whether their chosen solutions actually deliver the security they promise.
The timing couldn't be worse. With remote work normalizing the use of personal devices for business tasks, password managers have become critical infrastructure. Yet the research suggests that even "enterprise-grade" solutions may have fundamental architectural flaws.
Some organizations are already reconsidering their approaches. Instead of relying solely on cloud-based password managers, they're exploring hybrid solutions that combine local storage with limited cloud synchronization—trading some convenience for potentially better security.
The Regulatory Reckoning Ahead
This research arrives as regulators worldwide are scrutinizing the cybersecurity industry's claims more closely. The European Union's NIS2 directive and similar regulations in other jurisdictions are placing greater liability on companies for security failures.
Password manager companies may soon face the same scrutiny that social media platforms and cloud providers have endured. The "zero-knowledge" marketing claims that once differentiated these services could become legal liabilities if they can't withstand technical scrutiny.
Authors
Related Articles
Okta CEO Todd McKinnon on why AI agents need identity management, the SaaSpocalypse threat, and why the kill switch might be the most important button in enterprise tech.

Iran and Israel are hacking civilian security cameras for military reconnaissance. How consumer surveillance devices became weapons of war.
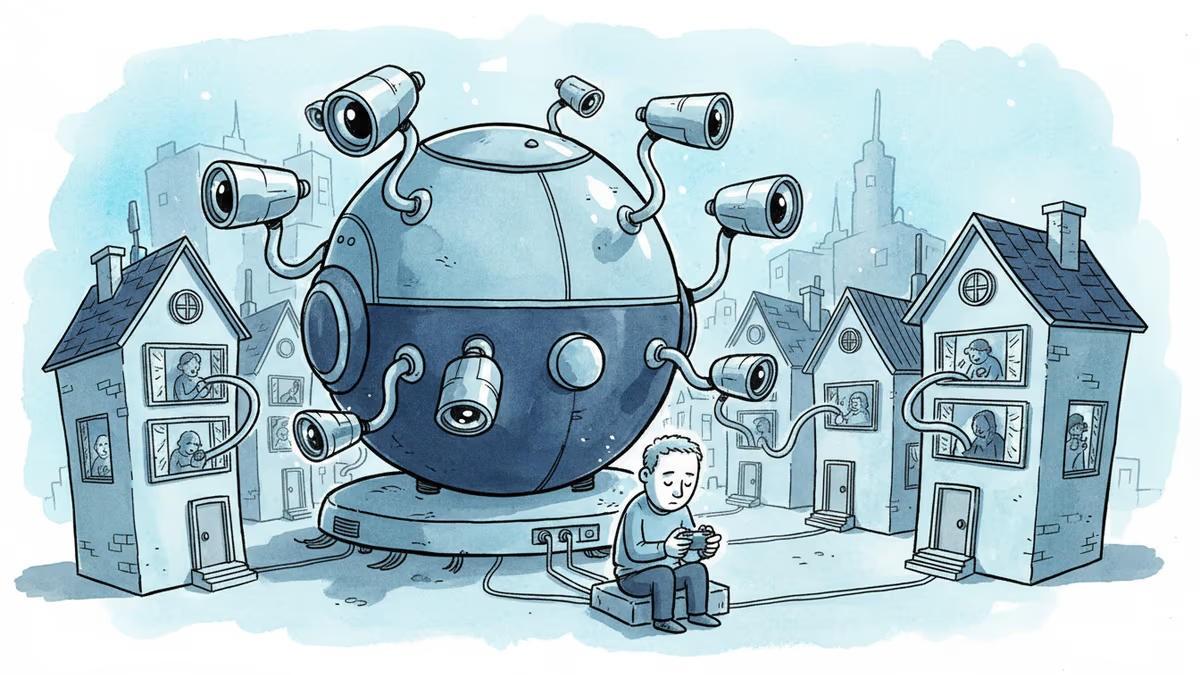
A security researcher discovered he could access 7,000 DJI robot vacuums and peek into strangers' homes. This Valentine's Day revelation exposes the hidden privacy risks of our smart home obsession.
CISA orders emergency patches for iOS vulnerabilities exploited by sophisticated Coruna toolkit, revealing how cybercriminals weaponize already-patched flaws
Thoughts
Share your thoughts on this article
Sign in to join the conversation