
North Korea Hacked a Golf Club. That's the Point.
Personal data of 100,000 members was stolen from a South Korean golf course in a suspected North Korean cyberattack. The real story isn't the golf club—it's the strategy.
A golf club doesn't sound like a national security concern. It should.
On April 26, South Korean police confirmed that Lee & Lee Country Club—a private golf course in Gapyeong county, roughly 55 kilometers northeast of Seoul—had been hacked, with personal data on approximately 100,000 members believed compromised. The stolen records include names, dates of birth, gender, user IDs, passwords, phone numbers, email addresses, and home addresses. The kind of data that, assembled together, can dismantle someone's financial life.
But the detail that changes everything: police didn't discover this breach because a victim complained. They found it while already investigating major North Korean hacking groups. The golf club's server, investigators believe, was infected with malware distributed by a state-linked hacking organization.
Not a Random Attack—A Pattern
To understand why this matters, consider the scale of what South Korea is up against. According to the country's 2024 defense white paper, approximately 8,400 hackers operate under the direction of North Korean state authorities. These aren't opportunistic criminals. They are organized, funded, and mission-driven—tasked with generating foreign currency, stealing military intelligence, and, increasingly, harvesting civilian data at scale.
U.S. officials have estimated that North Korea likely stole more than $2 billion in cryptocurrency in a single year. Britain has publicly labeled the country a "major" cyber threat. A Naver- and Google-ad-exploiting malware campaign linked to North Korean actors was reported just months ago.
Against that backdrop, a golf course breach looks less like a crime of opportunity and more like deliberate targeting logic. Golf club members in South Korea tend to skew wealthy—high-net-worth individuals whose financial credentials, once harvested, become premium raw material for fraud, spear-phishing, or identity theft. Meanwhile, private leisure facilities operate with a fraction of the cybersecurity infrastructure that banks or government agencies maintain. They are, in the language of security professionals, soft targets.
The suspected approach—malware infection of a web server—is consistent with techniques attributed to Lazarus Group and affiliated North Korean cyber units, which have repeatedly used legitimate-looking infrastructure to establish footholds before moving laterally toward higher-value targets.
What the 100,000 Don't Know
For the people whose data was taken, the immediate threat is concrete: credential stuffing attacks on other accounts, targeted phishing calls, potential identity fraud. The combination of home address, date of birth, phone number, and password is essentially a skeleton key.
But the deeper problem is invisibility. Victims have no way of knowing where their data is now, who has purchased it, or when it will be used. Stolen data doesn't expire. It circulates through dark web marketplaces, gets bundled into larger datasets, and resurfaces months or years later in entirely different attack contexts. The harm from a breach like this is diffuse, delayed, and nearly impossible to trace back to the source.
Cybersecurity experts have long warned that mid-sized private businesses—golf clubs, medical clinics, regional retailers—represent the most underprotected layer of a country's digital infrastructure. They collect significant personal data, they lack dedicated security teams, and they rarely appear on anyone's threat radar until something goes wrong.
It's worth noting a caveat: attribution in cyberattacks is genuinely difficult. Investigators believe the malware matches patterns associated with a North Korean group, but "believed to be" is doing real work in that sentence. Malware code can be copied, spoofed, or deliberately planted to mislead. The South Korean government has strong political incentives to frame breaches as state-sponsored—and that doesn't mean they're wrong, but it warrants scrutiny.
The Bigger Question for Governments and Industry
This incident sits at the intersection of two trends that security analysts have been tracking closely. First, the democratization of cyberattack targets: state-level actors are no longer focused exclusively on military or governmental systems. Civilian infrastructure—hospitals, utilities, leisure businesses—is now fair game, both as an end in itself and as a stepping stone. Second, the accountability gap: when a nation-state attacks a private business, who is responsible for the defense? The company that couldn't afford enterprise-grade security? The government that didn't mandate it? The industry that sold inadequate solutions?
South Korea has been grappling with this question for years, given its unique threat environment. But it's a question that every country with a significant North Korean cyber exposure—which increasingly means every country with a financial sector—needs to answer.
This content is AI-generated based on source articles. While we strive for accuracy, errors may occur. We recommend verifying with the original source.
Related Articles

Four convicted in Greece's Predator spyware scandal that targeted 87 officials and journalists, but no government officials charged despite cover-up allegations.
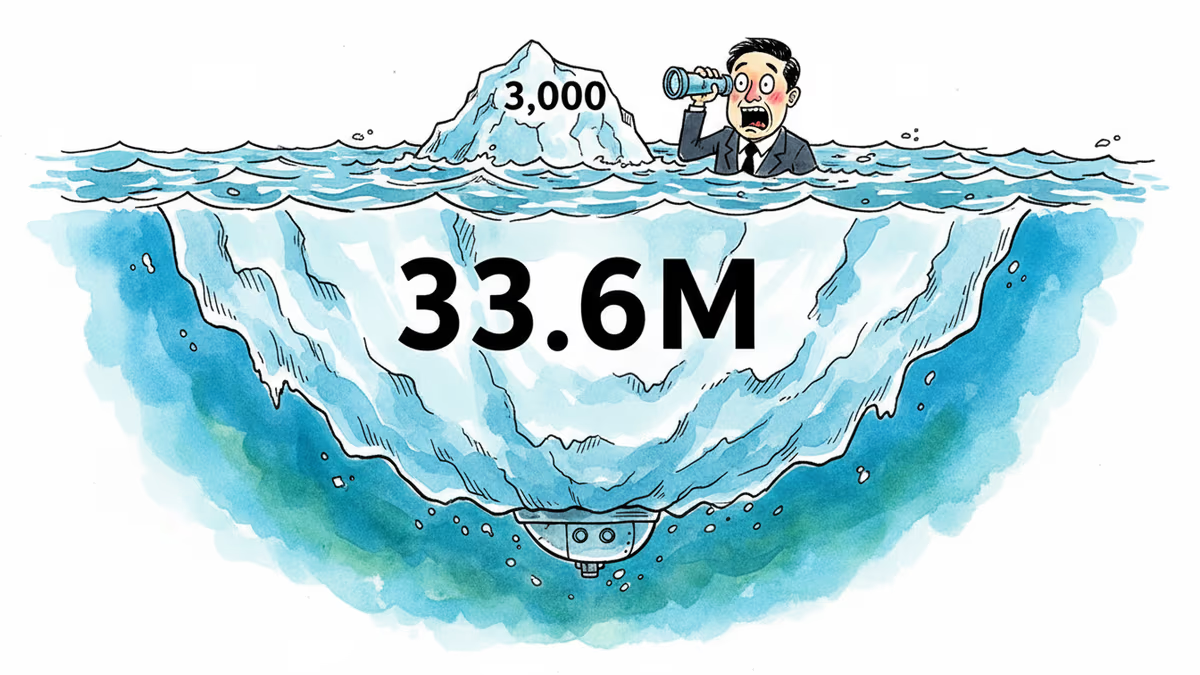
South Korea's investigation reveals Coupang's data breach affected 33.6 million accounts, not 3,000 as initially claimed. A case study in corporate transparency and digital trust.

South Korean government probe reveals Coupang's data breach affected 33.6 million accounts, not 3,000 as initially claimed, exposing massive transparency issues.

In January 2026, Chinese state security issued a major warning regarding 'honey trap' risks in the defense and technology sectors following a blackmail case.
Thoughts
Share your thoughts on this article
Sign in to join the conversation